Security
Beware: Senior Executives Targeted in Latest VENOM Phishing Attacks

New VENOM Phishing Attacks Targeting Senior Executives’ Microsoft Logins
Recent reports have highlighted a concerning trend in the cybersecurity landscape, with threat actors utilizing a sophisticated phishing-as-a-service (PhaaS) platform known as “VENOM” to steal the login credentials of high-ranking executives across various industries. This platform, which has been operational since at least November of last year, specifically targets CEOs, CFOs, and VPs within organizations.
Despite its malicious intent, VENOM operates discreetly, avoiding public promotion on common channels and underground forums to evade detection by researchers.
The Intricate VENOM Attack Chain
A detailed analysis by cybersecurity experts at Abnormal has revealed that VENOM’s phishing emails masquerade as Microsoft SharePoint document-sharing notifications, a tactic commonly used in internal communications to deceive targets.
These phishing emails are meticulously personalized, incorporating random HTML noise like fake CSS classes and comments to enhance their authenticity. Additionally, the inclusion of counterfeit email threads tailored to each recipient further boosts the credibility of the messages.
One unique aspect of VENOM’s attacks is the use of a QR code encoded in Unicode, a technique intended to bypass traditional scanning tools by redirecting the attack to mobile devices.
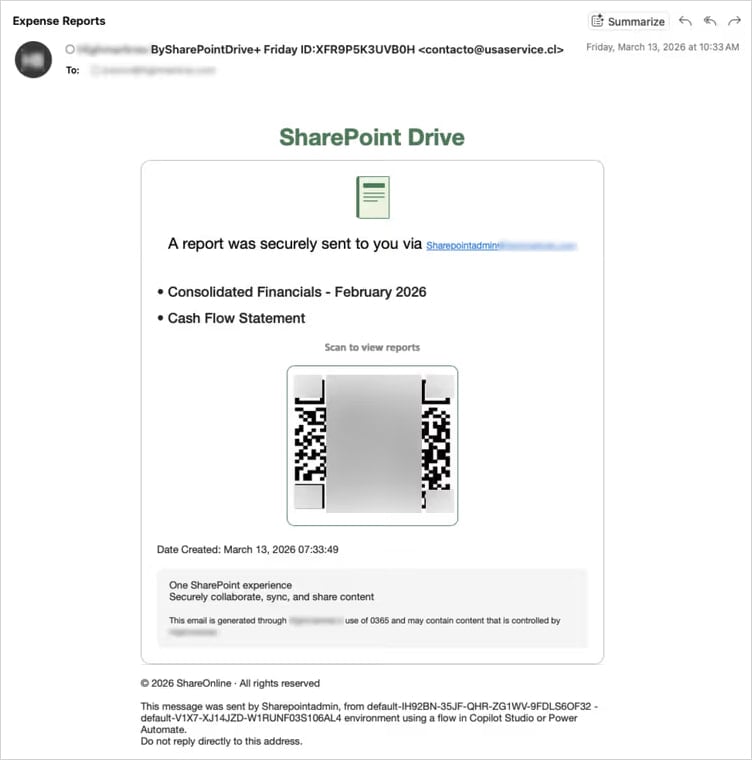
Source: Abnormal
Abnormal’s researchers have highlighted a unique approach adopted by VENOM, where the target’s email address is double Base64-encoded in the URL fragment, rendering it invisible to server-side logs and URL reputation feeds.
Upon scanning the QR code, victims are directed to a landing page designed to filter out security researchers and sandboxed environments, ensuring that only genuine targets are redirected to the phishing platform. Non-target individuals are redirected to legitimate websites to avoid suspicion.
Those who successfully pass the filtering process are led to a credential-harvesting page that mimics a real-time Microsoft login flow, capturing login credentials, and multi-factor authentication (MFA) codes, subsequently relaying them to Microsoft APIs and capturing the session token.
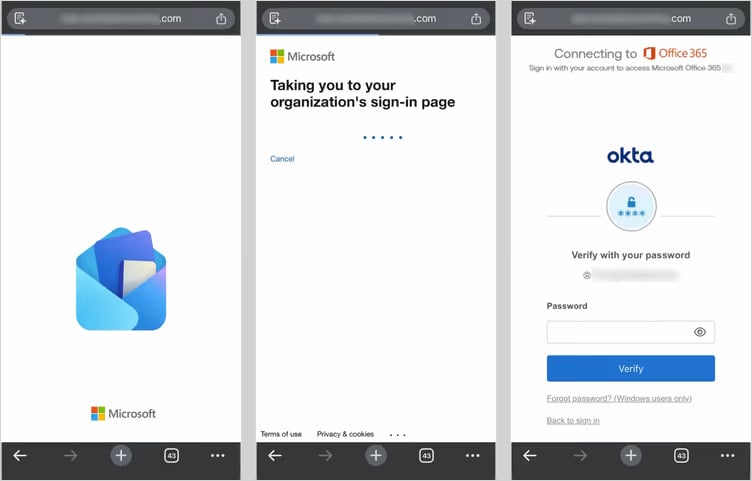
Source: Abnormal
In addition to the adversary-in-the-middle (AiTM) method, Abnormal’s researchers have identified a device-code phishing tactic where victims unknowingly authorize access to their Microsoft accounts for malicious purposes.
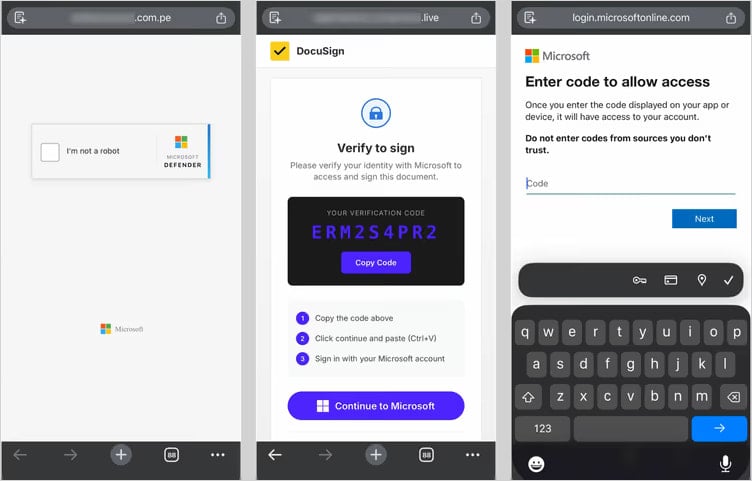
Source: Abnormal
This nefarious tactic has gained popularity due to its efficacy and resilience against password resets, with multiple phishing kits now offering it as an option.
Both attack methods employed by VENOM aim to establish persistent access during the authentication process. Whether through registering a new device on the victim’s account in the AiTM flow or obtaining a token for account access in the device code flow, the threat actor ensures continued control over the compromised accounts.
As a countermeasure, cybersecurity experts recommend that C-suite executives implement FIDO2 authentication, disable the device code flow when not required, and enforce stricter conditional access policies to mitigate the risk of token abuse.

Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
-

 Facebook6 months ago
Facebook6 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple6 months ago
Apple6 months agoMeta discontinues Messenger apps for Windows and macOS