Security
Embracing Danger: How Hugging Face Became a Gateway for Android Malware

Hugging Face Platform Abused to Spread Android Malware
Recently, a new Android malware campaign has emerged, utilizing the Hugging Face platform as a repository for numerous variations of an APK payload designed to gather credentials for popular financial and payment services.
The Hugging Face platform is well-known for hosting and distributing artificial intelligence (AI), natural language processing (NLP), and machine learning (ML) models, datasets, and applications.
Although typically considered a trusted platform that does not raise security concerns, malicious actors have previously exploited it to host harmful AI models.
The campaign, uncovered by researchers at Romanian cybersecurity company Bitdefender, leverages the Hugging Face platform to distribute Android malware.
The attack begins by enticing victims to install a dropper app called TrustBastion, which uses scareware-style ads claiming the target’s device is infected. The malicious app masquerades as a security tool, purportedly detecting threats like scams, fraudulent SMS messages, phishing attempts, and malware.
Upon installation, TrustBastion displays a mandatory update alert with visuals resembling Google Play.
Source: Bitdefender
Instead of directly delivering malware, the dropper contacts a server associated with trustbastion[.]com, which redirects to a Hugging Face dataset repository hosting the malicious APK. The final payload is downloaded from the Hugging Face infrastructure and distributed via its content delivery network (CDN).
To evade detection, the threat actor employs server-side polymorphism, generating new payload variants every 15 minutes, as reported by Bitdefender.
“At the time of investigation, the repository was approximately 29 days old and had accumulated more than 6,000 commits,” Bitdefender stated.
While analyzing the payload-serving repository, it was taken down, but the operation resurfaced under a new name, ‘Premium Club,’ with new icons while retaining the same malicious code.
The primary payload, unnamed, acts as a remote access tool that aggressively exploits Android’s Accessibility Services, justifying the request as essential for security purposes.
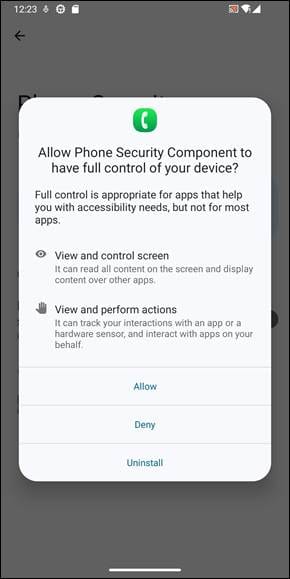
Source: Bitdefender
This enables the malware to deploy screen overlays, capture the user’s screen, execute swipes, prevent uninstallation attempts, and more.
The malware, according to Bitdefender, monitors user activity, captures screenshots, and exfiltrates the data to its operators. It also presents fake login interfaces mimicking financial services like Alipay and WeChat to steal credentials and attempts to obtain the lock screen code.
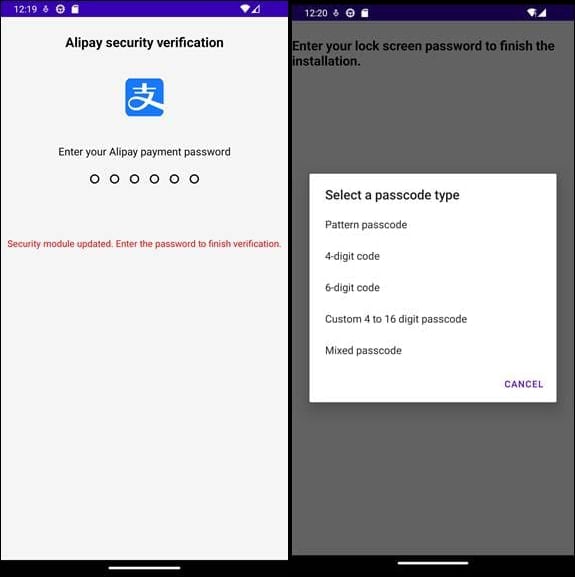
Source: Bitdefender
The malware remains connected continuously to the command-and-control (C2) server, receiving stolen data, executing command instructions, updating configurations, and pushing fake in-app content to maintain TrustBastion’s legitimacy.
Bitdefender promptly informed Hugging Face about the repository used by threat actors, leading to the removal of datasets containing the malware. Additionally, researchers published a series of indicators of compromise for the dropper, network, and malicious packages.
It is advisable for Android users to steer clear of downloading apps from third-party stores or manually installing them. Reviewing an app’s permissions and ensuring their necessity for intended functionality is crucial.

Whether you’re cleaning up old keys or setting guardrails for AI-generated code, this guide helps your team build securely from the start.
Get the cheat sheet and take the guesswork out of secrets management.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook3 months ago
Facebook3 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook3 months ago
Facebook3 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS
































