Security
Fortifying Security: RansomHouse Implements Advanced Encryption and Multi-Layered Data Processing

An upgrade in the encryptor of RansomHouse ransomware-as-a-service (RaaS) has taken place, transitioning from a basic linear encryption method to a more sophisticated multi-layered approach.
These enhancements result in stronger encryption, faster speeds, and increased reliability on current target systems, providing threat actors with greater leverage in negotiations after data encryption.
Introduced in December 2021 as a data extortion cybercriminal operation, RansomHouse later incorporated encryptors into its attacks and developed MrAgent, an automated tool capable of locking multiple VMware ESXi hypervisors simultaneously.

Recent reports revealed that threat actors targeted the Japanese e-commerce giant Askul Corporation using multiple ransomware families.
A recent report by Palo Alto Networks Unit 42 delves deeper into the toolset of RansomHouse, highlighting its latest encryptor variant named ‘Mario’.
New ‘Mario’ Encryptor
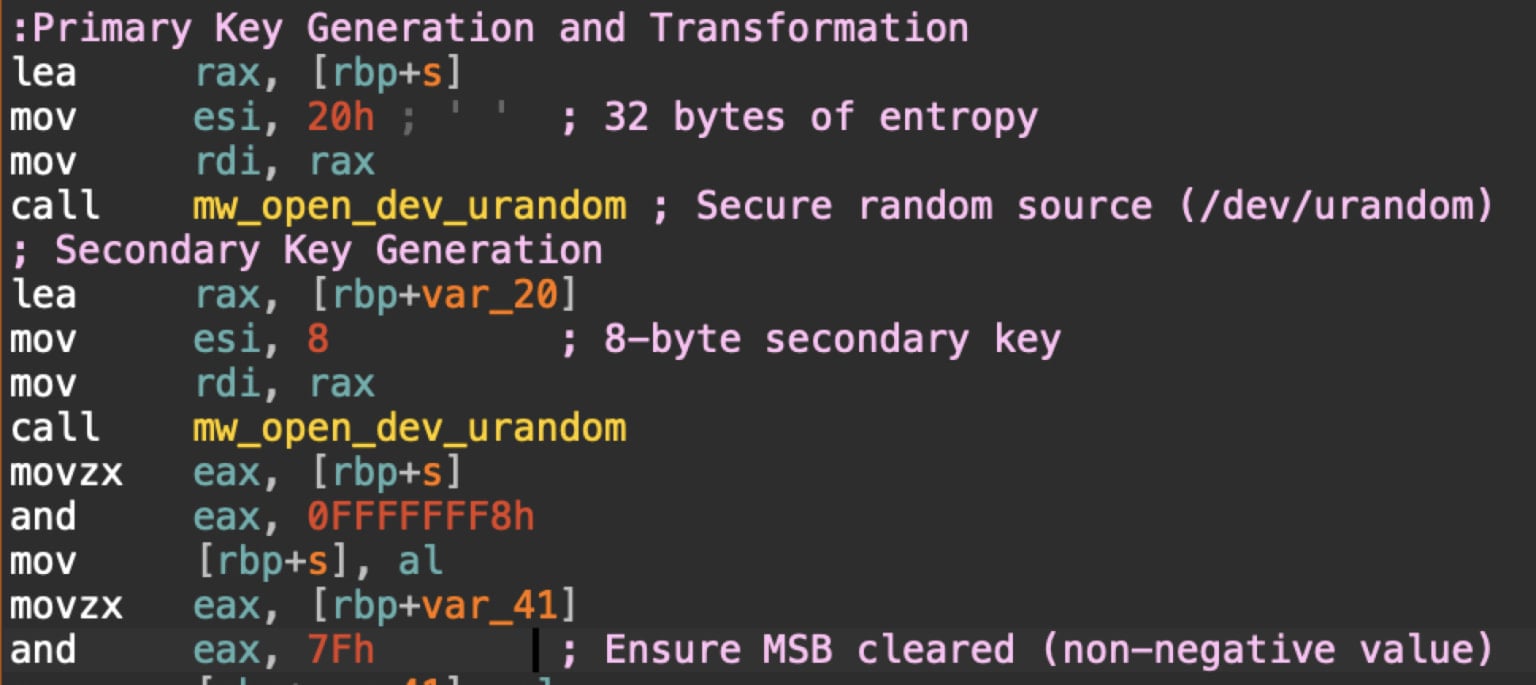
The latest encryptor variant from RansomHouse, ‘Mario,’ shifts from a single-pass file data transformation to a two-stage process utilizing two keys: a 32-byte primary key and an 8-byte secondary key.
This new approach enhances encryption entropy and makes partial data recovery more challenging.
Source: Unit 42
The second major upgrade in ‘Mario’ involves a new file processing strategy that incorporates dynamic chunk sizing at an 8GB threshold, along with intermittent encryption.
Unit 42 notes that this approach complicates static analysis due to its non-linear nature, use of complex mathematical calculations for processing order, and unique methods for handling files based on size.
Another significant enhancement in ‘Mario’ is the improved memory layout and buffer organization, along with increased complexity utilizing dedicated buffers for each encryption stage or role.
The updated encryptor version now provides more detailed information during file processing compared to previous versions, which only indicated task completion.
The new variant continues to target VM files, encrypting them and appending the ‘.emario’ extension while leaving a ransom note (How To Restore Your Files.txt) in affected directories.
Source: Unit 42
Unit 42 warns that the encryption upgrade by RansomHouse signifies a concerning trend in ransomware development, raising decryption challenges and making static analysis and reverse engineering more difficult.
Despite being a long-standing RaaS operation, RansomHouse remains a mid-tier threat in terms of attack volume. Its continuous advancement of sophisticated tools indicates a strategic focus on efficiency and evasion rather than sheer scale.

Issues with Identity and Access Management (IAM) extend beyond IT, impacting the entire business.
This comprehensive guide explains why traditional IAM practices fall short in modern environments, showcases effective IAM practices, and offers a checklist for a scalable strategy.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS






























