Security
Rhadamanthys Infostealer Foiled: Cybercriminals Locked Out of Server

Disruption of Rhadamanthys Infostealer Operation: What You Need to Know
The Rhadamanthys infostealer operation recently faced a major disruption, leading to several “customers” of the malware-as-a-service reporting a loss of access to their servers.
Rhadamanthys is a type of infostealer malware designed to pilfer credentials and authentication cookies from various applications such as browsers and email clients. It is commonly distributed through deceptive campaigns masquerading as software cracks, malicious search advertisements, or even YouTube videos.
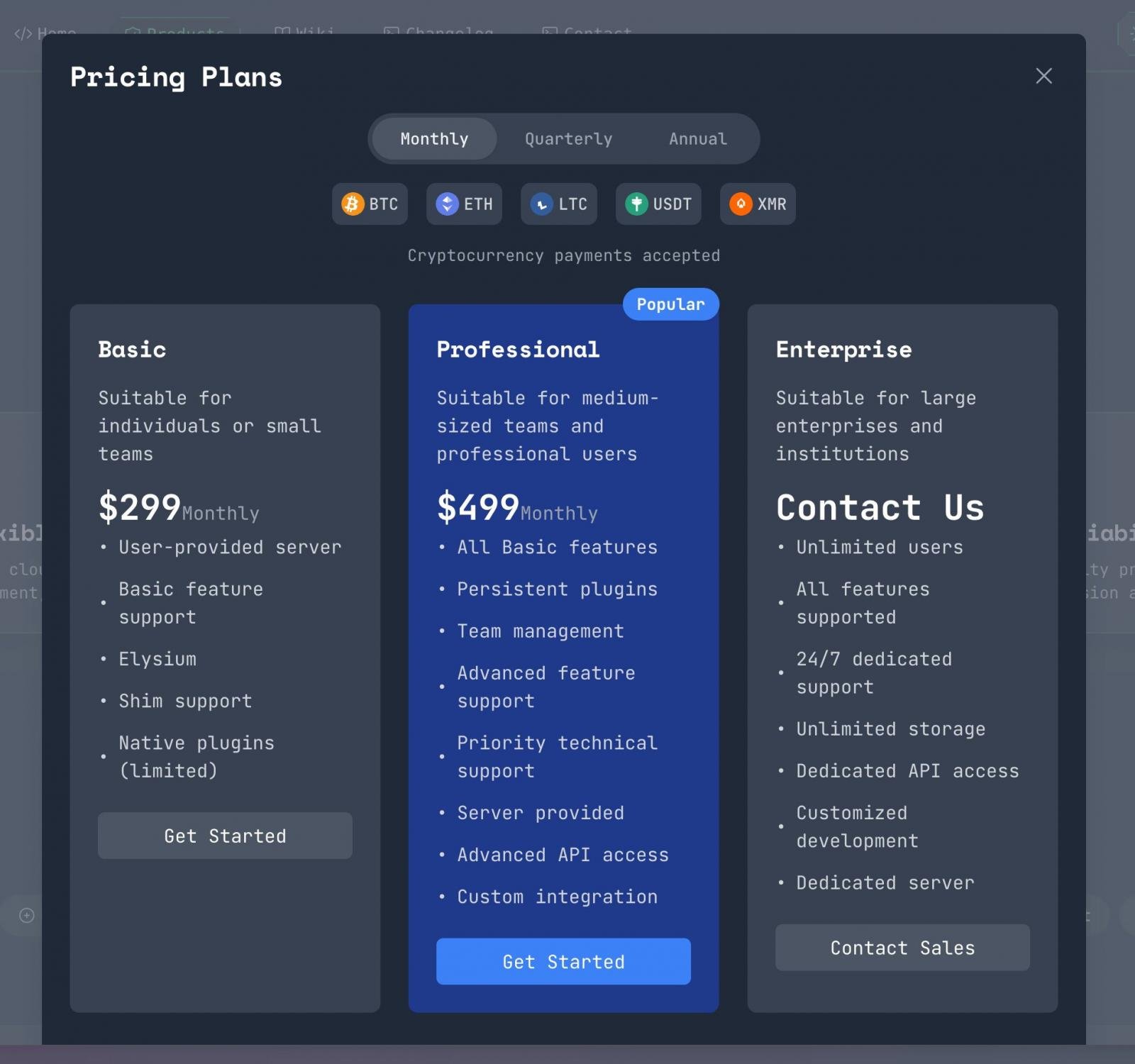
This malware operates on a subscription model, where cybercriminals pay a monthly fee to the developer in exchange for access to the malware, support, and a web panel used to gather stolen data.

According to cybersecurity researchers g0njxa and Gi7w0rm, who monitor malware operations like Rhadamanthys, law enforcement authorities reportedly gained access to the web panels of cybercriminals involved in the operation.
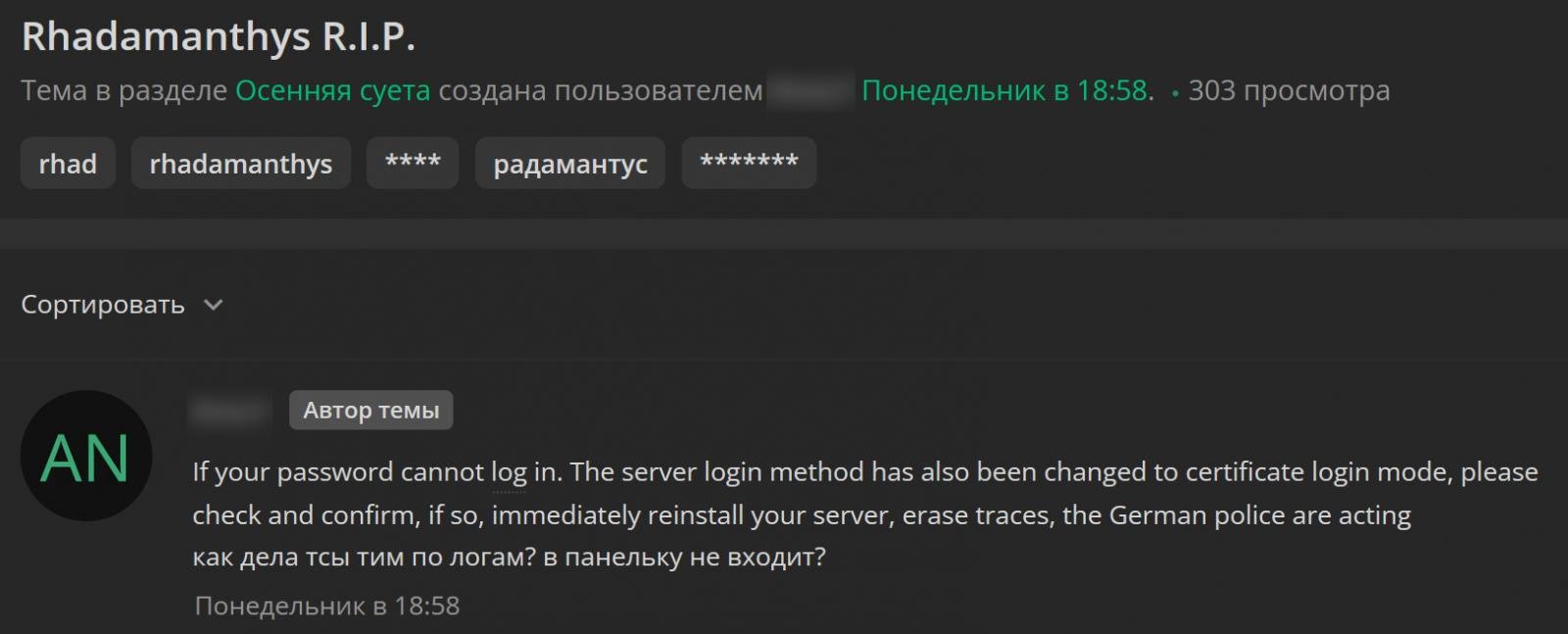
On a hacking forum, some customers mentioned losing SSH access to their Rhadamanthys web panels, which now require a certificate for logging in instead of the usual root password.
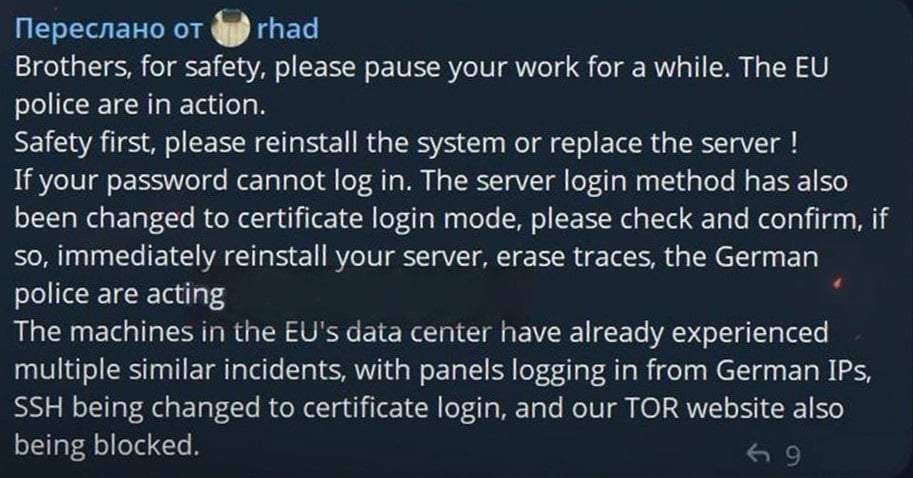
One customer wrote, “If your password cannot log in. The server login method has also been changed to certificate login mode, please check and confirm, if so, immediately reinstall your server, erase traces, the German police are acting.”
Another Rhadamanthys subscriber shared similar issues, with their server now requiring certificate-based logins for SSH access.
“I confirm that guests have visited my server and the password has been deleted. Server login became strictly certificate-based, so I had to immediately delete everything and power down the server. Those who installed it manually were probably unscathed, but those who installed it through the ‘smart panel’ were hit hard,” another subscriber mentioned.
A message from the Rhadamanthys developer suggested that German law enforcement might be behind the disruption, as web panels hosted in EU data centers had German IP addresses logging in before cybercriminals lost access.
Further investigations revealed that the Tor onion sites for the malware operation are currently offline, raising questions about the entity responsible for the disruption.
Several researchers speculate that this disruption could be linked to an upcoming announcement from Operation Endgame, a law enforcement initiative targeting malware-as-a-service operations.
Operation Endgame has a history of successfully disrupting various cyber threats, including ransomware infrastructure and other malware operations like AVCheck, SmokeLoader, DanaBot, IcedID, Pikabot, Trickbot, Bumblebee, Smokeloader, and SystemBC.
The Operation Endgame website features a countdown timer, hinting at new developments to be revealed on Thursday.
Despite attempts to reach out to German police, Europol, and the FBI for comments, there has been no response as of yet.

As MCP (Model Context Protocol) becomes the standard for connecting LLMs to tools and data, security teams are moving fast to keep these new services safe.
This free cheat sheet outlines 7 best practices you can start using today.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS







![Apple verification server issue breaking local app installation for developers [U]](https://bennetttechinnovation.com/wp-content/uploads/2026/03/Developers-Face-Hurdles-with-Apple-Verification-Server-Local-App-Installation-400x240.jpg)
![Apple verification server issue breaking local app installation for developers [U]](https://bennetttechinnovation.com/wp-content/uploads/2026/03/Developers-Face-Hurdles-with-Apple-Verification-Server-Local-App-Installation-80x80.jpg)






















