Security
Uncovering the Dangers of the Latest OAuth Phishing Attack

Unveiling the Dangers of the ConsentFix Attack Technique
In the realm of cybersecurity, new threats are constantly emerging. In December, the Push Security research team encountered a novel attack technique known as ConsentFix. This technique, a fusion of ClickFix-style social engineering and OAuth consent phishing, posed a significant risk to Microsoft accounts.
The attack was widespread, with the malicious payload injected into numerous compromised websites. This large-scale campaign was swiftly detected across multiple customer estates.
The response from the cybersecurity community to ConsentFix was swift and commendable. Security researchers, including John Hammond, Microsoft, Glueck Kanja, and others, shared insights and recommendations to combat this evolving threat.
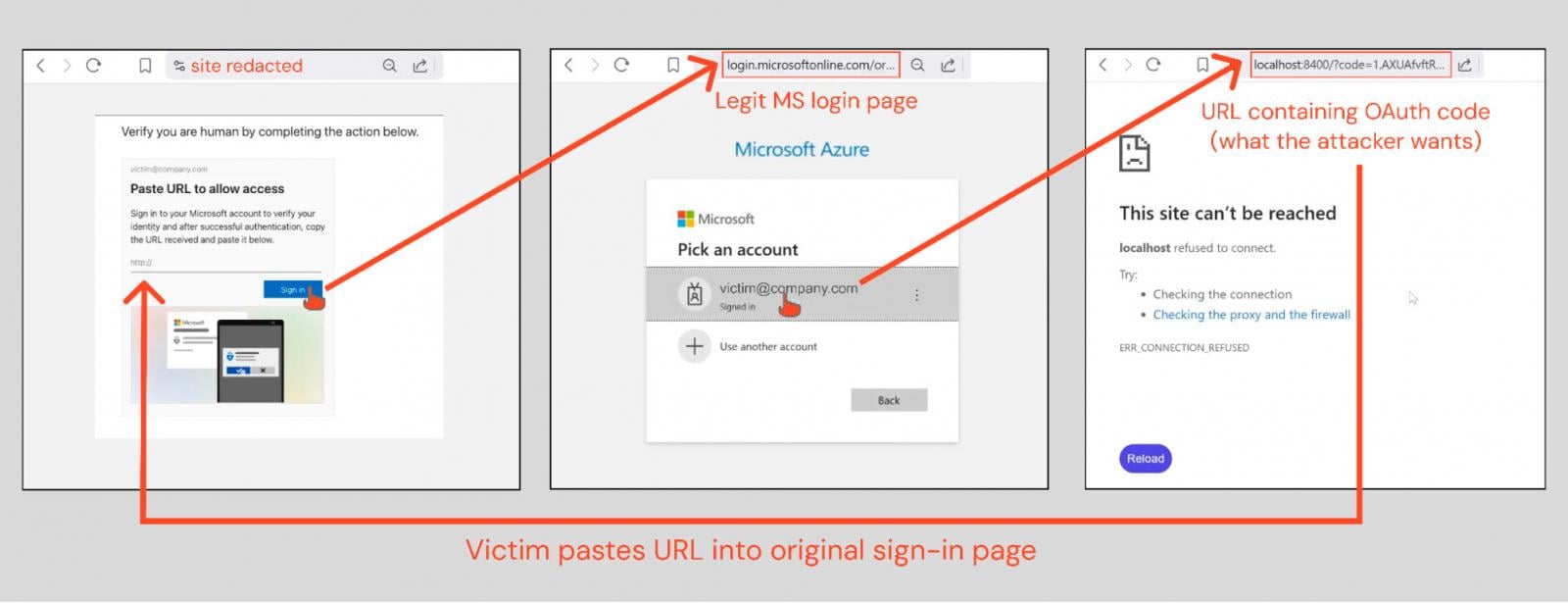
ConsentFix operates by tricking victims into sharing an OAuth authorization code with attackers through a phishing page. By exploiting OAuth, attackers can circumvent traditional authentication methods, such as passwords and MFA, gaining unauthorized access to accounts.
While OAuth abuse attacks are not new, ConsentFix represents a significant advancement in the exploitation of this method. It targets first-party Microsoft apps that are not subject to the same restrictions as third-party applications, making detection and response more challenging.
The Perils of ConsentFix
Unlike conventional OAuth attacks, ConsentFix allows attackers to target a wider range of applications, posing challenges for detection and response mechanisms. This technique:
-
Targets first-party Microsoft apps that are pre-consented in every tenant, bypassing admin approval requirements.
-
Utilizes legacy scopes and Conditional Access policy exclusions to evade detection.
The nature of ConsentFix makes it difficult for traditional security controls to thwart the attack. Default logging may not capture the necessary information, and conditional access policy exclusions can render existing security measures ineffective.
The evolving landscape of cybersecurity demands a proactive approach to combatting threats like ConsentFix. Security teams must prioritize monitoring controls and mitigation strategies to safeguard Microsoft environments.
Latest Developments in the Campaign
Further investigation has revealed potential links between the ConsentFix campaign and Russian state-affiliated APT29. The sophisticated tactics employed in this attack underscore the need for advanced detection and response capabilities.
The community response to ConsentFix has been instrumental in raising awareness and sharing best practices. Security researchers, including John Hammond, have released enhanced versions of the technique, highlighting the need for continuous vigilance.
Enhancing Security Measures
To combat evolving threats like ConsentFix, organizations must adopt a holistic approach to browser-based security. Traditional security tools may prove inadequate in detecting and blocking such attacks, necessitating a shift towards behavioral threat detection controls.
By leveraging deep browser telemetry and real-time monitoring, organizations can enhance their defense mechanisms against browser-based attacks. Initiatives like the Elastic detection rules for ConsentFix and guidance from Glueck Kanja offer valuable insights for bolstering security postures.
As the cybersecurity landscape continues to evolve, staying ahead of emerging threats like ConsentFix is paramount. By embracing innovative detection technologies and proactive security measures, organizations can mitigate the risks posed by sophisticated attack techniques.
Protecting against modern threats requires a proactive and multifaceted approach. By staying informed, leveraging community resources, and implementing robust security measures, organizations can safeguard their digital assets against the ever-evolving threat landscape.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS






























