Security
Record $21 Billion Lost to Cybercrime by Americans in 2021

Recent data from the Federal Bureau of Investigation (FBI) reveals that U.S. victims fell prey to cyber-enabled crimes, resulting in nearly $21 billion in losses last year. This staggering amount was primarily driven by various types of fraudulent activities such as investment scams, business email compromise, tech support fraud, and data breaches.
The figures indicate a concerning upward trend, with a 26% increase compared to 2024, when losses amounted to $16.6 billion. Additionally, the number of complaints received by the Internet Crime Complaint Center (IC3) exceeded 1 million in the past year, a significant rise from the 859,000 complaints filed the year before.

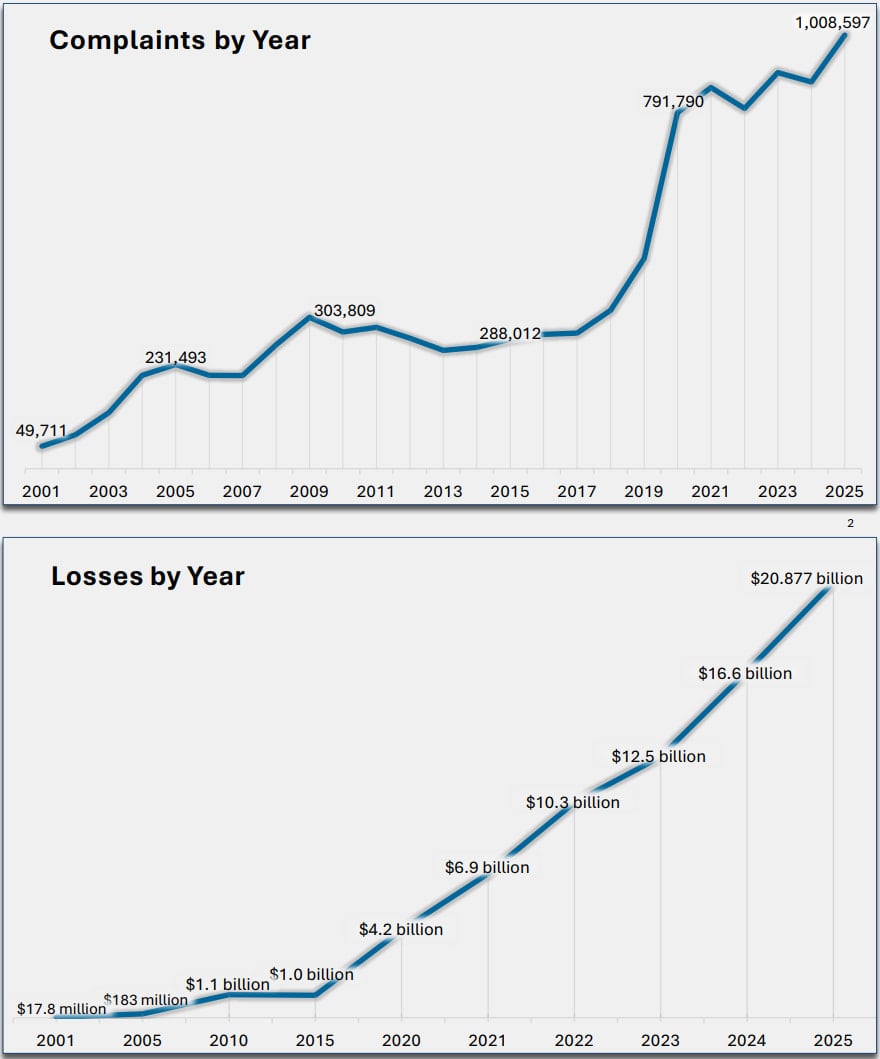
Source: FBI
Last year, the most common complaints reported included phishing attacks (191,000 cases), extortion (89,000 cases), and investment scams (72,000 cases), which collectively contributed to substantial financial losses. Additionally, there were notable reports of serious cyber threats such as business email compromise (24,700 cases), data breaches (3,900 cases), ransomware attacks (3,600 cases), and SIM swapping incidents (971 cases).
Among the various scam types, investment fraud accounted for 49% of all incidents and led to losses amounting to $8.6 billion. However, the most significant financial impact was attributed to cybercrime targeting cryptocurrency, resulting in losses exceeding $11 billion across 181,565 cases.
Cyber-enabled fraud was prevalent in 453,000 complaints, contributing to a total loss of $17.7 billion reported to the IC3 in 2025. Notably, individuals over the age of 60 were disproportionately affected, reporting losses of $7.7 billion, marking a 37% increase from the previous year.
Including AI-related scams for the first time in its report, the FBI highlighted 22,300 complaints related to such schemes, resulting in losses of $893 million. These scams involved tactics like voice cloning, fake profiles, forged documents, and deepfake videos.
Additionally, the FBI classified two incidents targeting critical infrastructure (such as dams and nuclear facilities) as data breaches, underscoring the severity of cyber threats faced by essential sectors. The most targeted critical infrastructure sectors in 2025 included healthcare, manufacturing, financial services, information technology, and government facilities.
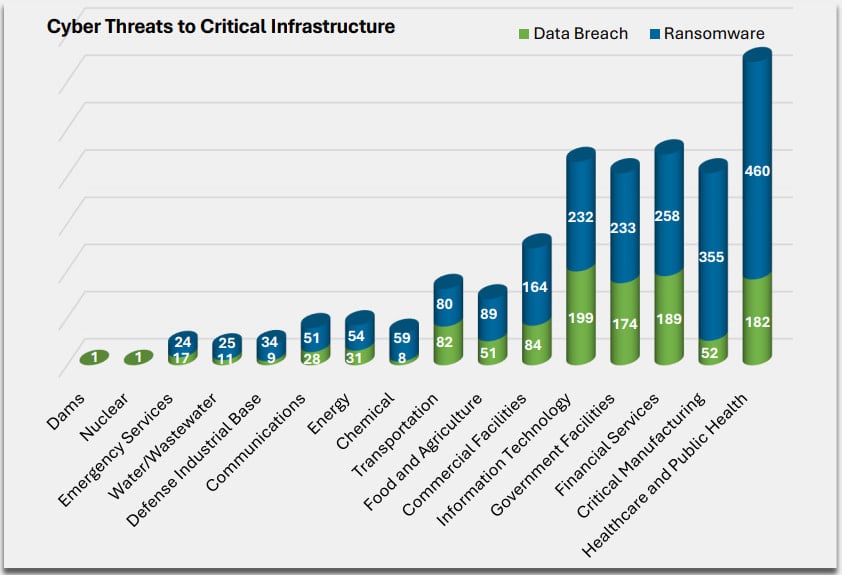
Source: FBI
FBI’s Countermeasures
To combat the rising tide of cybercrime, the FBI has intensified its efforts to thwart attacks, alert victims, and freeze illicitly acquired funds, with successful recovery in some cases. In 2025, the agency launched 3,900 Financial Fraud Kill Chain (FFKC) interventions, effectively blocking fraudulent transactions and freezing $679 million of the targeted $1.16 billion.
One notable initiative included ‘Operation Level Up,’ a proactive approach aimed at preventing financial losses due to cryptocurrency investment fraud. By notifying 3,780 victims last year, the FBI managed to alert 78% of individuals who were unaware of being targeted by scammers.
The FBI emphasizes the importance of vigilance when faced with urgent requests or pressure tactics, urging individuals to verify the authenticity of communications before sharing sensitive information or making financial transactions. Suspected incidents of hacking or scams should be promptly reported to ic3.gov for investigation.

Automated penetration testing demonstrates existing vulnerabilities, while Breach and Attack Simulation (BAS) evaluates the effectiveness of security controls. It’s crucial to combine both approaches for comprehensive security testing.
Explore our whitepaper detailing six validation surfaces, identifying coverage gaps, and offering three key questions for evaluating security tools.
-

 Facebook6 months ago
Facebook6 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple6 months ago
Apple6 months agoMeta discontinues Messenger apps for Windows and macOS