Security
Exposed: The MongoDB Secrets Leak – 87K Servers Vulnerable to Exploited MongoBleed Flaw

MongoBleed Vulnerability Exposes MongoDB Secrets
In a recent development, a critical vulnerability affecting various versions of MongoDB, known as MongoBleed (CVE-2025-14847), has been identified and is currently being exploited in the wild. It has left over 80,000 potentially vulnerable servers exposed on the public internet.
Exploitation of this vulnerability allows attackers to remotely extract sensitive data, including secrets, credentials, and other confidential information from exposed MongoDB servers. The severity of this vulnerability has been rated at 8.7 and has been classified as a “critical fix,” with a patch available for self-hosted instances since December 19.
Exploit Reveals MongoDB Server Secrets
The MongoBleed vulnerability is rooted in how the MongoDB Server processes network packets utilizing the zlib library for lossless data compression. Researchers at Ox Security have identified that the issue arises from MongoDB returning the amount of allocated memory during network message processing instead of the length of the decompressed data.
By sending a malformed message claiming a larger size when decompressed, threat actors can cause the server to allocate a larger memory buffer, leading to the leakage of sensitive in-memory data to the client.
The leaked information may include credentials, API and cloud keys, session tokens, personally identifiable information (PII), internal logs, configurations, paths, and client-related data. Notably, the decompression of network messages occurs before the authentication stage, meaning that attackers exploiting MongoBleed do not require valid credentials.
A public proof-of-concept exploit named “MongoBleed,” created by Elastic security researcher Joe Desimone, has been released to demonstrate the potential for leaking sensitive memory data. Security researcher Kevin Beaumont has confirmed the validity of the exploit code, emphasizing its capability to extract database passwords and AWS secret keys from MongoDB instances.
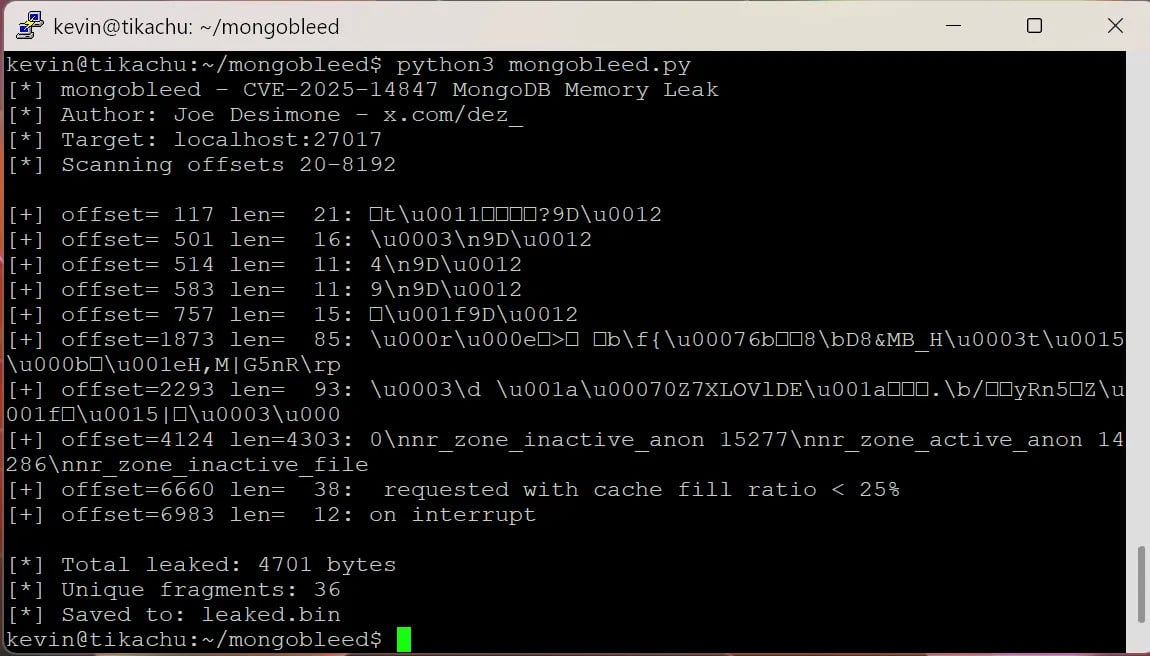
source: Kevin Beaumont
As of December 27, the Censys platform has reported over 87,000 potentially vulnerable MongoDB instances exposed on the public internet, with a significant number located in the United States, China, and Germany.
Exploitation and Detection Measures
The impact of the MongoBleed vulnerability extends to cloud environments, with telemetry data from cloud security platform Wiz indicating that 42% of visible systems contain MongoDB versions susceptible to CVE-2025-14847. Wiz researchers have observed instances of MongoBleed exploitation and urge organizations to prioritize patching.
While unverified, there are claims from threat actors suggesting the use of the MongoBleed flaw in a recent breach of Ubisoft’s Rainbow Six Siege online platform. Recon InfoSec co-founder Eric Capuano emphasizes the importance of not only patching but also monitoring for signs of compromise.
Capuano has shared a detection method involving the identification of a source IP with numerous connections but zero metadata events. However, he warns that attackers could modify exploit code to evade detection.
Security expert Florian Roth has leveraged Capuano’s research to develop the MongoBleed Detector, a tool that parses MongoDB logs to identify potential exploitation of the CVE-2025-14847 vulnerability.
Secure Lossless Compression Solutions
MongoDB has released patches for the MongoBleed vulnerability in versions 8.2.3, 8.0.17, 7.0.28, 6.0.27, 5.0.32, and 4.4.30, urging administrators to upgrade to these secure releases. The vendor highlights that a wide range of MongoDB versions dating back to late 2017 are impacted by MongoBleed, necessitating immediate action.
Customers using MongoDB Atlas, the fully managed multi-cloud database service, have received the patch automatically and do not need to take any further steps. MongoDB emphasizes that there is no workaround for the vulnerability and advises customers to disable zlib compression on the server if upgrading is not feasible.
Safe alternatives for lossless data compression, such as Zstandard (zstd) and Snappy, maintained by Meta and Google respectively, are recommended by MongoDB as secure options.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook3 months ago
Facebook3 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook3 months ago
Facebook3 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS