Security
Urgent Warning: CISA Directs Federal Agencies to Address Critical Gogs RCE Vulnerability Targeted in Zero-Day Exploits

The Urgent Need to Secure Government Systems Against Gogs Vulnerability
Recent orders from the U.S. Cybersecurity and Infrastructure Security Agency (CISA) have highlighted the critical importance of securing government systems against a severe Gogs vulnerability that has been exploited in zero-day attacks.
Gogs, designed as an alternative to GitLab or GitHub Enterprise and written in Go, has become a popular platform for online collaboration. However, a high-severity remote code execution (RCE) security flaw, tracked as CVE-2025-8110, has raised significant concerns.
This vulnerability, originating from a path traversal weakness in the PutContents API, allows authenticated attackers to bypass previously patched RCE vulnerabilities by overwriting files outside the repository through symbolic links.

Exploiting this flaw enables threat actors to create repositories with symbolic links to sensitive system files, allowing them to execute arbitrary commands by overwriting Git configuration files.
Discovery of this vulnerability by Wiz Research during a malware investigation in July prompted the release of patches by Gogs maintainers in response to Wiz’s report. However, a second wave of attacks targeting this vulnerability as a zero-day occurred shortly after.
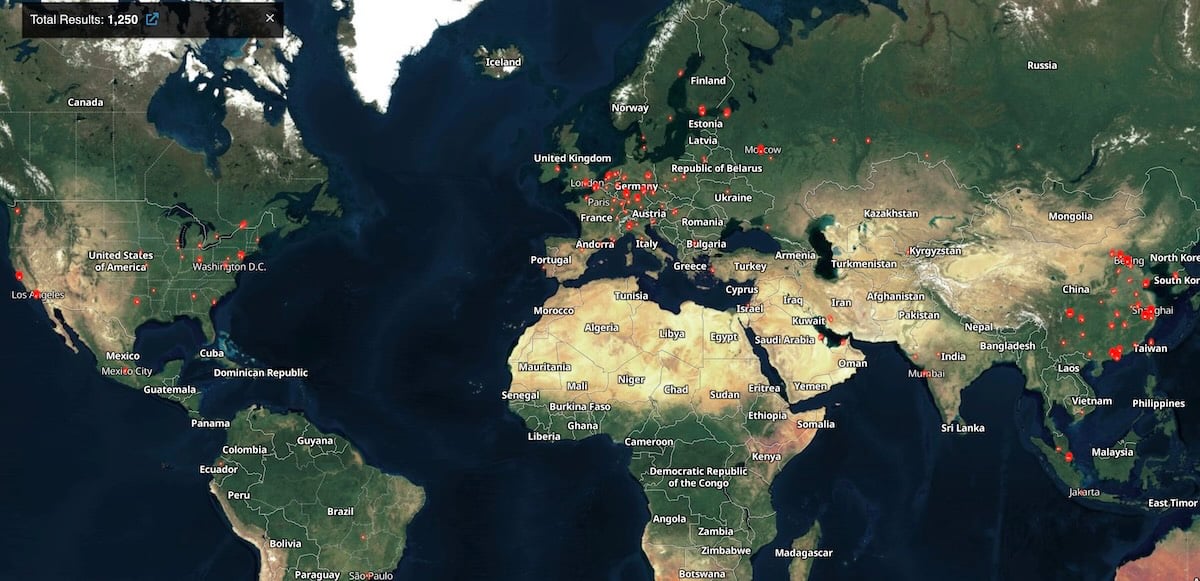
Subsequent investigations by Wiz Research revealed over 1,400 exposed Gogs servers, with a significant number showing signs of compromise. CISA has confirmed the severity of the issue and mandated that Federal Civilian Executive Branch (FCEB) agencies patch their systems by February 2, 2026.
These agencies, including prominent governmental bodies like the Department of Energy and the Department of Homeland Security, must take immediate action to mitigate the risks posed by this vulnerability.
CISA’s warning emphasizes the critical nature of this vulnerability, urging agencies to follow vendor instructions for mitigation or discontinue product usage if necessary. Additionally, Gogs users are advised to enhance security measures by disabling open registration and limiting server access.
Administrators should remain vigilant for signs of compromise, such as suspicious use of the PutContents API and repositories with randomly generated names created during the attack waves.

Enhance your team’s security practices with our comprehensive guide on secrets management. Download the cheat sheet now to streamline your security protocols.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS































