Security
Mac Users Beware: GlassWorm Malware Threatens Crypto Wallet Security

A new surge in the “GlassWorm” cyber attack campaign has specifically set its sights on macOS developers by distributing malicious VSCode/OpenVSX extensions that contain modified versions of cryptocurrency wallet applications.
Extensions found in the OpenVSX registry and the Microsoft Visual Studio Marketplace enhance the functionalities of a VS Code-compatible editor by integrating additional features, tools, language support, or themes to boost productivity.
The Microsoft marketplace functions as the official extension hub for Visual Studio Code, while OpenVSX provides an open and vendor-neutral alternative primarily utilized by editors that do not support or opt not to rely on Microsoft’s proprietary marketplace.

The introduction of GlassWorm malware was observed within the marketplaces in October, concealed within malicious extensions that used “invisible” Unicode characters.
Once these extensions were installed, the malware aimed to pilfer credentials for GitHub, npm, and OpenVSX accounts, along with cryptocurrency wallet data from various extensions. Furthermore, it facilitated remote access through VNC and could redirect traffic through the victim’s device using a SOCKS proxy.
Despite being exposed publicly and facing heightened defenses, GlassWorm reemerged in early November on OpenVSX and resurfaced once more in early December on VSCode.
Resurgence of GlassWorm on OpenVSX
Researchers at Koi Security uncovered a fresh GlassWorm offensive targeting exclusively macOS systems, a shift from the previous campaigns that focused solely on Windows.
In contrast to the invisible Unicode tactics seen in the initial two waves or the compiled Rust binaries utilized in the third wave, the most recent GlassWorm attacks involve an AES-256-CBC–encrypted payload embedded in compiled JavaScript within the OpenVSX extensions:
- studio-velte-distributor.pro-svelte-extension
- cudra-production.vsce-prettier-pro
- Puccin-development.full-access-catppuccin-pro-extension
The malicious code executes after a 15-minute delay, likely to evade detection in sandboxed environments.
Instead of using PowerShell, the malware now employs AppleScript and relies on LaunchAgents for persistence instead of Registry modifications. The command-and-control (C2) mechanism based on the Solana blockchain remains unchanged, with researchers noting an overlap in infrastructure as well.
In addition to targeting over 50 browser-based crypto extensions, developer credentials (GitHub, NPM), and browser data, GlassWorm now also endeavors to steal Keychain passwords.
Moreover, it has introduced a novel capability wherein it checks for hardware cryptocurrency wallet applications such as Ledger Live and Trezor Suite on the host system and replaces them with tampered versions.
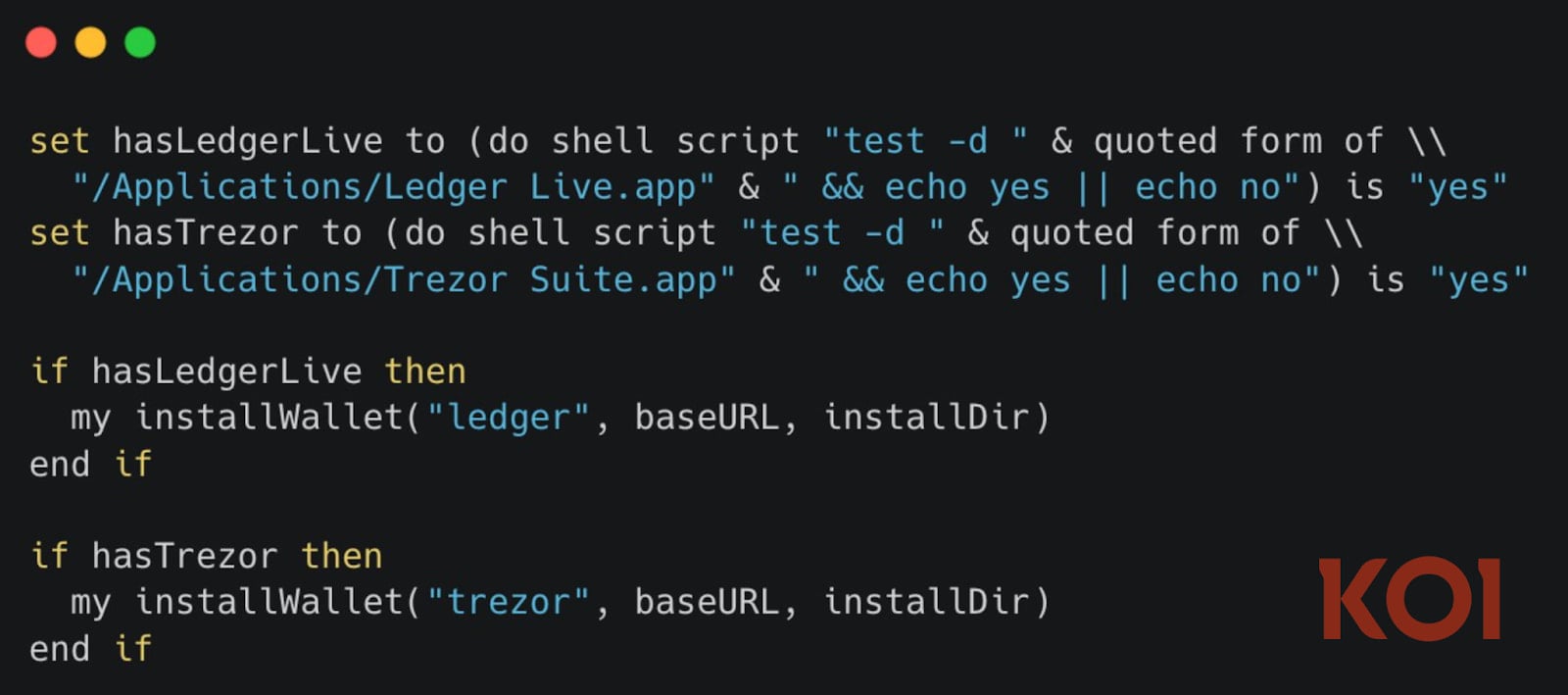
Source: Koi Security
However, Koi Security notes that this particular functionality is presently ineffective as the tampered wallets are returning empty files.
“This could indicate that the attacker is still in the process of preparing the macOS wallet trojans, or the infrastructure is undergoing a transition,” elucidates Koi Security.
“The capability is fully developed and ready – it’s just awaiting the upload of payloads. All other malicious operations (credential theft, keychain access, data extraction, persistence) remain fully operational.”
Upon verifying the availability of the malicious extensions on OpenVSX, BleepingComputer noted a warning for two of them, cautioning that their publisher was unverified.

Source: BleepingComputer
The download counts indicate more than 33,000 installations, though such figures are often manipulated by threat actors to confer a sense of reliability to the files.
Developers who have installed any of the aforementioned extensions are strongly advised to promptly uninstall them, reset their GitHub account passwords, revoke NPM tokens, scrutinize their systems for signs of compromise, or consider reinstalling the operating system.

As budget planning season approaches, gain insights from over 300 CISOs and security leaders on their strategies, spending priorities, and plans for the upcoming year. This comprehensive report provides valuable benchmarks, identifies emerging trends, and allows for comparison of priorities as we head into 2026.
Discover how top leaders are translating investments into tangible outcomes.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook3 months ago
Facebook3 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook3 months ago
Facebook3 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS