Security
GitHub Vulnerability Exploits: The Rise of WebRAT Malware

WebRAT Malware Spreading Through Fake Vulnerability Exploits on GitHub
The distribution of the WebRAT malware has taken a new turn as it is now being disseminated through GitHub repositories that falsely claim to offer proof-of-concept exploits for recently disclosed vulnerabilities.
Previously, WebRAT was mainly spread through pirated software and cheats for popular games like Roblox, Counter Strike, and Rust. WebRAT is a backdoor with information-stealing capabilities that emerged earlier this year.
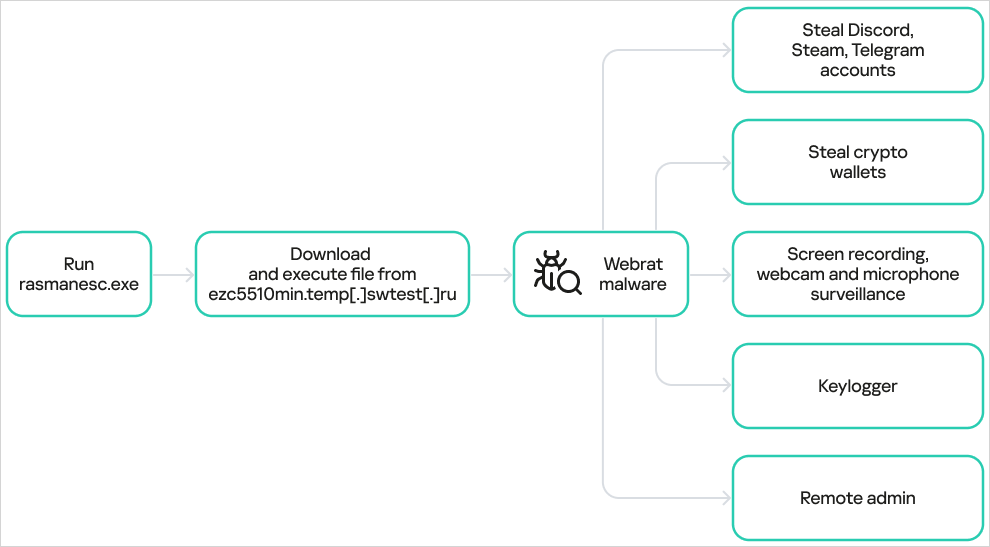
Solar 4RAYS reported in May that WebRAT has the ability to steal credentials for various accounts including Steam, Discord, and Telegram, as well as cryptocurrency wallet data. Additionally, it can spy on victims through webcams and capture screenshots.

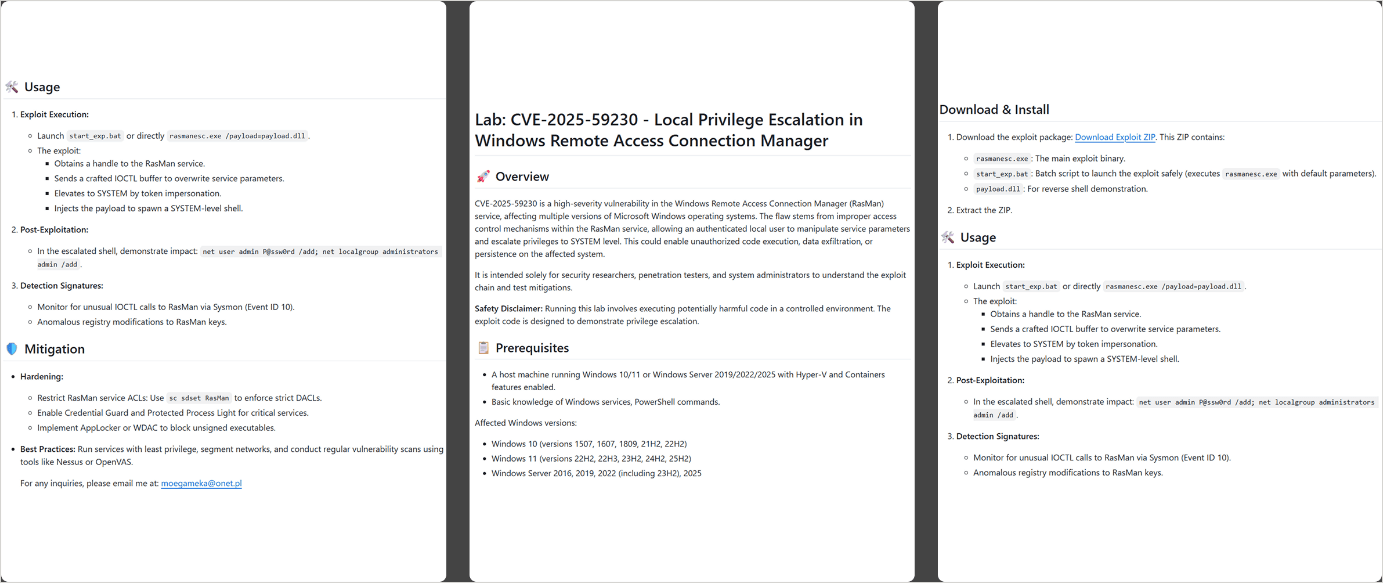
Since September, the operators have begun distributing the malware through carefully crafted repositories that claim to offer exploits for several vulnerabilities covered in media reports. Some of these vulnerabilities include CVE-2025-59295, CVE-2025-10294, and CVE-2025-59230.
Kaspersky researchers discovered 15 repositories distributing WebRAT, all providing information about the exploit, its functionality, and available mitigations.
The malware employs various methods to establish persistence, such as Windows Registry modifications, Task Scheduler, and injection into random system directories.
According to Kaspersky, the fake exploits are delivered in the form of a password-protected ZIP file containing several components including the main dropper named rasmanesc.exe.
Source: Kaspersky
The dropper elevates privileges, disables Windows Defender, and then downloads and executes WebRAT from a hardcoded URL, as per Kaspersky’s analysis.
Kaspersky states that the WebRAT variant used in this campaign exhibits the same capabilities as previously documented samples.
Source: Kaspersky
Using fake exploits on GitHub to deceive users into installing malware is a known tactic, with recent instances involving a fake “LDAPNightmare” exploit. Kaspersky has removed all malicious repositories related to the WebRAT campaign but advises caution when sourcing information from GitHub.
When testing exploits or code from potentially untrusted sources, it is recommended to run them in a controlled, isolated environment.

Broken IAM impacts your entire business, not just IT. Learn about modern IAM practices and build a scalable strategy with this practical guide.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS































