Security
Axios npm Hijacking: How Fake Teams Error Fix Led to Maintainer Account Takeover

In a recent incident, the developers behind the widely-used Axios HTTP client detailed how one of their team members fell victim to a social engineering attack orchestrated by North Korean hackers.
This attack involved compromising a maintainer account to introduce two harmful versions of Axios (1.14.1 and 0.30.4) on the npm package registry, initiating a supply chain attack.
These malicious releases included a dependency called plain-crypto-js, which installed a remote access trojan (RAT) on macOS, Windows, and Linux operating systems.
Although the malicious versions were swiftly removed after being available for three hours, any systems that installed them during that period are considered compromised, necessitating a rotation of all credentials and authentication keys.
The Axios team took immediate action by wiping affected systems, resetting all credentials, and implementing measures to prevent similar incidents in the future.
Google’s Threat Intelligence Group has connected this attack to North Korean threat actors identified as UNC1069.
“GTIG attributes this activity to UNC1069, a financially motivated North Korea-nexus threat actor active since at least 2018, based on the use of WAVESHAPER.V2, an updated version of WAVESHAPER previously utilized by this threat actor,” explained Google.
“Further, analysis of infrastructure artifacts used in this attack shows overlaps with infrastructure used by UNC1069 in past activities.”
Targeted in a Social Engineering Campaign
According to the post-mortem analysis, the compromise began with a targeted social engineering attack on Jason Saayman, the lead maintainer of the project.
The attackers impersonated a legitimate company, replicated its branding and founders’ images, and lured the maintainer into a Slack workspace designed to mimic the company. The Slack server featured realistic channels, staged activity, and fake profiles posing as employees and other open-source maintainers.
“They then invited me to a real slack workspace. this workspace was branded to the companies ci and named in a plausible manner,” stated Saayman in the post-mortem report.
“The slack was thought out very well, they had channels where they were sharing linked-in posts, the linked in posts i presume just went to the real companys account but it was super convincing etc. they even had what i presume were fake profiles of the team of the company but also number of other oss maintainers.”
The attackers arranged a meeting on Microsoft Teams that seemed to involve multiple participants.
During the call, a technical error message appeared, indicating that something on the system needed updating, leading the maintainer to install a Teams update to resolve the issue. However, this purported update was actually a RAT malware that granted threat actors remote access to the maintainer’s device, enabling them to acquire the npm credentials for the Axios project.
Other maintainers also reported similar social engineering attacks, where the threat actors attempted to persuade them to install a fake Microsoft Teams SDK update.
This attack bears resemblance to a ClickFix attack, where victims are presented with a fabricated error message and instructed to follow steps that deploy malware.
Additionally, this attack echoes previous campaigns identified by Google’s threat intelligence teams, where North Korean threat actors UNC1069 employed the same tactics to target cryptocurrency firms.
In prior campaigns associated with UNC1069, the threat actors deployed additional payloads on devices, such as backdoors, downloaders, and infostealers designed to pilfer credentials, browser data, session tokens, and other sensitive information.
Given that the attackers gained access to authenticated sessions, multi-factor authentication (MFA) protections were effectively circumvented, granting access to accounts without the need for re-authentication.
The Axios maintainers affirmed that the attack did not involve altering the project’s source code but instead relied on injecting a malicious dependency into otherwise legitimate releases.
Pelle Wessman, a maintainer of various open-source projects including the popular Mocha framework, disclosed on LinkedIn that he was also targeted in the same campaign and shared a screenshot of a fake RTC connection error message used to deceive targets into installing malware.
