Security
CrystalRAT Evolution: A Deadly Combination of RAT, Stealer, and Prankware

New CrystalRAT Malware: Remote Access, Data Theft, and Prankware Features
A new malware known as CrystalRAT is currently being advertised on Telegram as a malware-as-a-service (MaaS) offering various capabilities such as remote access, data theft, keylogging, and clipboard hijacking. This malware first emerged in January with a subscription-based model and has been promoted not only on Telegram but also on YouTube through a dedicated marketing channel showcasing its functionalities.
Researchers at Kaspersky have reported that CrystalRAT bears striking similarities to WebRAT (Salat Stealer), including a similar panel design, Go-based code, and a bot-based sales system. In addition to its malicious features, CrystalRAT also includes a range of prankware features designed to annoy users or disrupt their work, making it a multifaceted threat.
Source: Kaspersky
CrystalX RAT Overview
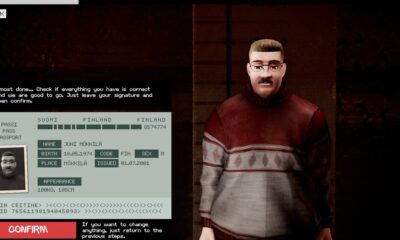
Kaspersky’s analysis reveals that CrystalRAT offers a user-friendly control panel and an automated builder tool with customization options such as geoblocking, executable customization, and anti-analysis features. The payloads generated by CrystalRAT are zlib-compressed and encrypted using the ChaCha20 symmetric stream cipher for enhanced protection.
The malware establishes a connection to the command-and-control (C2) server via WebSocket to send host information for profiling and infection tracking. CrystalRAT’s infostealer component, currently disabled for an upgrade, targets Chromium-based browsers like Chrome, Yandex, and Opera, as well as collects data from desktop applications such as Steam, Discord, and Telegram.
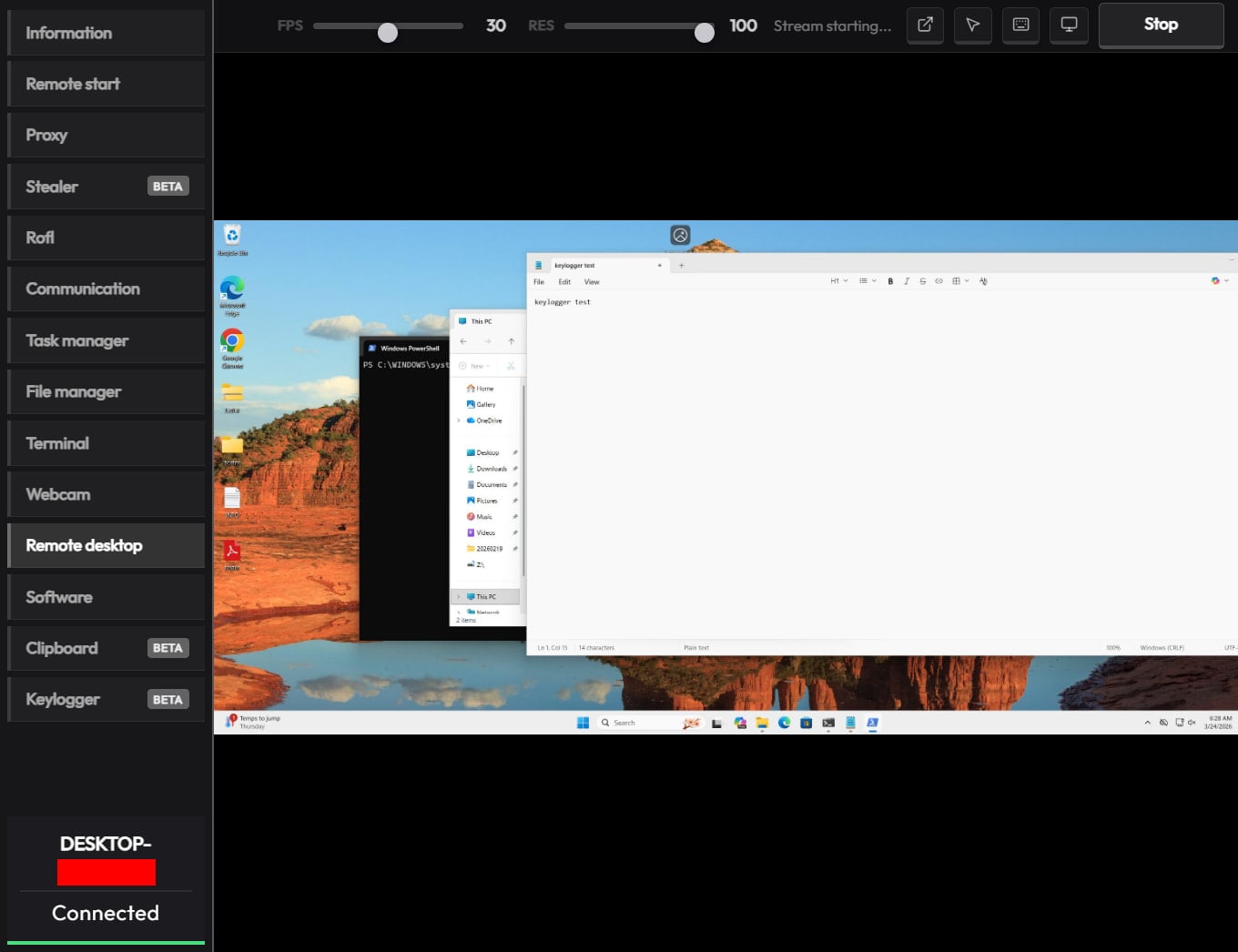
Furthermore, the remote access module allows cybercriminals to execute commands via CMD, transfer files, navigate the file system, and control the infected machine in real-time through built-in VNC functionality. The malware also possesses spyware-like capabilities, enabling it to capture video and audio from the microphone.
Additionally, CrystalRAT includes a keylogger that streams keystrokes in real-time to the C2 server and a clipper tool that identifies wallet addresses in the clipboard using regular expressions and replaces them with the attacker’s provided addresses.
Source: Kaspersky
Adding “Fun” to the Equation
One distinguishing factor of CrystalRAT in the MaaS landscape is its inclusion of prankware features. These features, while not directly contributing to cybercriminals’ monetization efforts, add a unique aspect to the malware. Among the actions CrystalRAT can perform on infected devices are changing desktop wallpapers, altering display orientations, forcing system shutdowns, remapping mouse buttons, disabling input devices, displaying fake notifications, and more.
While these prank features may not increase the profitability of attacks, they could attract less experienced threat actors or individuals interested in causing disruptions. Additionally, these features could serve as a distraction while the data theft components operate in the background.
To minimize the risk of malware infections, users are encouraged to exercise caution when engaging with online content and to avoid downloading software or media from untrustworthy sources.

Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS