Security
Enhancing Incident Response: A Collaboration Between Criminal IP and Palo Alto Networks Cortex XSOAR

Criminal IP, an innovative AI-powered threat intelligence and attack surface monitoring platform created by AI SPERA, has now been officially incorporated into Palo Alto Networks’ Cortex XSOAR.
This integration brings real-time external threat context, exposure intelligence, and automated multi-stage scanning directly into Cortex XSOAR’s orchestration engine. This advancement provides security teams with improved incident accuracy and quicker response times compared to traditional log-centric approaches.
Being a prominent figure in cybersecurity, Palo Alto Networks leverages Cortex XSOAR as a central hub for SOC automation. With the addition of Criminal IP through the Cortex Marketplace,
Cortex XSOAR users now have the capability to assess suspicious IPs and domains using not just static reputation data but also behavioral signals, exposure history, infrastructure correlations, and AI-driven threat scoring. This functionality is seamlessly integrated without the need for additional systems or manual lookups by analysts.
Enhancing Incident Response with AI Context
Modern SOC teams are inundated with alerts, yet traditional enrichment methods rely on static reputation feeds that offer limited context. This often results in overlooking crucial details such as port exposure, CVE ties, certificate reuse, DNS changes, or anonymization behavior.
Criminal IP addresses this gap by continuously analyzing global internet-facing assets and correlating IP behavior, domain activity, SSL/TLS data, port states, CVE exposure, IDS hits, and masking indicators.
When an alert involves an IP or domain, Cortex XSOAR can automatically integrate this enriched intelligence into the active incident through a playbook. This streamlines the process for analysts to evaluate intent and severity directly within Cortex SOAR.
Access the comprehensive threat intelligence provided by Criminal IP to proactively identify, analyze, and respond to emerging threats.
Driven by AI and OSINT, Criminal IP offers threat scoring, reputation data, and real-time detection of various malicious indicators, including C2 servers, IOCs, and masking services like VPNs and proxies. Its API-first architecture ensures seamless integration into security workflows, enhancing visibility, automation, and response capabilities.
Request Your Demo
Advanced Scanning and Exposure Linking
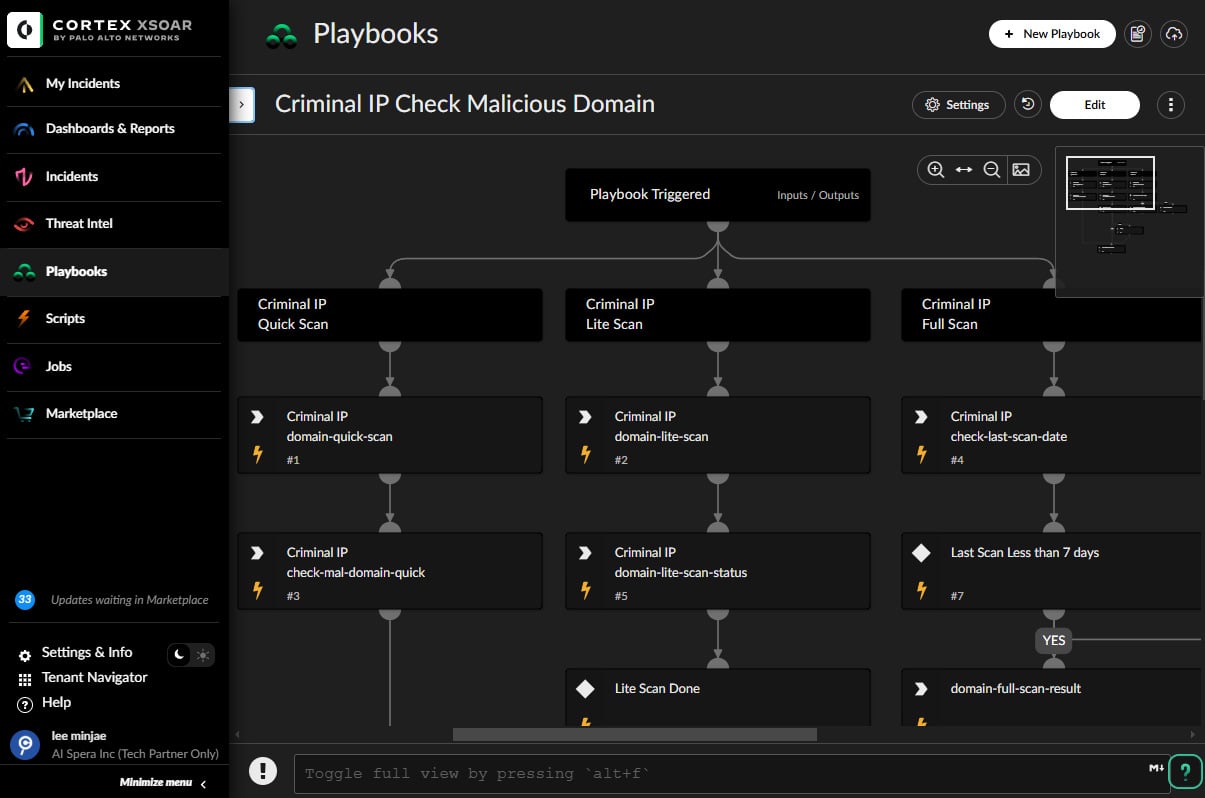
Cortex XSOAR playbooks can trigger Criminal IP’s automated three-stage scanning process: starting with a Quick Lookup, progressing to a Lite Scan, and culminating in a Full Scan for comprehensive attack surface analysis.
The results of the Full Scan are presented as structured reports within Cortex XSOAR, with generic polling mechanisms ensuring continuous workflow without manual intervention.
Besides enriching alerts, the integration establishes links between internal telemetry and open-internet intelligence, providing insights into historical behavior, C2 relationships, anonymization indicators, abuse records, and SSL correlations for each indicator.
Cortex XSOAR also enables the scheduling of Micro Attack Surface Management scans to evaluate exposed ports, certificate validity, vulnerable services, and outdated software. This feature offers lightweight, continuous ASM capabilities to help organizations identify vulnerabilities preemptively.
Driving Intelligence-Driven Autonomous Security

The collaboration between Palo Alto Networks and Criminal IP signifies a broader shift towards autonomous security operations. By combining Cortex XSOAR’s automation and orchestration capabilities with Criminal IP’s real-time external analysis, SOC teams can automate decision-making processes that previously required manual research across multiple intelligence sources.
This integration reduces response times, enhances the accuracy of incident classification, and mitigates analyst fatigue—an increasingly critical issue as alert volumes and AI-generated threats continue to rise.
Criminal IP is already accessible through Azure, AWS, and Snowflake marketplaces and maintains partnerships with over 40 security vendors, including Cisco, Fortinet, and Tenable. Its expansion into the Palo Alto Networks ecosystem lays the groundwork for further integrations across XDR and cloud security solutions.
Byungtak Kang, CEO of AI SPERA, emphasized that the integration “underscores the growing importance of AI-driven threat intelligence and exposure analytics in enterprise security operations,” highlighting Criminal IP’s role in facilitating organizations’ transition towards fully autonomous defense architectures.
Explore more: https://cortex.marketplace.pan.dev/marketplace/details/CriminalIP/
Presented and authored by Criminal IP.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS































