Security
Resurgent Gootloader Malware Unleashes Fresh Tactics Following 7-Month Hiatus
Gootloader Malware Operation Resumes with SEO Poisoning Tactics
After a 7-month hiatus, the notorious Gootloader malware loader operation has resurfaced, utilizing SEO poisoning to drive traffic to fake websites distributing the malicious software.
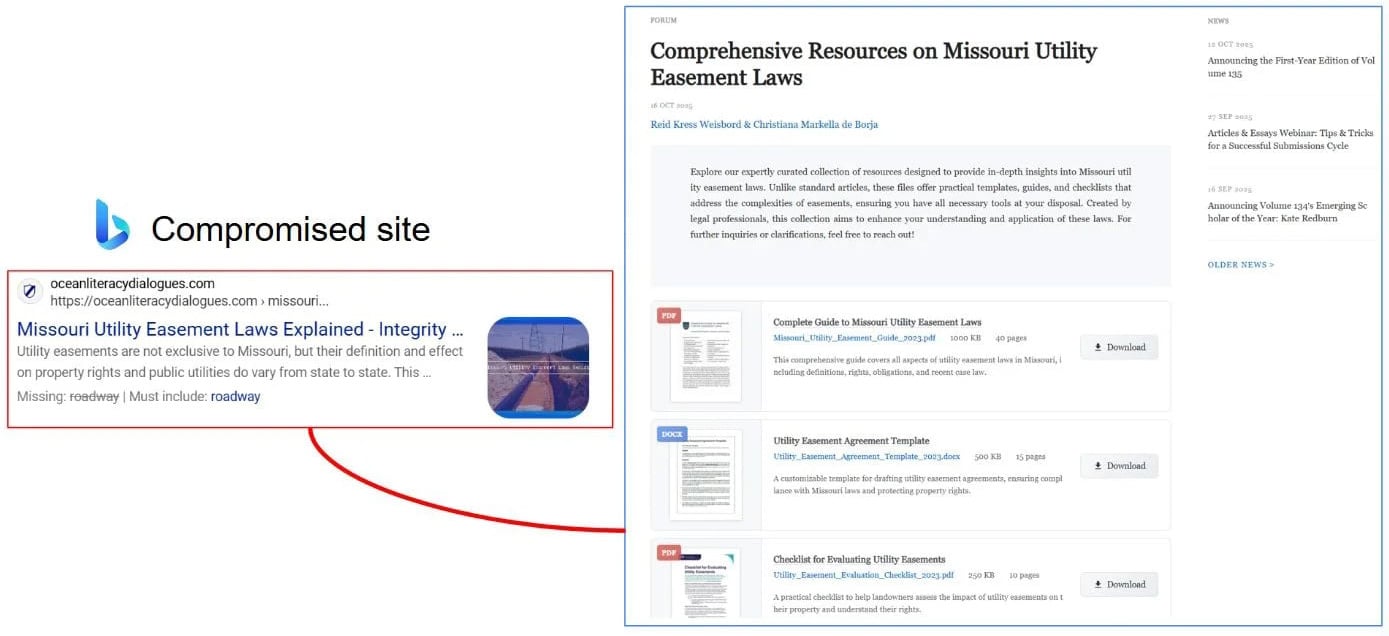
Gootloader, a JavaScript-based malware loader, is disseminated through compromised or attacker-controlled websites. It tricks users into downloading harmful documents by posing as legitimate content.
These nefarious websites are promoted in search engines through ads or SEO poisoning techniques. SEO poisoning involves manipulating search engine results to boost a website’s ranking for specific keywords, such as legal documents and agreements.

Source: Gootloader researcher
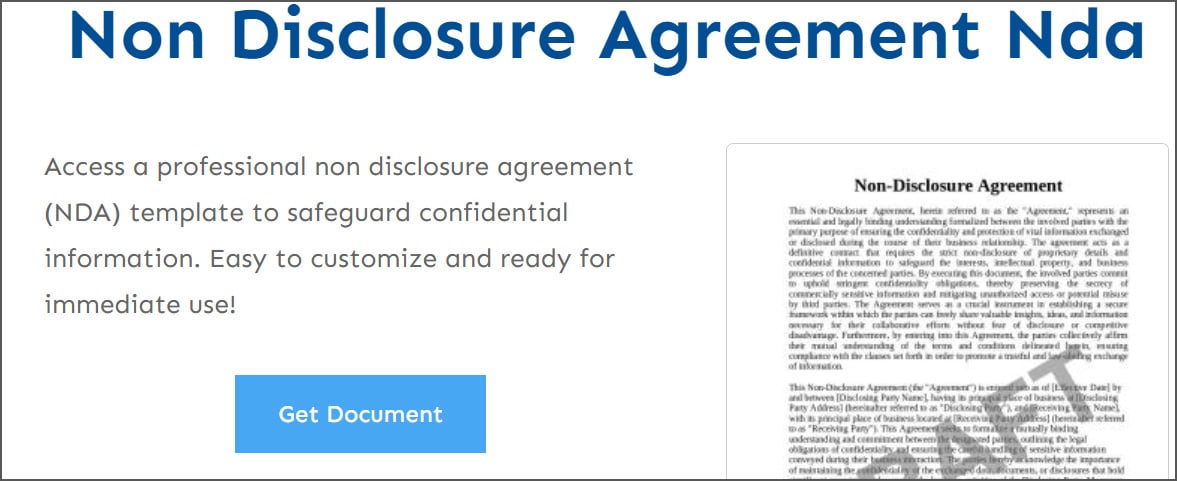
Initially, these deceptive websites featured fake message boards simulating user discussions, with some posts recommending malicious document templates for download. Subsequently, the SEO campaigns transitioned to websites offering free templates for various legal documents.
Source: Gootloader researcher
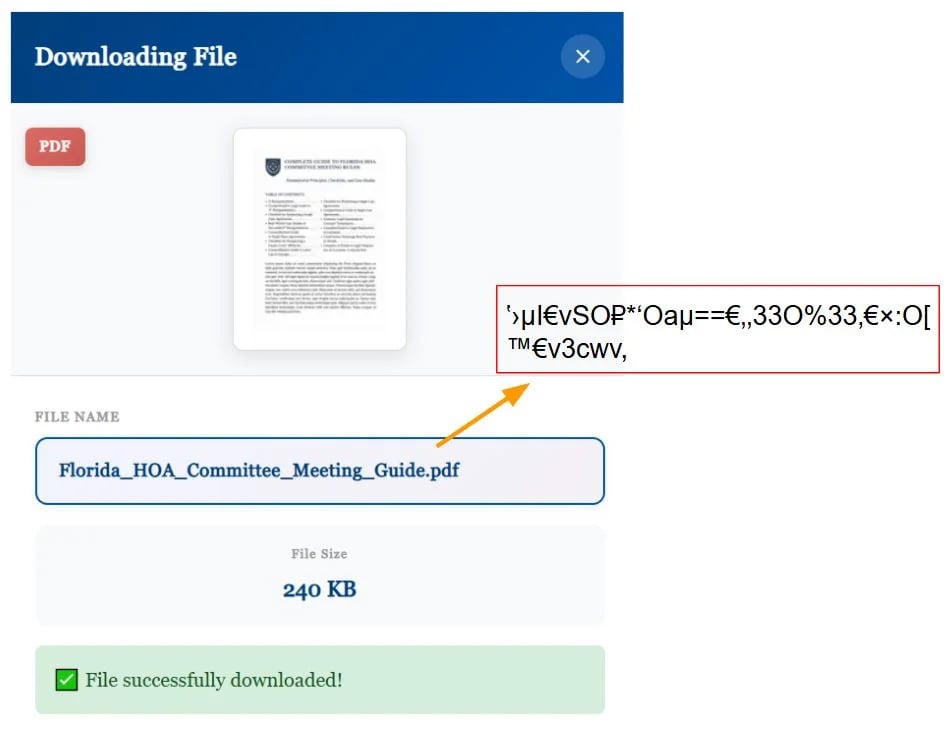
Upon clicking the “Get Document” button, visitors unknowingly triggered the download of a malicious document archive, often disguised with a .js extension. For instance, a file named mutual_non_disclosure_agreement.js could be included in the archive.
Upon opening the downloaded document, Gootloader executed and installed additional malware payloads on the device, including Cobalt Strike, backdoors, and bots facilitating unauthorized access to corporate networks. Subsequently, threat actors leveraged this access to deploy ransomware or launch other cyberattacks.
Gootloader’s Resurgence
An anonymous cybersecurity researcher known as “Gootloader” has been actively monitoring and disrupting the malware operation by reporting abuse to ISPs and hosting platforms, leading to a temporary halt on March 31st, 2025.
Recently, Gootloader, in collaboration with Anna Pham from Huntress Labs, identified a new campaign wherein the malware operation once again masquerades as legal documents.
According to the Gootloader researcher, the latest campaign features thousands of unique keywords spread across 100 websites, all designed to lure victims into downloading a malicious ZIP archive containing a JScript (.JS) file. This file establishes initial access for subsequent malicious activities, often culminating in ransomware deployment.
Source: Huntress Labs
However, this new variant employs evasion techniques to thwart automated analysis tools and security researchers. Huntress Labs discovered that malicious websites use JavaScript to obfuscate filenames by utilizing a special web font that substitutes letters with visually similar symbols.
While the HTML source code displays gibberish text, the rendered page shows normal words due to the font’s swapped glyph shapes, complicating the detection of keywords like “invoice” or “contract” in the source code.
Researchers noted that the font’s metadata appears legitimate, mapping characters to corresponding glyphs with swapped vector paths. This technique renders the text unreadable in the source code but legible on the screen, enhancing the malware’s stealth.
Source: Huntress Labs
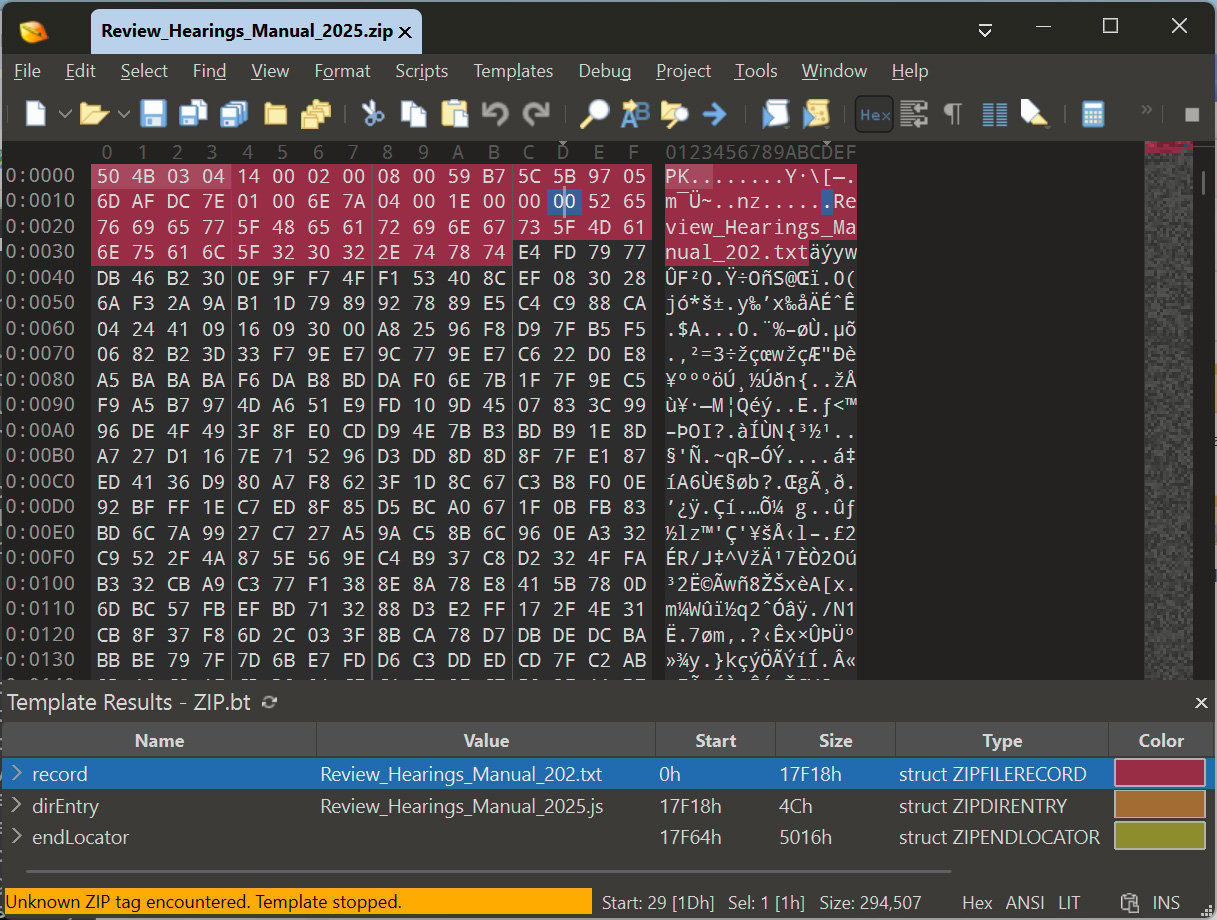
Furthermore, the DFIR Report uncovered that Gootloader leverages malformed Zip archives to distribute its scripts through attacker-controlled websites. These archives are designed in a way that, when extracted with different tools, produce varying outcomes.
For instance, extracting the ZIP file with Windows Explorer may reveal a malicious JavaScript file named Review_Hearings_Manual_2025.js, while other tools extract a harmless text file named Review_Hearings_Manual_202.txt.
The inconsistency in extraction methods poses a challenge for analysts, raising questions about the malware’s evolving tactics and potential new techniques.
Source: BleepingComputer
As Gootloader resurfaces, it is observed dropping the Supper SOCKS5 backdoor on infected devices to establish remote access to networks. This backdoor, utilized by ransomware affiliates like Vanilla Tempest, enables threat actors to conduct unauthorized activities.
Vanilla Tempest, a notorious ransomware affiliate associated with various cyberattacks, including Inc, BlackCat, Quantum Locker, Zeppelin, and Rhysida, swiftly escalates its attacks post-infection. Within a short timeframe, the threat actor conducts reconnaissance and compromises critical network components, underscoring the urgency for heightened vigilance among consumers and corporate entities.
With the resurgence of Gootloader, users are advised to exercise caution when downloading legal agreements and templates online. Unless a website is reputable and known for providing such content, it is prudent to approach unfamiliar sources with skepticism to mitigate the risk of falling victim to malicious activities.

Empower your team with essential insights on secrets management and AI-generated code security. Download the cheat sheet for a secure development process.
Unlock the secrets to robust cybersecurity practices. Download now!
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook3 months ago
Facebook3 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook3 months ago
Facebook3 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS