Tech News
Software Development HIPAA Compliance Checklist: Ensuring Data Security and Privacy

by Parth Pandya
by Parth Pandya
Healthcare data breaches are a significant source of identity theft, with 95% of cases originating from stolen healthcare records. This is why compliance with the Health Insurance Portability and Accountability Act (HIPAA) is crucial for software development in the USA. Healthcare software solutions handle a vast amount of patient data, making it essential for healthcare IT providers to ensure that their software is HIPAA-compliant.
HIPAA-compliant software is vital for protecting patient privacy, preventing identity theft, reducing legal and financial risks, preventing discrimination, and maintaining trust. By adhering to HIPAA standards, software developers can ensure that patients’ data remains secure and protected.
However, achieving HIPAA compliance goes beyond just encryption; it also involves implementing secure coding practices, managing access effectively, responding to incidents promptly, overseeing vendors, and continuously monitoring the system.

This comprehensive blog offers a detailed HIPAA compliance checklist for developers in 2026, covering administrative, technical, and physical safeguards, practical steps for building compliant software, common mistakes to avoid, and frequently asked questions.
It provides developers with the necessary information upfront, enabling them to select a HIPAA-compliant software development company to create healthcare software that aligns with HIPAA regulations.
Key Takeaways
- HIPAA is a U.S. federal law that establishes standards to safeguard the privacy and security of electronic Protected Health Information (ePHI).
- HIPAA compliance is governed by key rules, including Privacy, Security, Breach Notification, and Enforcement, which directly impact the design and operation of healthcare software.
- Covered Entities and Business Associates must adhere to HIPAA regulations, including healthcare organizations and software vendors that create, store, or process ePHI.
- HIPAA-compliant software requires administrative, technical, and physical safeguards, such as risk assessments, access controls, encryption, audit logging, and secure infrastructure.
- HIPAA compliance is an ongoing effort that necessitates continuous monitoring, risk management, vendor oversight, and secure development practices.
What Is HIPAA?
The Health Insurance Portability and Accountability Act (HIPAA) is a U.S. federal law enacted in 1996 to set national standards, aiming to protect patient health information (PHI) from being disclosed without consent.
It mandates rules for healthcare providers, insurers, and related entities (Covered Entities) to secure electronic health records (ePHI) and manage patient data, giving individuals the right to their health info.
HIPAA ensures that patients’ medical information remains confidential, accurate, and secure while allowing legitimate access for healthcare operations. It improves the efficiency of healthcare systems and standardizes electronic health transactions while ensuring privacy and data security.
HIPAA Compliance Rules Overview
The HIPAA compliance rules include the privacy rule, security rules, notification rule, and more. A software development company willing to build software that adheres to HIPAA compliance needs to follow these rules. Here’s how:
HIPAA Privacy Rule
This rule of HIPAA compliance governs how Protected Health Information (PHI) is used and disclosed. It allows patients the right to access, correct, and obtain copies of their medical information.
Patients can inspect a copy of the data and request alterations if necessary. The HIPAA Privacy Rule ensures that software handling PHI respects confidentiality and consent rules.
HIPAA Security Rule
This rule focuses on keeping electronic PHI (ePHI) secure by mandating administrative, physical, and technical safeguards. The security rule of HIPAA involves secure user authentication, encryption, audit controls, and risk management processes. This rule applies to covered entities and business associates, such as health plans, healthcare providers, healthcare clearinghouses, and subcontractors.
HIPAA Enforcement Rule
This rule establishes how the U.S. Department of Health and Human Services (HHS) enforces the HIPAA law. It determines accountability and imposes penalties for non-compliance, including fines and potential criminal charges. The Office for Civil Rights (OCR) conducts enforcement when a data breach occurs.
HIPAA Breach Notification Rule
This HIPAA compliance rule requires covered entities and business associates to notify affected individuals, HHS, and sometimes the media in case of a PHI breach.
The HHS has defined elements that constitute a breach based on the volume and type of PHI involved, the type of disclosure, and more. A timely and documented breach response is crucial for software teams.
What Is the Importance of HIPAA?
HIPAA compliance is crucial for protecting patient privacy, preventing identity theft, reducing legal and financial risks, and more. Here’s how:
- Protects Patient Privacy: HIPAA compliance prevents the misuse of sensitive medical information related to patients.
- Prevents Identity Theft: It secures ePHI against unauthorized access for patients’ well-being.
- Reduces Legal and Financial Risk: Adhering to HIPAA compliance helps avoid hefty fines and reputational damage.
- Prevents Discrimination: HIPAA compliance protects individuals with chronic conditions from being denied insurance or facing bias when changing jobs.
- Maintains Trust: Patients and healthcare partners trust platforms that handle data responsibly.
Who Needs to Be HIPAA-Compliant?
HIPAA compliance applies to Covered Entities (healthcare providers, health plans, clearinghouses) and their business associates (third-party vendors like IT, billing, and legal) that handle Protected Health Information (PHI).
The rule safeguards patient data for treatment and operations. Any entity creating, receiving, maintaining, or transmitting electronic PHI must comply, even if not traditionally in the healthcare sector but serving a healthcare function.
Below are the types of individuals and organizations subject to the Privacy Rule and considered covered entities:
Healthcare Providers
Every healthcare provider, including hospitals, clinics, telemedicine platforms, pharmacies, dentists, psychologists, and physicians, regardless of the size of their practice, that electronically transmits health information in connection with certain transactions, needs to be HIPAA compliant.
These transactions involve claims, referral authorization requests, benefit eligibility inquiries, and other transactions for which HHS has determined standards under the HIPAA Transactions Rule.
These organizations must prioritize the protection of patient data in electronic health records (EHRs), billing systems, and patient portals.
Health Plans
The following are the health plans that need to be HIPAA compliant:
- Health, vision, dental, and prescription drug insurers
- Health maintenance organizations (HMOs)
- Medicare, Medicaid, Medicare+Choice, and Medicare supplement insurers
- Employer-sponsored group health plans
- Government- and church-sponsored health plans
- Long-term care insurers, excluding nursing home fixed-indemnity policies
- Multi-employer health plans
Note: A group health plan with less than 50 participants administered solely by the establishing and maintaining employer is not covered and would be the exception.
Healthcare Clearinghouses
Organizations that process health information for standardization or translation are liable to be HIPAA compliant.
For example, those entities that process nonstandard information received from another entity into a standard format or vice versa, and healthcare clearinghouses that receive identifiable health information when providing processing services to a health plan or healthcare provider as a business associate need to be HIPAA compliant.
Business Associates
Vendors and software providers that store, transmit, or process ePHI on behalf of covered entities need to adhere to HIPAA compliance.
These include non-members of a covered entity’s workforce using individually identifiable health information for functions of a covered entity that must be HIPAA compliant. These functions, activities, or services include claims processing, data analysis, utilization review, and billing.
These associates must sign Business Associate Agreements (BAAs) and adhere to HIPAA safeguards.
HIPAA Compliance Checklist for Software Development
The HIPAA compliance checklist for software development includes administrative, technical, and physical safeguards. Here is a detailed 2026-ready checklist with explanations and practical guidance to help ensure that you build software that complies with HIPAA regulations:
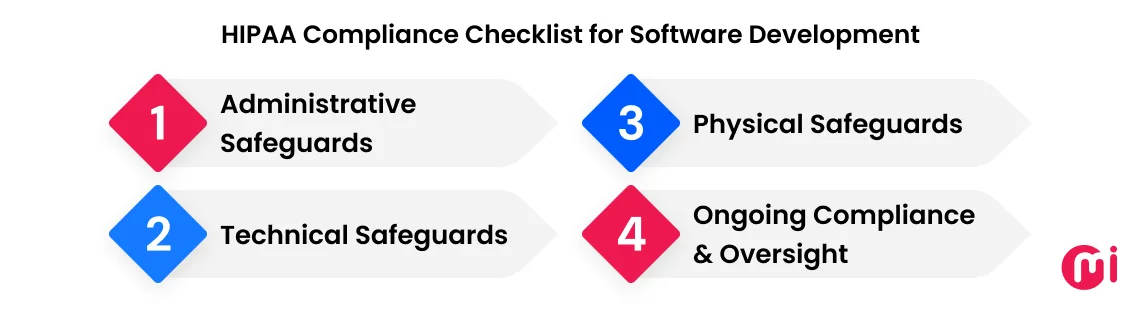
1. Administrative Safeguards (Governance & Accountability)
HIPAA Applicability & Scope Definition
Administrative safeguards begin with understanding the scope of compliance. Software developers working on a project need to know exactly which systems, processes, and personnel handle ePHI.
For example, a telehealth app developer should know exactly which parts of the backend handle patient records, how those records are transmitted to clinicians, and where they are stored in the cloud.
- Identify ePHI Systems: Map databases, cloud storage, APIs, and third-party integrations. This ensures you know which components need HIPAA controls.
- Classify Your Organization: Determine if you are a Covered Entity, like a hospital or insurance company, or a Business Associate, like a SaaS provider handling ePHI.
- Data Flow Mapping: Track how ePHI moves between systems, applications, and external services, enabling you to identify vulnerabilities, unauthorized access points, and compliance gaps.
Security Risk Analysis & Risk Management
A formal security risk assessment is mandatory; therefore, software developers need to identify vulnerabilities, prioritize risks, and implement mitigations.
- Document Risks: Consider identifying threats, like ransomware, unauthorized access, or cloud misconfigurations, and their likelihood and impact on ePHI.
- Mitigation: Apply technical controls, such as encryption, access control, and administrative controls (policies, training) to mitigate these risks.
- Continuous Reassessment: Make sure you repeat assessments after major updates, infrastructure changes, or security incidents.
Pro Tip: Make use of automated scanning tools to identify vulnerabilities in APIs, servers, or dependencies.
Policies, Procedures & Documentation
Policies, procedures, and documentation formalize how your organization protects ePHI. Documentation is critical for audits. For example, you can document how your app encrypts PHI in transit and at rest, and which team is responsible for key rotation.
Policies cover access control, encryption, incident response, and acceptable use, procedures provide step-by-step instructions for developers and IT teams, and documents maintain architecture diagrams, risk logs, and change management records.
Workforce Management & Access Governance
When it comes to the HIPAA compliance checklist, human error emerges as a considerable risk. Therefore, you need administrative safeguards to control who can access ePHI.
For example, a new engineer joining a team should only access the data and environments necessary for development and testing, and the access should be revoked immediately upon departure.
Assign roles and responsibilities clearly, implement user onboarding and offboarding procedures, conduct periodic access reviews to remove unnecessary privileges, and train developers, IT, and support teams on HIPAA security best practices.
Incident Response & Breach Management
To ensure HIPAA compliance for software development, developers must plan for unexpected events, as it mandates a timely response and reporting when any incident of data breach occurs.
Consider maintaining a written incident response plan and defining processes for detection, investigation, containment, and remediation of any incident. What’s more, establish reporting timelines to affected individuals and OCR and preserve evidence for audits and legal purposes.
For example, if a vulnerability exposes PHI, your plan should allow for quick patching, notification to stakeholders, and documentation of the entire incident.
Vendor & Third-Party Risk Management
Business associates (vendors) are likely to introduce risks to ePHI; hence, vendor & third-party risk management is one of the essential elements.
To deal with this issue, identify vendors accessing ePHI and execute Business Associate Agreements (BAAs).
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook3 months ago
Facebook3 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook3 months ago
Facebook3 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS