Security
Apple Enhances Security Protocols in macOS Terminal to Combat ClickFix Attacks
Apple Enhances macOS Security with New Terminal Warning Feature
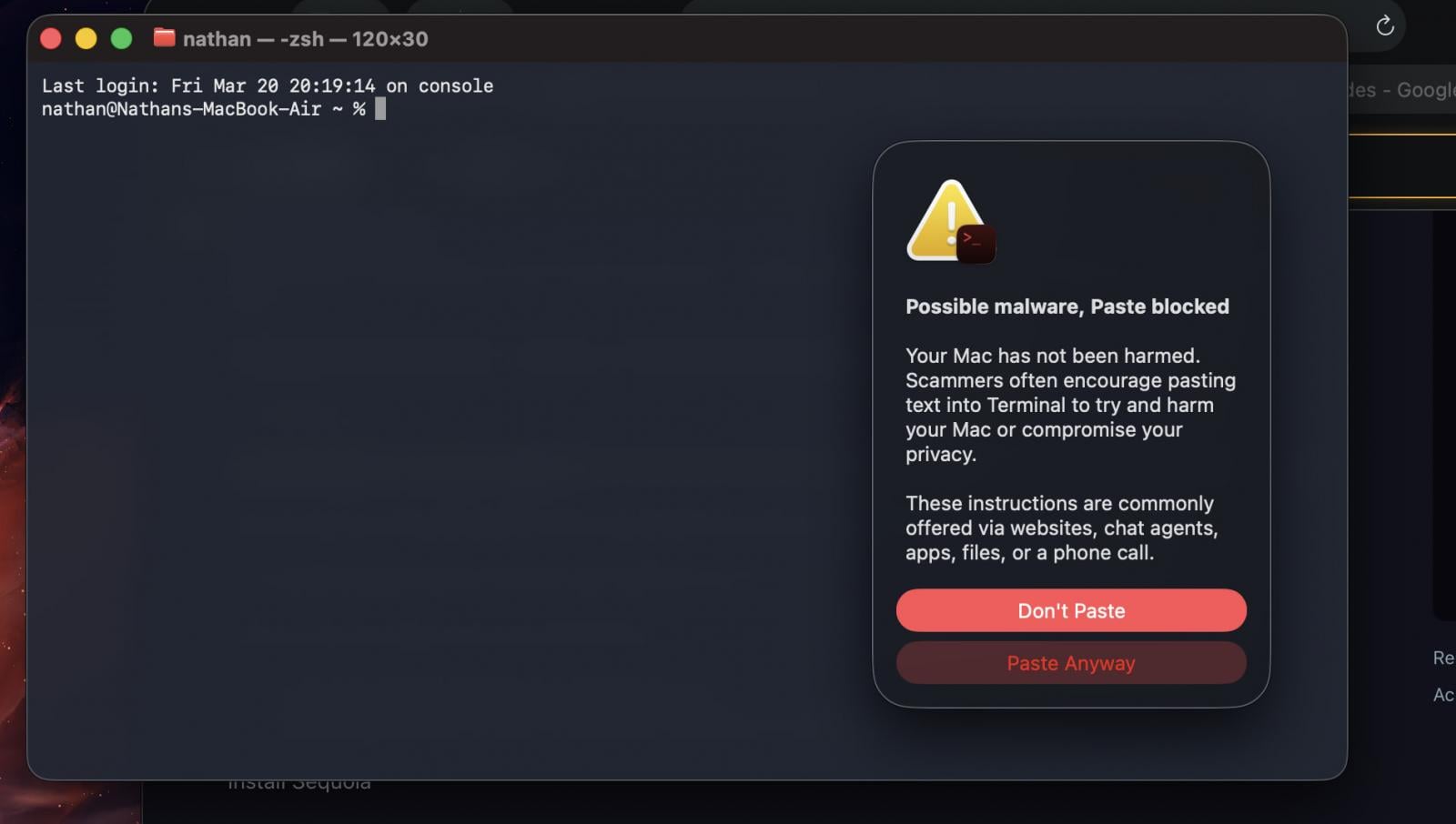
Apple has recently introduced an innovative security feature in macOS Tahoe 26.4 to protect users from potential cyber threats. The new mechanism aims to prevent ClickFix attacks by blocking the execution of harmful commands in Terminal and alerting users about possible risks.
ClickFix attacks involve social engineering tactics where users are tricked into pasting malicious commands into the command line interface under false pretenses. This technique bypasses existing security measures, allowing malware to infiltrate the system undetected.
To combat this growing threat, Apple’s latest macOS version now delays the execution of suspicious commands in Terminal when pasted by the user. A warning message is displayed, informing users about the associated risks and advising caution.
Source: Reddit
Users are encouraged to exercise vigilance when copying and pasting commands, especially from untrusted sources. They have the option to ignore the warning and proceed with the action, but it is advisable only if they fully understand the implications of the command.
Although Apple has not released official documentation regarding this new warning system, user reports indicate that alerts are triggered when commands are copied from Safari and pasted into Terminal.
It is worth noting that the warning prompts may only appear once per session, as some users have observed no alerts when testing potentially harmful commands. This suggests that the system may analyze the commands before issuing a warning.
BleepingComputer has reached out to Apple for further clarification on this security feature and will update accordingly.
As a precaution against ClickFix attacks, users across all operating systems are advised to refrain from executing commands they do not fully comprehend. While Apple’s new alerts provide an added layer of protection, users should not rely solely on them, as the criteria for determining command risk remain unspecified.

Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS