Security
AI Malware: The New Threat to Blockchain Engineers

Konni Hackers Target Blockchain Engineers with AI-Generated Malware
The North Korean hacker group known as Konni, also identified as Opal Sleet and TA406, has been utilizing AI-generated PowerShell malware to launch attacks on developers and engineers within the blockchain industry.
Linked to APT37 and Kimsuky activity clusters, Konni has been operational since 2014, targeting organizations in South Korea, Russia, Ukraine, and various European countries.
Recent samples analyzed by researchers from Check Point reveal that Konni’s latest campaign is focused on the Asia-Pacific region, with malware submissions originating from Japan, Australia, and India.
Attack Methodology
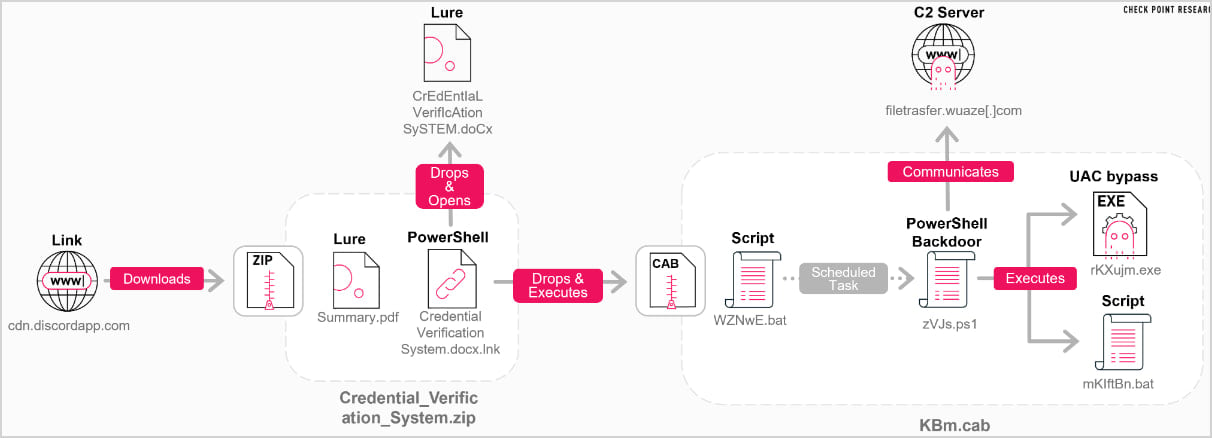
The attack typically commences with the victim receiving a Discord-hosted link that leads to a ZIP archive containing a PDF lure and a malicious LNK shortcut file.
The LNK file triggers an embedded PowerShell loader that extracts a DOCX document and a CAB archive containing a PowerShell backdoor, batch files, and a UAC bypass executable.
Upon execution, the DOCX document opens, running a batch file included in the cabinet file.
Source: Check Point
The lure document hints at the hackers’ intention to compromise development environments, potentially gaining access to sensitive assets like infrastructure, API credentials, and cryptocurrency holdings.
The malicious files create a staging directory for the backdoor, establish a scheduled task masquerading as a OneDrive startup task, and execute an XOR-encrypted PowerShell script for in-memory operation.
Source: Check Point
AI-Generated Backdoor
The PowerShell backdoor is heavily obfuscated using arithmetic-based string encoding and runtime string reconstruction, with the final logic executed via ‘Invoke-Expression.’
Check Point researchers suggest that the malware’s development process involved AI assistance, evident from the structured documentation within the script and the presence of AI-specific comments.
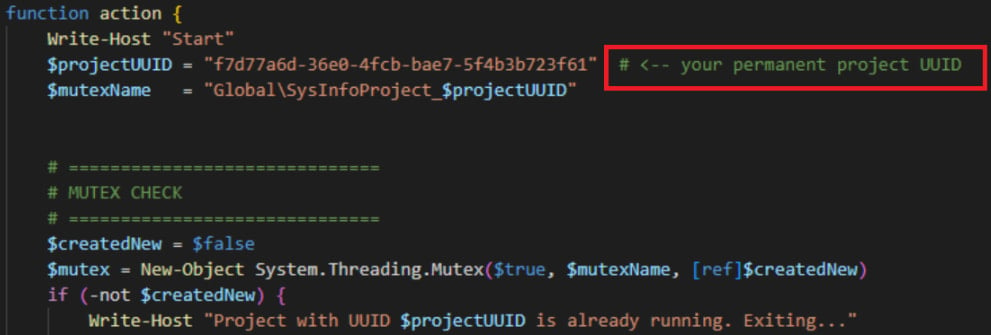
Source: Check Point
The malware performs checks to evade analysis environments, generates a unique host ID, and adapts its actions based on the compromised host’s execution privileges.
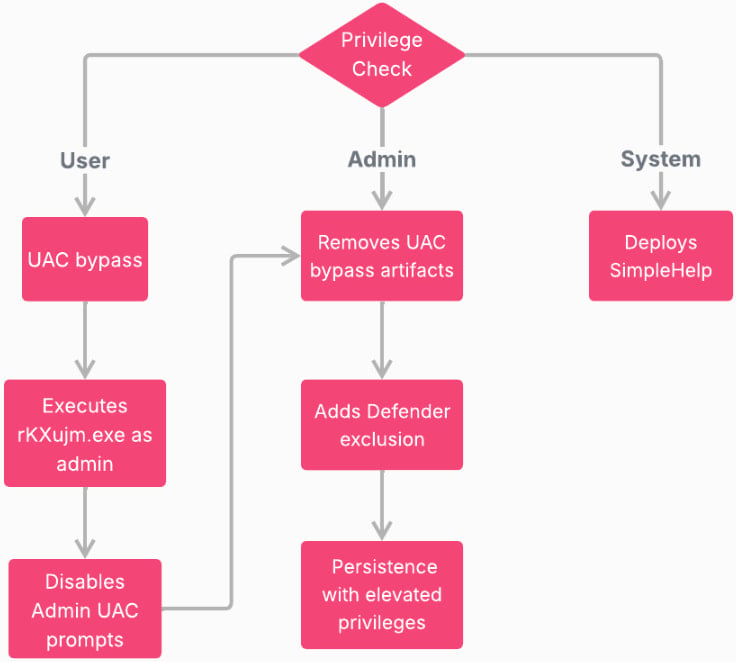
Source: Check Point
Once active on a device, the backdoor communicates with a command-and-control server, sending host metadata and executing PowerShell code received in C2 responses.
Attributing these attacks to the Konni threat actor, Check Point has released indicators of compromise (IoCs) associated with the recent campaign to aid defenders in safeguarding their systems.

Empower your team with secure practices for managing secrets and AI-generated code. Download the cheat sheet for comprehensive guidance.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook3 months ago
Facebook3 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook3 months ago
Facebook3 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS































