Security
Security Alert: Post SMTP WordPress Plugin Vulnerability Allows Hackers to Hijack Admin Accounts

Hackers Exploit Critical Vulnerability in Post SMTP Plugin to Hijack WordPress Admin Accounts
Security experts have issued a warning regarding a critical security flaw in the Post SMTP plugin, a popular email delivery solution used by over 400,000 WordPress websites. Hackers have been actively exploiting this vulnerability to gain unauthorized access to administrator accounts.
Post SMTP, known for its advanced features and reliability as a replacement for the default ‘wp_mail()’ function, has fallen prey to a severe vulnerability that could lead to complete site compromise.
Discovered by security firm Wordfence on October 11, the vulnerability, identified as CVE-2025-11833, scored a high severity level of 9.8. It affects all versions of Post SMTP from 3.6.0 and earlier.
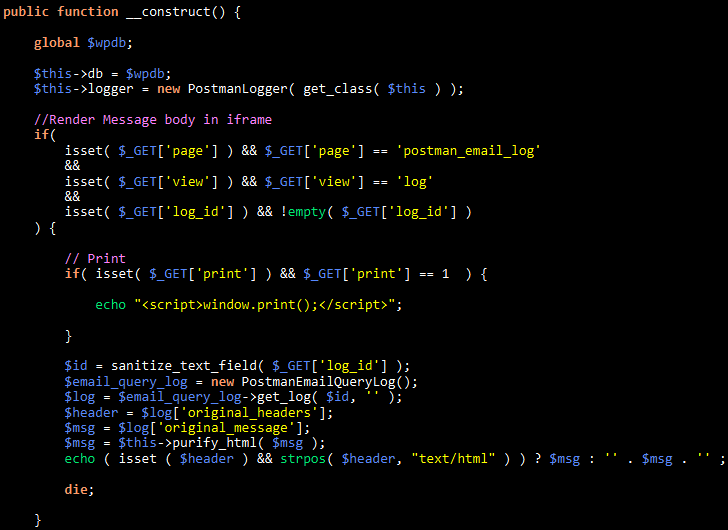
The vulnerability lies in the ‘PostmanEmailLogs’ flow within the plugin, specifically in the ‘construct’ function, where the absence of proper authorization checks allows attackers to view sensitive email content without authentication.

Exploiting this vulnerability enables threat actors to access password reset emails, allowing them to change administrator passwords without proper authorization, ultimately leading to complete account takeover.
After validating the exploit on October 15, Wordfence promptly notified the plugin developer, Saad Iqbal. A fix was released on October 29 with version 3.6.1 of Post SMTP. However, data from WordPress.org indicates that only half of users have updated, leaving approximately 210,000 sites vulnerable to attacks.
Since the emergence of CVE-2025-11833, hackers have been actively exploiting the vulnerability, with Wordfence blocking over 4,500 exploit attempts on its customers since November 1.
Website owners using Post SMTP are strongly advised to update to version 3.6.1 immediately or disable the plugin to mitigate the risk of unauthorized access.
Notably, this isn’t the first time Post SMTP has faced security issues. In July, a similar flaw (CVE-2025-24000) allowed hackers to access email logs and potentially take control of administrator accounts. This emphasizes the importance of staying vigilant and promptly addressing security vulnerabilities.
Source: Wordfence

As the Model Context Protocol (MCP) gains prominence in connecting LLMs to tools and data, security measures are crucial to safeguard these services. Download our free cheat sheet outlining 7 best practices for enhanced security.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS






























