Security
Securing the Future: Implementing Identity Threat Detection as the Cornerstone of Your Security Strategy in 2026

In today’s cybersecurity landscape, attackers have evolved from breaking into systems to logging in with compromised accounts. To combat this growing threat, organizations must have comprehensive visibility into IT events. Identity Threat Detection is a crucial tool that enables the identification of suspicious activities and the prevention of attacks.
Defending Against the Primary Threat
Identity-based attacks, such as phishing emails and social engineering, have become the most prevalent form of threat faced by businesses. These attacks, which are often automated and scalable, can easily bypass traditional security measures. Even a single successful attack out of numerous attempts can have catastrophic consequences for an organization.
Once an attacker gains access to a network account, they can quickly move laterally, escalate privileges, and execute devastating actions without detection.
Transitioning from Risk Mitigation to Proactive Defense
While implementing measures like email filters, multi-factor authentication, and access controls can reduce the risk of attacks, no prevention method is foolproof. Organizations must be prepared to detect and respond to breaches swiftly. This shift from reactive to proactive security requires a focus on Identity Security as a core component of the overall strategy.
Identity Threat Detection & Response (ITDR) provides the necessary visibility to monitor and act on security incidents effectively.
Tenfold offers a comprehensive solution for managing user accounts and IT privileges, integrating Identity Governance and Identity Security seamlessly. By leveraging advanced logging and event auditing capabilities, organizations can enhance their security posture without incurring additional costs.
Schedule a personalized tenfold demo to experience the platform in action!
Understanding Your Adversaries and Users
ITDR enables real-time monitoring and analysis of IT events across systems, empowering organizations to track user activities and detect anomalies promptly. By establishing baseline behavior patterns, security teams can identify deviations indicative of malicious intent.
Recognizing unusual IT events, such as spikes in login attempts or unauthorized access to privileged accounts, allows for immediate investigation and response to potential threats.
It is crucial to err on the side of caution when dealing with suspicious activities, as swift action can prevent serious security incidents.
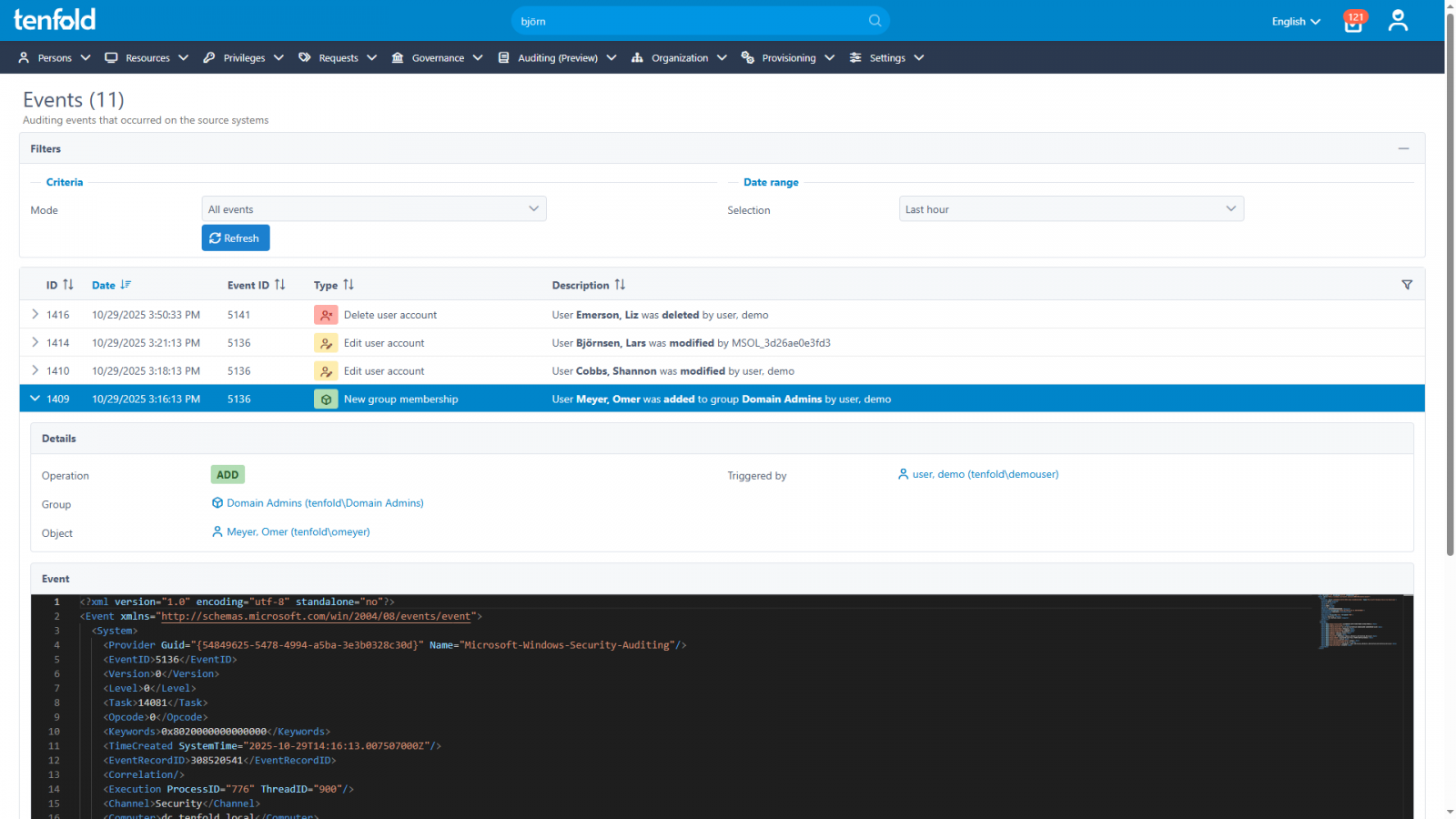
Tenfold: Empowering Governance and Event Auditing
As organizations strive to enhance their Identity Security strategy, tenfold offers a unified platform encompassing Identity Governance, Data Access Governance, and Event Auditing. This integrated approach enables automated onboarding processes, granular permission management, access reviews, and rapid response to security incidents.
Take the first step towards bolstering your Identity Threat Detection capabilities with tenfold’s intuitive platform, designed for easy deployment and operation.
Discover more about tenfold by scheduling a tailored walkthrough of our solution today.
This article is sponsored and authored by Tenfold Software.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook3 months ago
Facebook3 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS