Security
Stealthy Strikes: LucidRook Malware Threatens NGOs and Universities

New ‘LucidRook’ Malware Targeting NGOs and Universities
A recently discovered Lua-based malware known as LucidRook is currently being utilized in spear-phishing campaigns aimed at non-governmental organizations and universities in Taiwan.
According to researchers at Cisco Talos, the malware has been attributed to a threat group identified internally as UAT-10362, described as a proficient adversary with well-developed operational techniques.
LucidRook was first detected in attacks in October 2025, which involved phishing emails containing password-protected archives.
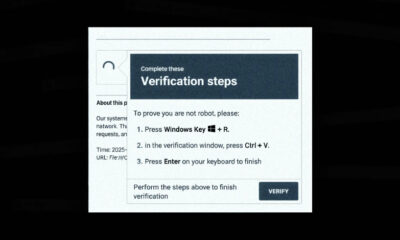
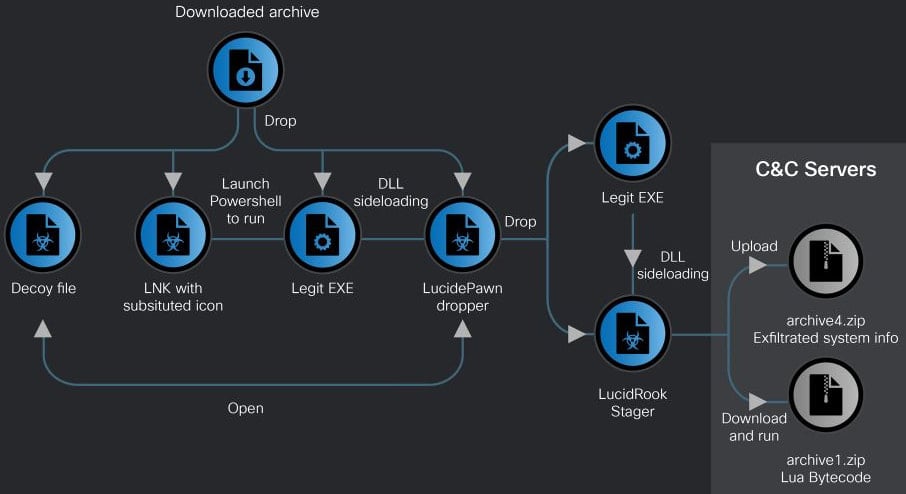
Two distinct infection chains were identified by the researchers. One chain utilized an LNK shortcut file that ultimately delivered the LucidPawn malware dropper, while the other chain was EXE-based and involved a fake antivirus executable posing as Trend Micro Worry-Free Business Security Services.
The LNK-based attack method involved using decoy documents, such as government letters made to appear as if they were from the Taiwanese government, to distract the user.
Source: Cisco Talos
Cisco Talos observed that LucidPawn decrypts and deploys a legitimate executable renamed to mimic Microsoft Edge, alongside a malicious DLL (DismCore.dll) for sideloading LucidRook.
One notable feature of LucidRook is its modular design and built-in Lua execution environment, allowing it to retrieve and execute second-stage payloads as Lua bytecode.
This unique approach enables operators to update functionality without altering the core malware, while also reducing forensic visibility. The extensive obfuscation of the code further enhances its stealth.
Cisco Talos elaborates, stating, “Embedding the Lua interpreter effectively transforms the native DLL into a stable execution platform while enabling the threat actor to customize behavior for each target or campaign by updating the Lua bytecode payload with a lighter and more flexible development process.”
The researchers also noted that the binary is heavily obfuscated across embedded strings, file extensions, internal identifiers, and C2 addresses, complicating reverse-engineering efforts.
During its operation, LucidRook conducts system reconnaissance, gathering information such as user and computer names, installed applications, and running processes.
The collected data is encrypted using RSA, stored in password-protected archives, and then sent to attacker-controlled infrastructure via FTP.
While analyzing LucidRook, Talos researchers discovered a related tool named “LucidKnight,” likely used for reconnaissance purposes.
One intriguing aspect of LucidKnight is its exploitation of Gmail GMTP for data exfiltration, indicating that UAT-10362 maintains a versatile toolkit to meet various operational requirements.
Cisco Talos concludes with medium confidence that the LucidRook attacks form part of a targeted intrusion campaign. However, they were unable to access a decryptable Lua bytecode fetched by LucidRook, thus the specific post-infection actions remain unknown.

Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
-

 Facebook6 months ago
Facebook6 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple6 months ago
Apple6 months agoMeta discontinues Messenger apps for Windows and macOS