

Fake OpenAI Repository on Hugging Face Distributes Infostealer Malware A deceptive repository on the Hugging Face platform, masquerading as OpenAI’s...



Anthropic’s new research-preview model represents a significant advancement in AI capabilities for cybersecurity. The model, named Claude Mythos Preview, has demonstrated exceptional proficiency in finding and...
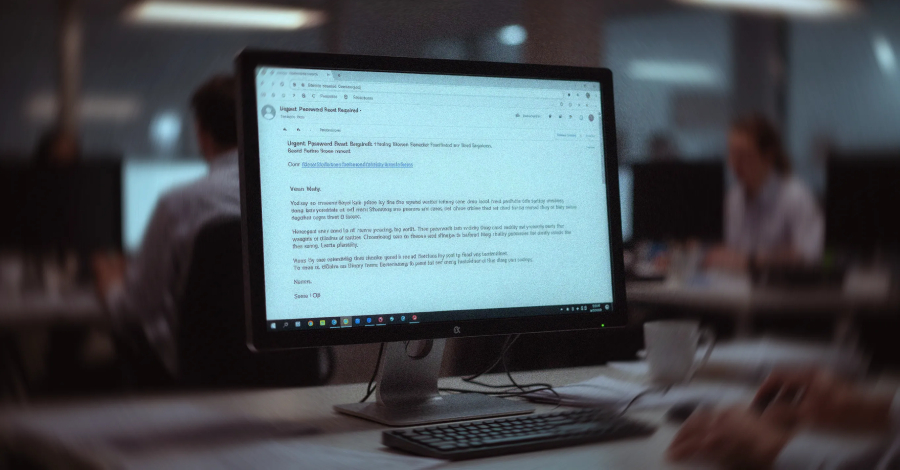

An Overview of the VENOMOUS#HELPER Phishing Campaign A sophisticated phishing campaign, known as VENOMOUS#HELPER, has been actively targeting various organizations since April 2025. This campaign utilizes...


Confirmation has been provided by NVIDIA to BleepingComputer regarding a data breach that has impacted users of GeForce NOW in Armenia. The tech giant stated that...



If your organisation runs quarterly vulnerability scans and calls it penetration testing, you are not alone. According to a 2025 SANS Institute survey, over 60% of...



The flaws, tracked as CVE-2026-20014 and CVE-2026-20015, allow an attacker to execute arbitrary code remotely, leading to potential system compromise. The vulnerabilities exist due to improper...



Recently, the ShinyHunters group targeted education technology giant Instructure once again, this time exploiting a vulnerability to deface Canvas login portals for numerous colleges and universities....



The Significance of Cyber Storage Resilience in Enterprise Security Recent surveys conducted by The Register / Blocks & Files among large enterprises reveal a growing trend...


The Recent Data Breach and Outage of Canvas Learning Management Platform Canvas, the popular learning management platform owned by Instructure, is currently experiencing an outage following...



The Iranian state-sponsored hacking group known as MuddyWater (aka Mango Sandstorm, Seedworm, and Static Kitten) has been attributed to a ransomware attack in what has been...
Subscribe to our weekly newsletter below and never miss the latest News or an exclusive offer.