Security
Deadly Deception: The LastPass Scam

Warning: LastPass Users Targeted by Phishing Campaign
LastPass has issued a warning to its customers regarding a sophisticated phishing campaign that aims to compromise their password vaults. The deceptive emails being sent out request access to the password vault under the guise of a legacy inheritance process.
According to LastPass, this malicious activity began in mid-October and has been traced back to a financially motivated threat group known as CryptoChameleon (UNC5356). This group is notorious for its involvement in cryptocurrency theft and has targeted popular wallets such as Binance, Coinbase, Kraken, and Gemini.
CryptoChameleon utilizes a phishing kit that specializes in stealing cryptocurrency by posing as legitimate platforms like Okta, Gmail, iCloud, and Outlook. LastPass users were previously targeted by this group in April 2024, but the latest campaign is more extensive and now includes targeting passkeys as well.
The fraudulent emails sent to LastPass users falsely claim that a family member has requested access to their vault by submitting a death certificate.
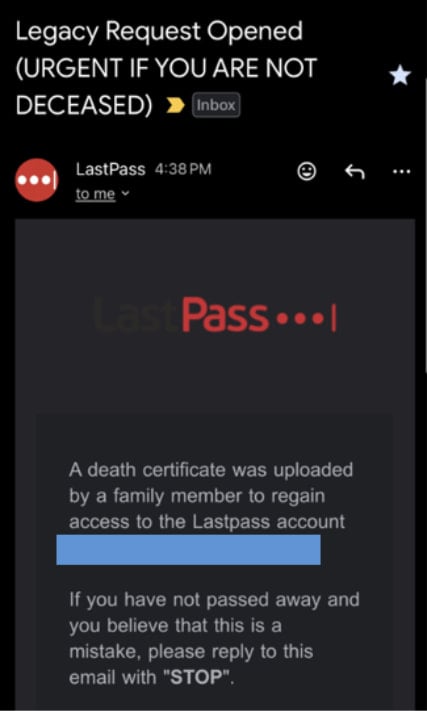
Source: LastPass
LastPass’s inheritance process includes an emergency access feature that allows designated individuals to request access to a user’s vault in the event of their death or incapacity. When such a request is initiated, the user receives an email notification, and access is granted after a specified waiting period.
The fraudulent legacy request contains an agent ID number to lend credibility to the scam, urging the recipient to take action by clicking on a link to cancel the request if they are not deceased. However, clicking on the link redirects them to a fake page on lastpassrecovery[.]com, prompting them to enter their master password.
LastPass has reported instances where the threat actors have even gone as far as calling victims posing as company staff and instructing them to enter their credentials on the phishing site.
One notable aspect of the CryptoChameleon attack targeting LastPass users is the use of passkey-focused phishing domains such as mypasskey[.]info and passkeysetup[.]com. These domains indicate a deliberate effort to steal users’ passkeys, which are crucial for passwordless authentication using FIDO2 / WebAuthn protocols.
Password managers like LastPass, 1Password, Dashlane, and Bitwarden have integrated passkeys as a more secure alternative to traditional passwords. However, threat actors have begun targeting these passkeys directly, posing a significant risk to user security.
In a previous data breach incident in 2022, LastPass experienced a breach where encrypted vault backups were stolen. This breach led to targeted attacks that resulted in significant losses, highlighting the importance of safeguarding sensitive information.

Recent reports indicate that 46% of environments have had passwords cracked, nearly doubling from the previous year’s figure of 25%. Stay informed with the Picus Blue Report 2025, which offers insights into prevention, detection, and data exfiltration trends.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS