Security
Beware: Malicious Chrome Extensions Stealing User Credentials

Malicious Chrome Extensions in Web Store Steal User Credentials
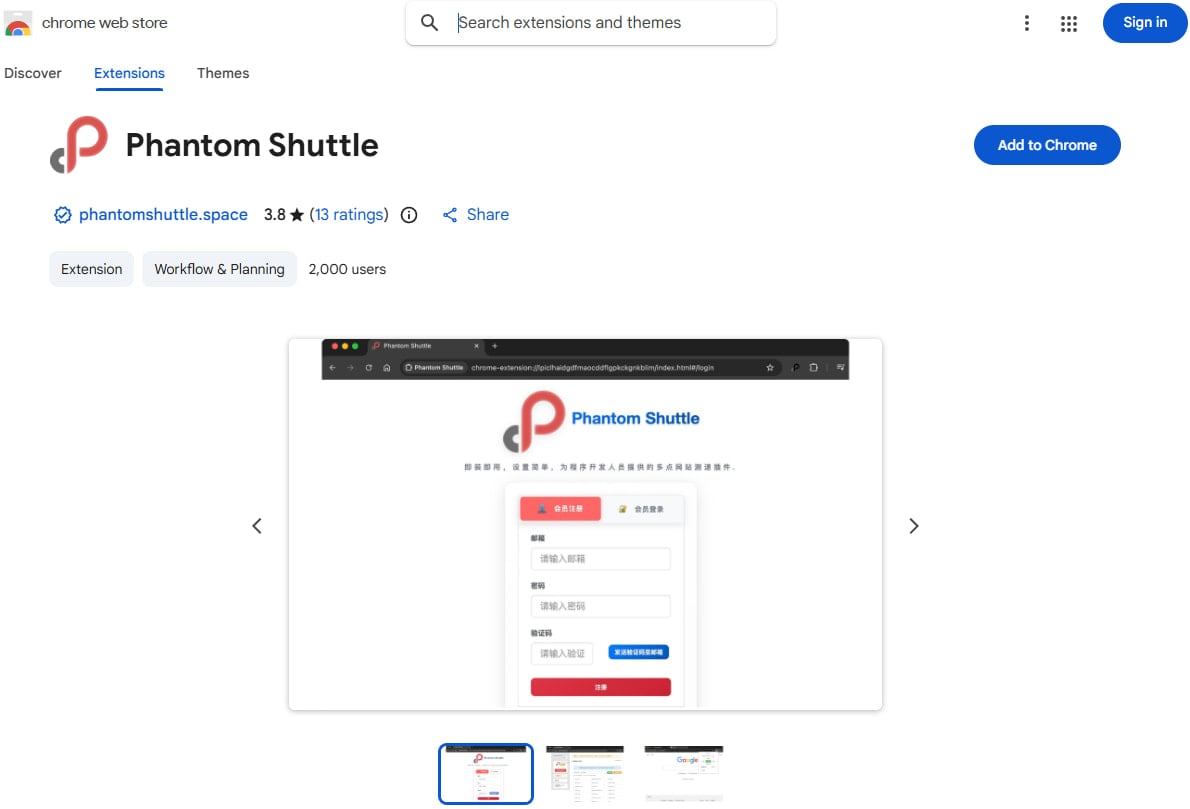
Recently, researchers have discovered two Chrome extensions in the Web Store known as ‘Phantom Shuttle’ that are disguising themselves as plugins for a proxy service. These extensions have been designed to intercept user traffic and extract sensitive data.
Despite the malicious intent of these extensions, they are still available for download on Chrome’s official marketplace and have been operational since at least 2017. The Socket supply-chain security platform released a report detailing the deceptive practices of these extensions.
The primary target audience of Phantom Shuttle includes users in China, particularly foreign trade workers who require connectivity testing from various locations within the country.
Both extensions are attributed to the same developer and are marketed as tools for proxying traffic and conducting network speed tests. They are available for subscription at prices ranging from $1.4 to $13.6.
Source: BleepingComputer
Covert Malicious Functionality
Researchers at Socket.dev have uncovered that Phantom Shuttle reroutes all user web traffic through proxies controlled by the threat actor, which are accessible using hardcoded credentials. This malicious code is inserted into the legitimate jQuery library.
The extensions employ a custom character-index encoding scheme to conceal the hardcoded proxy credentials. By utilizing a web traffic listener, the extensions can intercept HTTP authentication challenges on any website.
To redirect user traffic through the attacker’s proxies, the extensions dynamically adjust Chrome’s proxy settings via an auto-configuration script.
Under the default “smarty” mode, over 170 high-value domains are directed through the proxy network, including developer platforms, cloud services, social media platforms, and adult content sites. Notably, local networks and the command-and-control domain are excluded to avoid detection.
While operating as a man-in-the-middle, the extensions can capture data from various forms (credentials, card details, passwords, personal information), extract session cookies from HTTP headers, and obtain API tokens from requests.
BleepingComputer has reached out to Google regarding the presence of these extensions in the Web Store, but no immediate response has been provided.
Chrome users are advised to exercise caution when installing extensions, favoring those from reputable developers, reviewing user feedback, and scrutinizing permissions requested during installation.

Broken IAM isn’t just an IT problem – the impact ripples across your whole business.
This comprehensive guide delves into the reasons traditional IAM practices fall short in meeting modern demands, provides examples of effective IAM strategies, and offers a simple checklist for crafting a scalable approach.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS