Security
Hackers Target Resecurity in Alleged Honeypot Attack

Update: The article has been revised to accurately reflect that the ShinyHunters deny involvement in the incident. The story and title have been adjusted accordingly.
Threat actors linked to the “Scattered Lapsus$ Hunters” (SLH) group claim to have infiltrated cybersecurity firm Resecurity’s systems and extracted internal data. However, Resecurity asserts that the attackers only accessed a honeypot intentionally set up with fake information to monitor their movements.
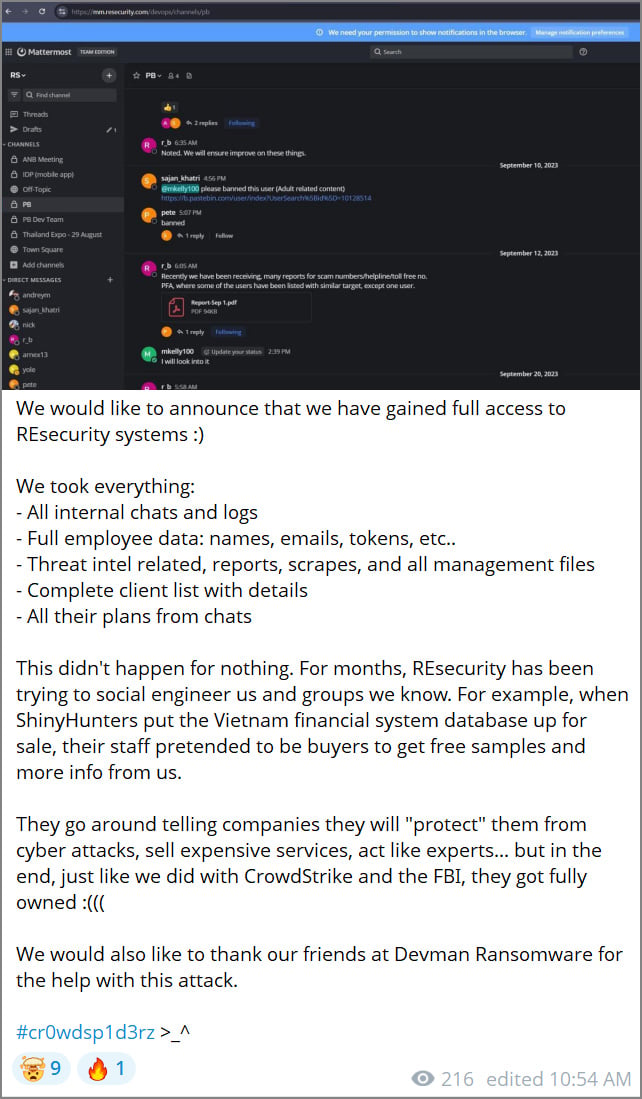
Recently, the threat actors released screenshots on Telegram showcasing the alleged breach, asserting that they pilfered employee data, internal communications, threat intelligence reports, and client details.

“We are pleased to announce that we have successfully infiltrated REsecurity systems,” declared the group on Telegram, claiming to have obtained “all internal chats and logs,” “complete employee data,” “threat intelligence reports,” and a “comprehensive list of clients with associated details.”
Source: BleepingComputer
As evidence of their claims, the threat actors shared screenshots they allege were taken from Resecurity, including what seems to be a Mattermost collaboration instance displaying communications between Resecurity staff and Pastebin personnel concerning malicious content on the platform.
The threat actors, self-identifying as “Scattered Lapsus$ Hunters” due to purported connections between ShinyHunters, Lapsus$, and Scattered Spider threat actors, stated that the breach was in retaliation for what they perceive as ongoing efforts by Resecurity to manipulate the group socially and gather intelligence on their activities.
The threat actors alleged that Resecurity employees posed as buyers during a purported sale of a Vietnamese financial system database, seeking complimentary samples and additional details.
Post-article release, a spokesperson from ShinyHunters informed BleepingComputer that they were not involved in the incident. While ShinyHunters had previously claimed association with Scattered Lapsus$ Hunters, they clarified that they played no part in this attack.
The article has been updated to reflect this new information.
For any information regarding this incident or other undisclosed attacks, you can reach us confidentially via Signal at 646-961-3731 or at tips@bleepingcomputer.com.
Resecurity’s Honeypot Defense
Resecurity contradicts the claims made by the threat actors, asserting that the breached systems were not part of their authentic production infrastructure but were actually a honeypot set up to attract and monitor malicious actors.
Following BleepingComputer’s inquiry, Resecurity shared a report from December 24, detailing their detection of a threat actor probing their exposed systems on November 21, 2025.
The company’s DFIR team promptly identified reconnaissance indicators and traced multiple IP addresses associated with the actor, including those from Egypt and Mullvad VPN services.
Resecurity responded by deploying a honeypot account within a controlled environment, allowing the threat actor to interact with fabricated employee, customer, and payment data while under surveillance by researchers.
A honeypot serves as a baited, monitored system or account designed to attract attackers for observation, analysis, and intelligence-gathering without jeopardizing real data or infrastructure.
The honeypot was populated with synthetic datasets mimicking real-world business information, including over 28,000 synthetic consumer records and more than 190,000 synthetic payment transaction records generated from Stripe’s official API format.
According to Resecurity, the threat actor attempted to automate data exfiltration in December, initiating over 188,000 requests between December 12 and December 24 using numerous residential proxy IP addresses.
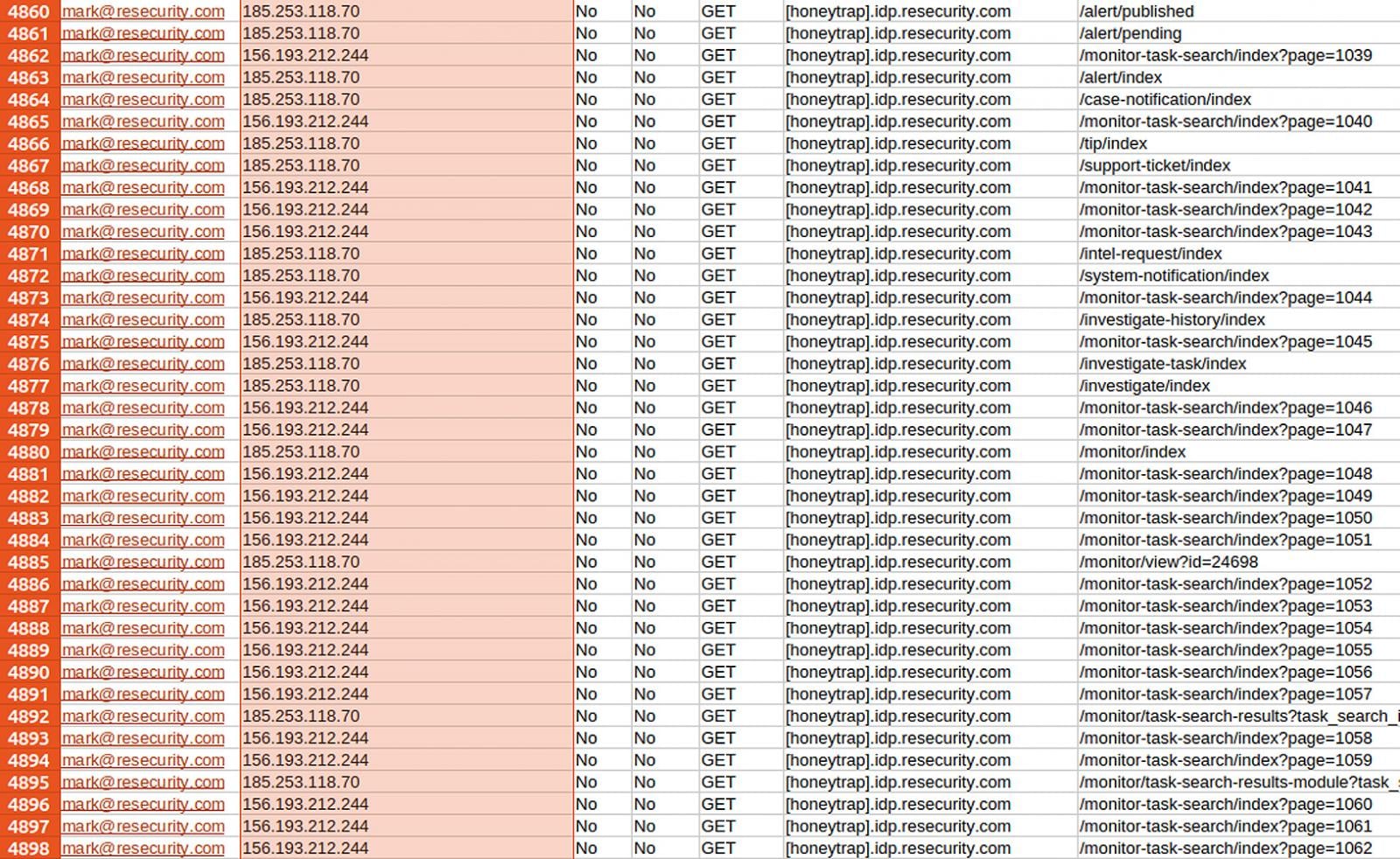
Source: Resecurity
Resecurity reported that the threat actor inadvertently exposed confirmed IP addresses multiple times due to proxy connection failures, with the information relayed to law enforcement.
Further synthetic datasets were added by Resecurity to study the attacker’s behavior, leading to additional operational security (OPSEC) failures and aiding in pinpointing the threat actor’s infrastructure.
“Upon identifying the actor through network intelligence and timestamps, a foreign law enforcement entity, a Resecurity partner, submitted a subpoena request regarding the threat actor,” Resecurity revealed.
As of the current moment, the threat actors have not presented additional evidence, merely teasing in a recent Telegram post that more information will be divulged soon.
“Nice damage control Resecurity. More information coming soon!,” the Telegram post reads.

As MCP (Model Context Protocol) gains prominence for linking LLMs to tools and data, security teams are swiftly enhancing the safety of these new services.
This complimentary cheat sheet outlines 7 best practices that you can implement today.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS































