Security
Hackers Unleashed: Researchers Hijack Malware Control Panels

The Rise of StealC Malware: Unveiling the Vulnerabilities
Security researchers recently uncovered a critical cross-site scripting (XSS) flaw in the web-based control panel utilized by operators of the notorious StealC info-stealing malware. This vulnerability provided a gateway for researchers to monitor active sessions and gather vital intelligence on the attackers’ hardware configurations.
StealC first emerged onto the cybercrime scene in early 2023, aggressively promoted through dark web channels. Its popularity soared due to its sophisticated evasion techniques and extensive data theft capabilities.
Over the years, the developer of StealC continued to enhance the malware’s capabilities. The release of version 2.0 in April introduced features such as Telegram bot support for real-time alerts and a new builder that could customize StealC builds based on templates and rules for data theft.
Following the leak of the malware’s administration panel source code, researchers seized the opportunity to analyze its inner workings.
CyberArk researchers identified an XSS vulnerability that allowed them to extract browser and hardware fingerprints of StealC operators, monitor active sessions, pilfer session cookies, and remotely hijack panel sessions.
By exploiting this vulnerability, the researchers gleaned insights into the threat actors’ computer characteristics, including location indicators and hardware details.
Moreover, they successfully retrieved active session cookies, granting them control over sessions from their own machines.
Source: CyberArk
For security reasons, CyberArk refrained from disclosing specific details about the XSS vulnerability to prevent prompt fixes by StealC operators.
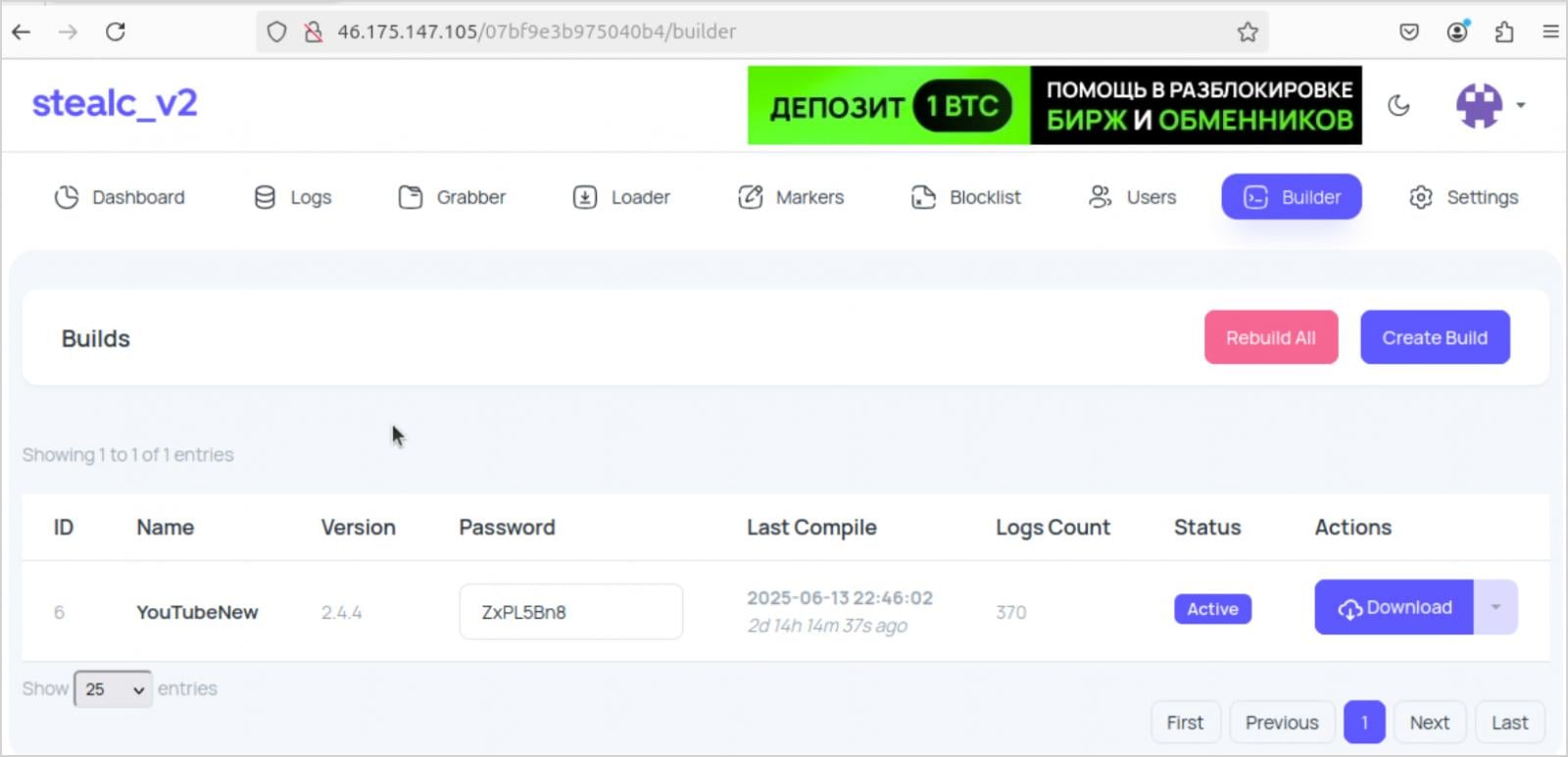
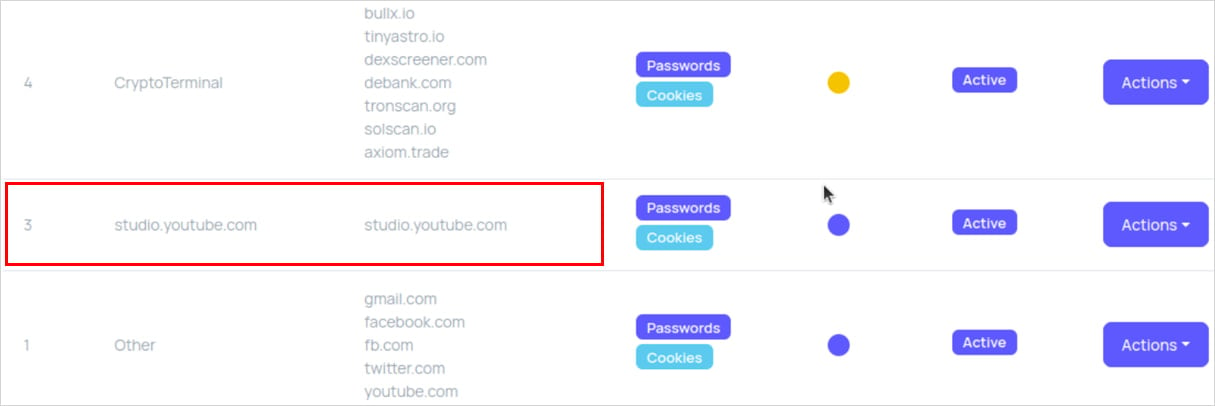
The report spotlighted a case involving a StealC customer known as ‘YouTubeTA’, who illicitly seized control of old YouTube channels using compromised credentials and disseminated infecting links.
Throughout 2025, this cybercriminal conducted malware campaigns, amassing over 5,000 victim logs, stealing approximately 390,000 passwords, and harvesting 30 million cookies, most of which were non-sensitive.
Source: CyberArk
Analysis of screenshots from the threat actor’s panel indicated a high incidence of infections when victims searched for cracked versions of Adobe Photoshop and Adobe After Effects.
By leveraging the XSS flaw, researchers were able to discern that the attacker operated on an Apple M3-based system with English and Russian language settings, utilized the Eastern European time zone, and connected to the internet via Ukraine.
The threat actor’s location was inadvertently exposed when they failed to route the StealC panel through a VPN, revealing their true IP address associated with Ukrainian ISP TRK Cable TV.
CyberArk emphasized the risks associated with malware-as-a-service (MaaS) platforms, highlighting the potential for rapid scalability but also the vulnerability to exposure for threat actors.
In response to a surge in StealC operators, CyberArk strategically chose to disclose the XSS flaw to disrupt the operations, prompting a reevaluation of the malware’s usage within the MaaS market.

As Model Context Protocol (MCP) gains traction as the standard for connecting LLMs to tools and data, security teams are swiftly adopting best practices to ensure the safety of these new services.
Download our free cheat sheet outlining 7 best practices for immediate implementation.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS































