Security
Down Under Alert: Unpatched Cisco Devices at Risk of BadCandy Infections in Australia

Cybersecurity Warning: Unpatched Cisco Devices Vulnerable to BadCandy Webshell Attacks
In a recent alert, the Australian government has raised concerns about ongoing cyberattacks targeting unpatched Cisco IOS XE devices in the country. These attacks aim to infect routers with the malicious BadCandy webshell.
The primary vulnerability being exploited in these attacks is identified as CVE-2023-20198, a critical flaw that allows threat actors to create a local admin user via the web user interface, providing them with unauthorized access to the devices.
Cisco addressed this vulnerability in October 2023, categorizing it as actively exploited. Subsequently, a public exploit became available, leading to widespread attempts to plant backdoors on internet-exposed devices.
Despite the patch released by Cisco, Australian authorities have reported continued use of variants of the BadCandy webshell in cyberattacks throughout 2024 and 2025. This indicates that a significant number of Cisco devices in the country remain unpatched.
Once installed, BadCandy enables remote attackers to execute commands with root privileges on compromised devices. Although the webshell is removed upon device reboot, attackers can easily reintroduce it if the devices remain unpatched and accessible via the web interface.
Recent reports from the Australian Signals Directorate (ASD) suggest that over 400 devices in Australia may have been compromised with BadCandy since July 2025. As of late October 2025, approximately 150 devices are still affected.
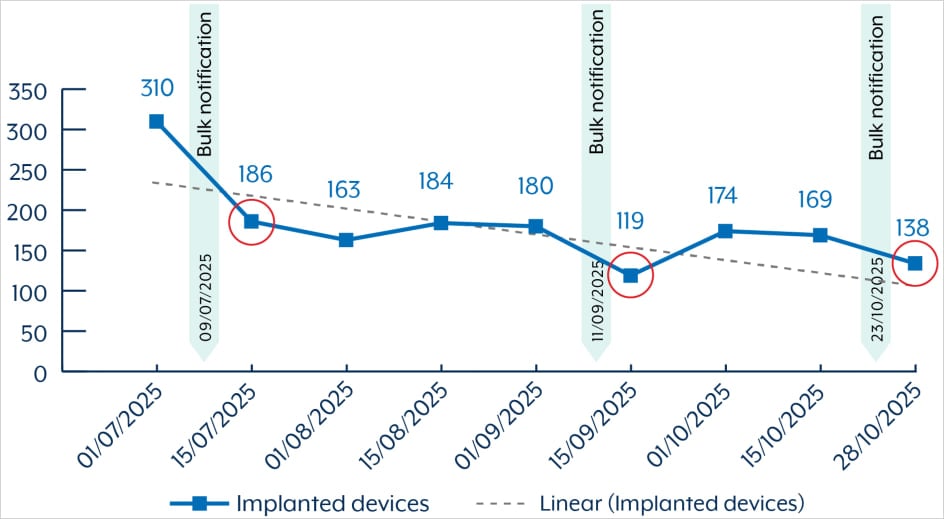
Source: ASD
While the number of infections is decreasing, the ASD has observed instances of re-exploitation of the vulnerability against previously compromised endpoints, even after the affected entities were notified.
The agency warns that attackers can detect the removal of the BadCandy implant and target the same devices for re-infection. As a response to these ongoing threats, the ASD is issuing notifications to victims with instructions on patching, device hardening, and incident response protocols.
Furthermore, the ASD highlights that the flaw exploited by BadCandy has been utilized by state actors, such as the Chinese group ‘Salt Typhoon,’ known for targeting large telecommunication service providers in the U.S. and Canada.
While BadCandy could theoretically be deployed by any malicious actor, recent escalations in attacks are believed to be linked to state-sponsored cyber-actors, according to the ASD.
Administrators of Cisco IOS XE systems globally, including those in Australia, are strongly advised to adhere to the vendor’s mitigation recommendations outlined in the security bulletin. Cisco has also published a comprehensive hardening guide for IOS XE devices to enhance their resilience against such threats.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS






























