Security
Corporate Espionage: The Dark Side of Zoom Stealer Browser Extensions

A recently uncovered scheme known as Zoom Stealer has impacted around 2.2 million users of Chrome, Firefox, and Microsoft Edge through 18 browser extensions. These extensions are designed to gather data related to online meetings, including URLs, IDs, topics, descriptions, and even embedded passwords.
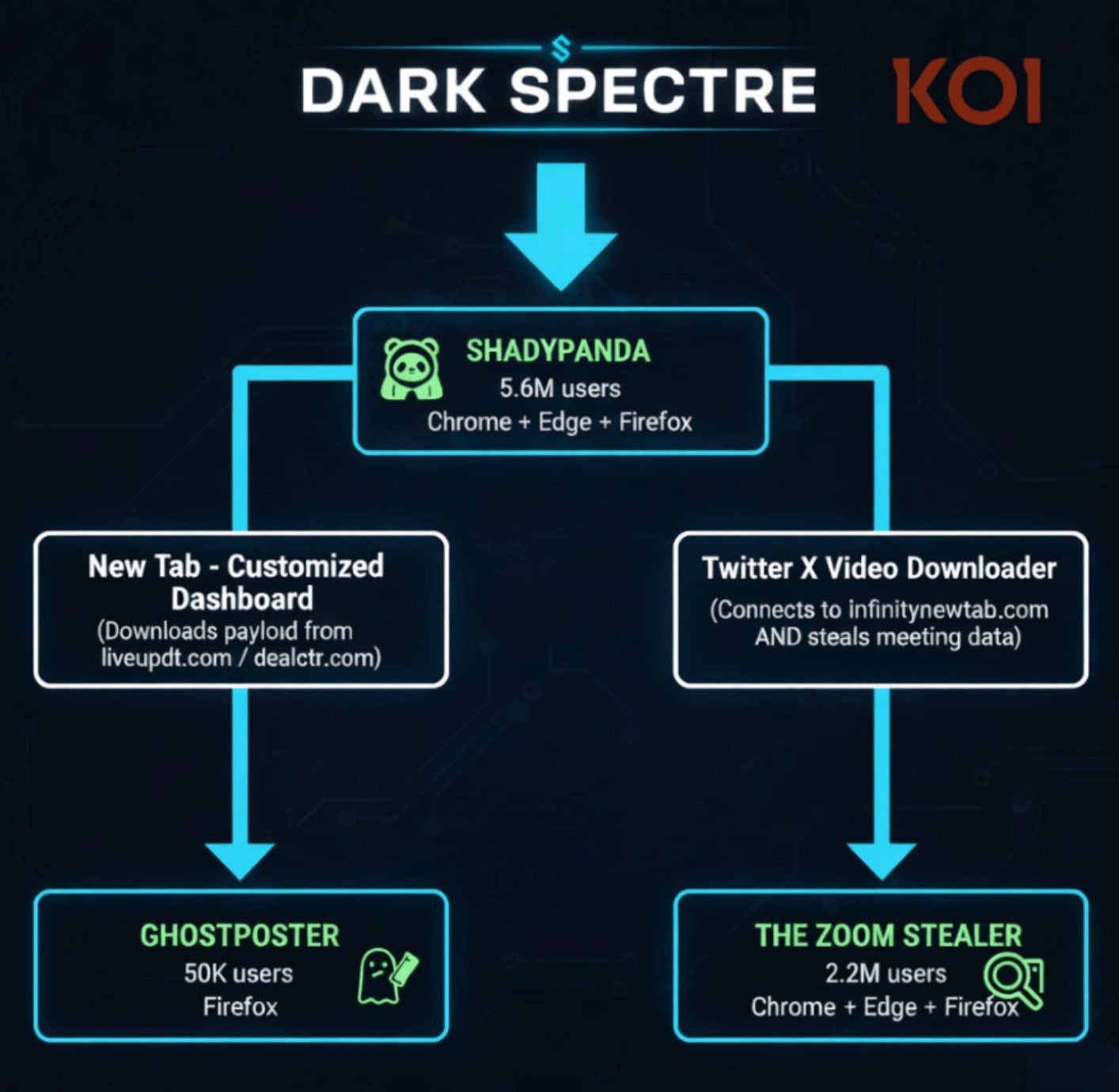
The Zoom Stealer campaign is part of a larger pattern involving three browser extension campaigns that have targeted over 7.8 million users in the span of seven years. These campaigns have been linked to a single threat actor identified as DarkSpectre.
DarkSpectre, the threat actor behind Zoom Stealer, is believed to be the same entity responsible for previous campaigns like GhostPoster targeting Firefox users and ShadyPanda, which delivered spyware to Chrome and Edge users, based on the shared infrastructure.

ShadyPanda, another campaign linked to DarkSpectre, continues to operate through 9 extensions and an additional 85 ‘sleepers’ that gradually turn malicious through updates. This information comes from researchers at Koi Security, a supply-chain security company.
Source: Koi Security
The connection to China has become more apparent with DarkSpectre, evident from hosting servers on Alibaba Cloud, ICP registrations, Chinese-language artifacts, and activity aligned with the Chinese timezone, as well as monetization strategies tailored to Chinese e-commerce.
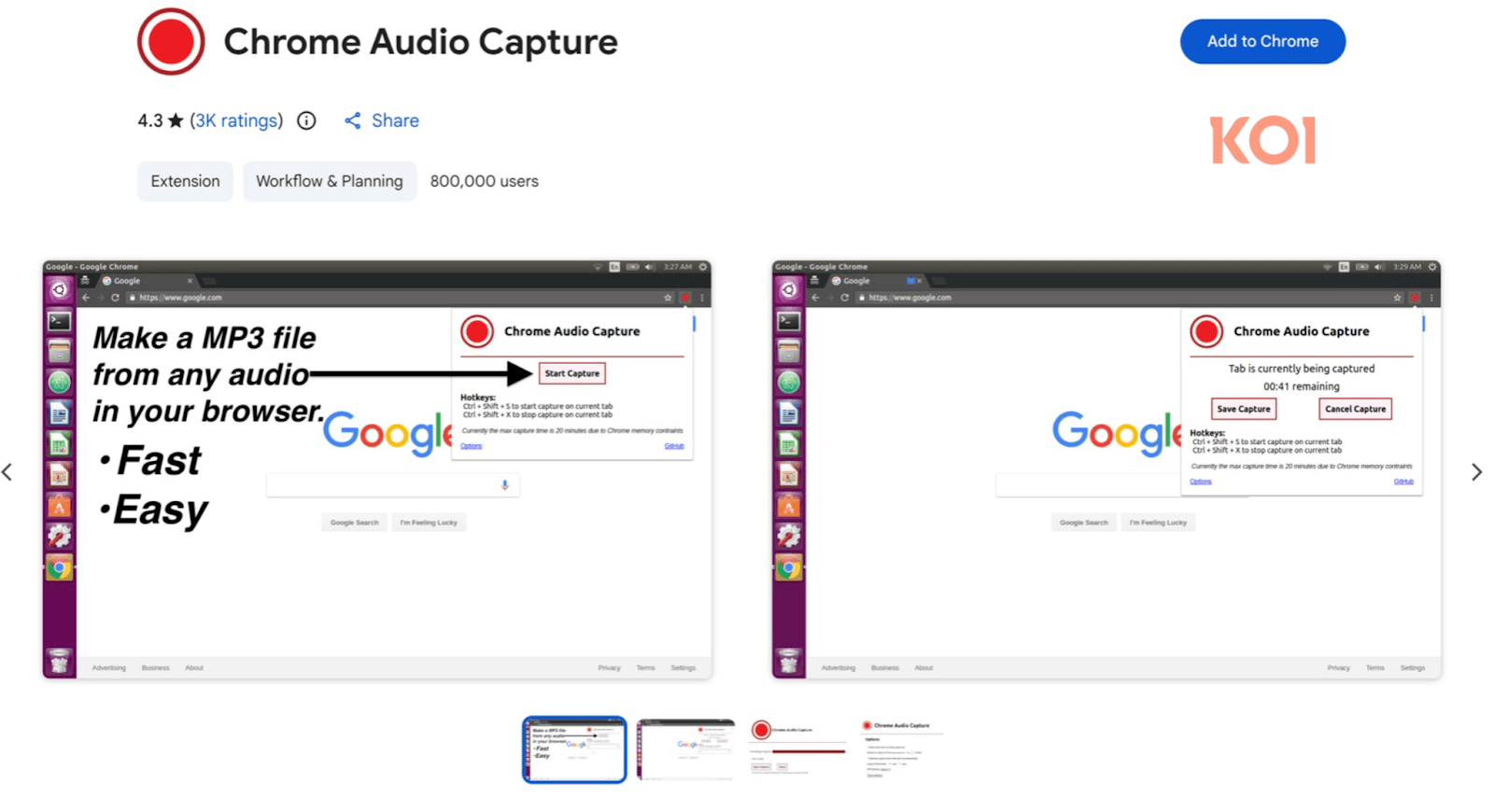
Corporate meeting intelligence
While the 18 extensions in the Zoom Stealer campaign are not exclusively focused on meeting data, some can be used for downloading videos or as recording tools. Notable extensions include Chrome Audio Capture with 800,000 installations and Twitter X Video Downloader, still accessible on the Chrome Web Store.
Researchers at Koi Security emphasize that these extensions are fully functional and perform their advertised tasks.
Source: Koi Security
According to Koi Security, all extensions in the Zoom Stealer campaign request permissions to access 28 video-conferencing platforms and collect various data points related to meetings. This includes meeting URLs, IDs, registration status, topics, speaker details, company information, and more.
The collected data is transmitted in real-time to threat actors via WebSocket connections, triggered when users interact with webinar registration pages or join meetings on conferencing platforms.
This data could be utilized for corporate espionage, sales intelligence, or social engineering attacks. It could potentially enable impersonation operations by providing attackers with valuable insights into confidential calls and participant lists.
Koi Security’s report highlights the importance of scrutinizing extension permissions and minimizing their usage to essential requirements to mitigate risks.
The researchers flagged the malicious extensions, but several remain available on the Chrome Web Store. A comprehensive list of active DarkSpectre extensions has been published.
BleepingComputer has reached out to InfinityNewTab and Google for comments, and updates will be provided accordingly.

Issues with Identity and Access Management (IAM) extend beyond IT, impacting various aspects of a business. This guide explores the shortcomings of traditional IAM practices, showcases effective IAM strategies, and offers a checklist for creating a scalable IAM approach.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS































