Security
Malicious ClickFix Exploits App-V Scripts to Infect Windows Devices

New ClickFix Attacks Exploit Windows App-V Scripts to Distribute Malware
A recent malicious campaign has combined the ClickFix technique with a fake CAPTCHA and a signed Microsoft Application Virtualization (App-V) script to deliver the Amatera infostealing malware.
The Microsoft App-V script acts as a living-off-the-land binary, using a trusted Microsoft component to execute PowerShell and mask malicious activities.
Microsoft Application Virtualization allows applications to run in isolated virtual environments without actual installation on the system.
Past incidents have seen App-V scripts used to evade security solutions, but this marks the first instance of such a file being utilized in ClickFix attacks to distribute an information stealer.
BlackPoint Cyber reports that the attack commences with a fake CAPTCHA verification, prompting victims to manually execute a command via the Windows Run dialog.
.jpg)
Source: BlackPoint
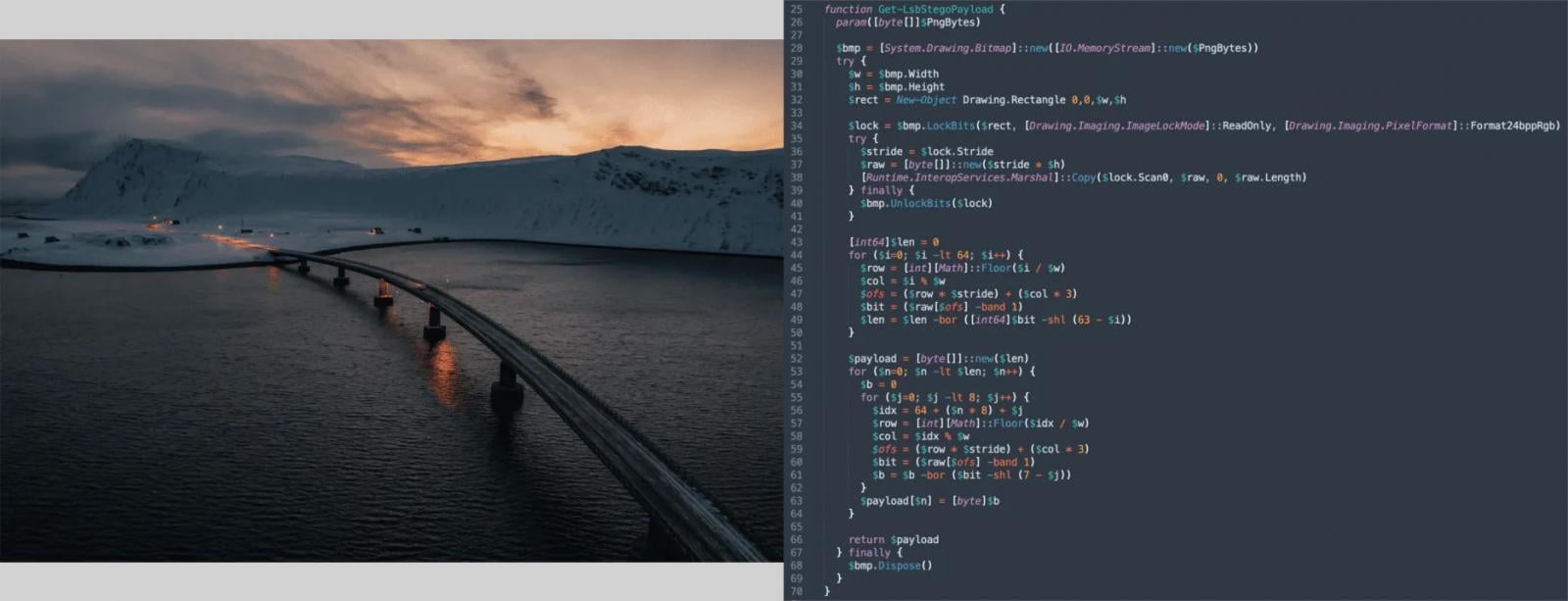
The command leverages the legitimate SyncAppvPublishingServer.vbs App-V script to execute PowerShell, ensuring that the user manually executes it.
BlackPoint Cyber researchers note that if the execution is detected in an analysis environment, it stalls silently to potentially thwart automated analysis resources.
Once the conditions are met, the malware retrieves configuration data from a public Google Calendar file containing encoded values.
In subsequent stages, a hidden PowerShell process is spawned via the Windows Management Instrumentation framework, decrypting and loading multiple payloads into memory.
Source: BlackPoint
Payload data is decrypted, decompressed, and executed in memory, launching the Amatera infostealer.
.jpg)
Source: BlackPoint
Post-infection, the malware connects to a designated IP address to retrieve mappings and additional payloads via HTTP POST requests.
Amatera is classified as an infostealer that targets browser data and credentials, based on the ACR infostealer with evolving sophistication and available as malware-as-a-service.
Defense measures include restricting Windows Run dialog access, removing unnecessary App-V components, enabling PowerShell logging, and monitoring outbound connections for anomalies.

Explore our guide for secure secrets management and AI-generated code practices to fortify your team’s development processes.
Download the cheat sheet now to streamline your security practices.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook3 months ago
Facebook3 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook3 months ago
Facebook3 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS































