Security
ArrayOS AG VPN Vulnerability: How Hackers are Using it to Install Webshells

Exploitation of Array AG Series VPN Flaw by Hackers to Plant Webshells
Cybercriminals have been taking advantage of a command injection vulnerability found in Array AG Series VPN devices to insert webshells and establish unauthorized users.
Array Networks addressed the vulnerability in a security update released in May; however, they have not assigned it an identifier, making it challenging to monitor and manage patching.
A warning from Japan’s Computer Emergency and Response Team (CERT) highlights that attackers have been leveraging this vulnerability since at least August in targeted attacks against organizations in Japan.
According to the advisory, the attacks are traced back to the IP address 194.233.100[.]138, which is also utilized for communication purposes.
The bulletin states, “In the incidents confirmed by JPCERT/CC, a command was executed attempting to place a PHP webshell file in the path /ca/aproxy/webapp/.”
The vulnerability affects ArrayOS AG 9.4.5.8 and earlier versions, including AG Series hardware and virtual appliances with the ‘DesktopDirect’ remote access feature enabled.
JPCERT mentions that Array OS version 9.4.5.9 resolves the issue and provides the following workaround options if immediate updating is not feasible:
- Disable all DesktopDirect services if the feature is not in use
- Implement URL filtering to block access to URLs containing a semicolon
The Array Networks AG Series comprises secure access gateways that depend on SSL VPNs to establish encrypted tunnels for secure remote access to corporate networks, applications, desktops, and cloud resources.
These gateways are typically employed by large enterprises and organizations to facilitate remote or mobile work.
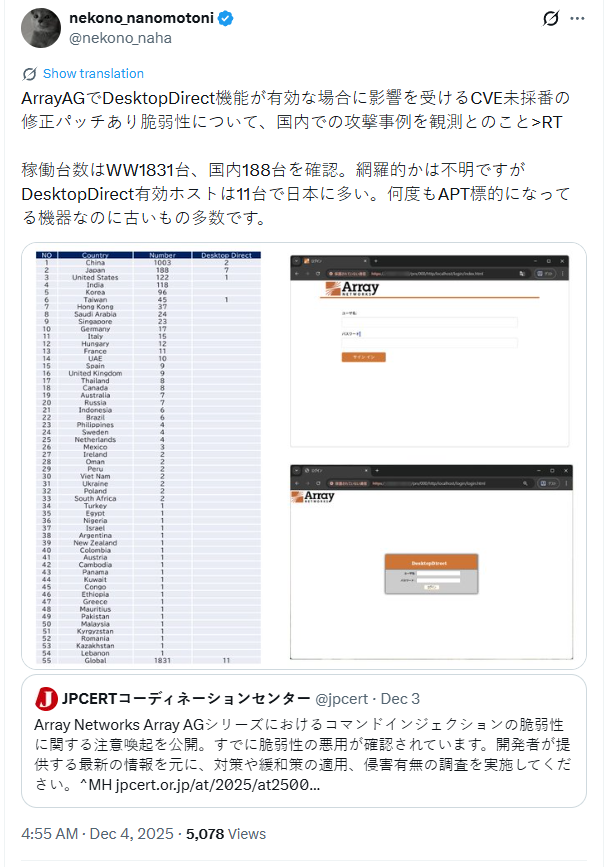
Research conducted by Macnica’s security researcher, Yutaka Sejiyama, reveals that there are 1,831 ArrayAG instances worldwide, primarily concentrated in China, Japan, and the United States.
Sejiyama confirmed that at least 11 hosts have the DesktopDirect feature enabled, emphasizing the significant possibility of more hosts with active DesktopDirect functionality.
Sejiyama expressed concerns to BleepingComputer, stating, “Because this product’s user base is concentrated in Asia and most of the observed attacks are in Japan, security vendors and organizations outside Japan have not been paying close attention.”
BleepingComputer reached out to Array Networks regarding the publication of a CVE-ID and an official advisory for the actively exploited vulnerability; however, a response was not received at the time of publication.
Notably, CISA issued a warning last year about active exploitation targeting CVE-2023-28461, a critical vulnerability for remote code execution in Array Networks AG and vxAG ArrayOS.

Broken IAM isn’t just an IT problem – the impact ripples across your whole business.
This comprehensive guide explains why traditional IAM practices fail to meet modern requirements, illustrates examples of effective IAM strategies, and offers a simple checklist for developing a scalable IAM strategy.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS