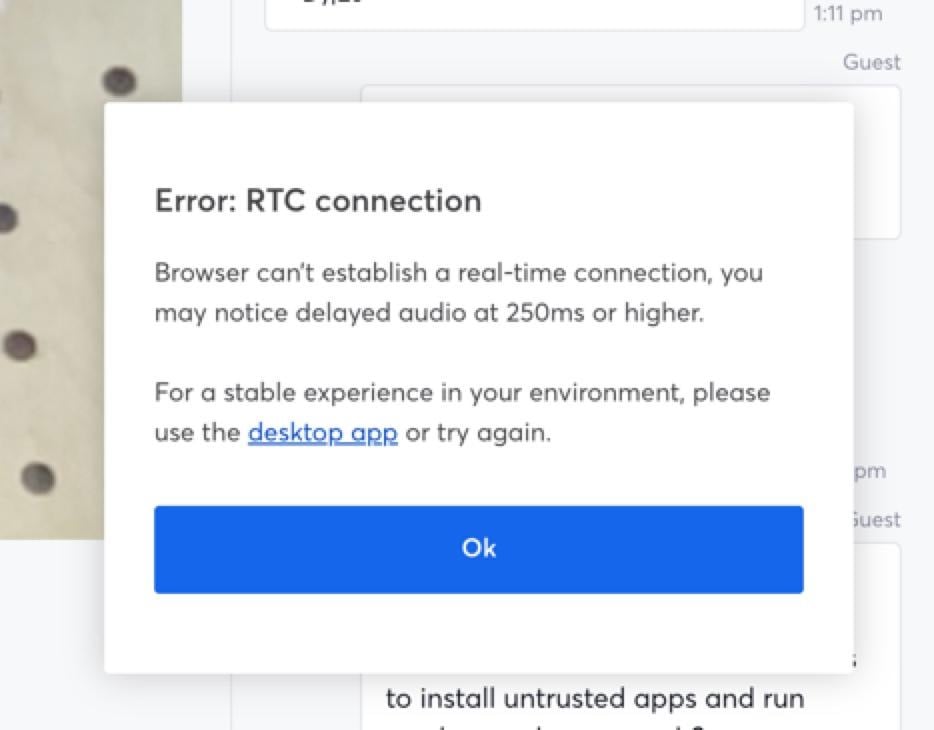
Source: Pelle Wessman
When Wessman declined to install the application, the threat actors attempted to convince him to execute a Curl command.
“When it became clear that I wouldn’t run the app and we had chatted back and forth on website and chat app they made one final desperate attempt and tried to get me to run a curl command that would download and run something, then when I refused they went dark and deleted all conversations,” Wessman explained.
Cybersecurity firm Socket also confirmed that this was a coordinated campaign targeting maintainers of popular Node.js projects.
Several developers, including maintainers of widely-used packages and Node.js core contributors, reported receiving similar outreach messages and invitations to Slack workspaces operated by the attackers.
Socket highlighted that these maintainers oversee packages with billions of weekly downloads, indicating that the threat actors focused on impactful projects.
“Since we published our initial analysis of the axios compromise, a deep dive into its hidden blast radius, and a report on the maintainer confirming it was social engineering, maintainers across the Node.js ecosystem have come out of the woodwork to report that they were targeted by the same social engineering campaign,” Socket stated.
“The accounts now span some of the most widely depended-upon packages in the npm registry and Node.js core itself, and together they confirm that axios was not a one-off target. It was part of a coordinated, scalable attack pattern aimed at high-trust, high-impact open source maintainers.”
Socket mentioned that the campaign followed a consistent pattern, with the threat actors initiating contact through platforms like LinkedIn or Slack before inviting recipients into private or semi-private workspaces.
After establishing rapport with the target, the threat actors scheduled video calls, some of which were conducted through sites mimicking Microsoft Teams and other platforms.
During these calls, targets encountered an error message prompting them to install “native” desktop software or run commands to address technical issues.
The uniform approach employed against all targets during the same timeframe suggests a coordinated campaign rather than isolated attacks.
Researchers at Socket emphasized that these types of supply chain attacks are increasingly prevalent, with attackers now targeting widely-used packages to generate widespread impact.

Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple6 months ago
Apple6 months agoMeta discontinues Messenger apps for Windows and macOS
































