Security
Stealthy Tactics: Ransomware Gangs Utilize Shanya EXE Packer to Evade Detection

Ransomware Gangs Embrace Shanya EXE Packer to Conceal EDR Killer Payloads
Numerous ransomware groups have turned to a packer-as-a-service platform known as Shanya to facilitate the deployment of payloads that incapacitate endpoint detection and response (EDR) solutions on targeted systems.
Packer services offer cybercriminals specialized tools to package their malicious payloads in a manner that obscures the malicious code, enabling them to evade detection by most conventional security tools and antivirus engines.
The Shanya packer operation surfaced in late 2024 and has since gained significant traction, with malware instances utilizing it detected in various countries including Tunisia, the UAE, Costa Rica, Nigeria, and Pakistan, according to telemetry data from Sophos Security.
Confirmed ransomware groups leveraging the service include Medusa, Qilin, Crytox, and Akira, with the latter being the most frequent user of the packer service.

Source: Sophos
Understanding the Functionality of Shanya
Threat actors submit their malicious payloads to Shanya, which in turn provides a “packed” version with a custom wrapper utilizing encryption and compression techniques.
The service emphasizes the uniqueness of the resulting payloads, highlighting features such as “non-standard module loading into memory” and “wrapper over the system loaderStub uniqueization,” ensuring each customer receives a relatively unique stub with a distinct encryption algorithm upon purchase.

Source: Sophos
The payload is inserted into a memory-mapped copy of the Windows DLL file ‘shell32.dll,’ which appears valid and normal but has its header and .text section overwritten with the decrypted payload.
While the payload remains encrypted within the packed file, it is decrypted and decompressed entirely in memory and then inserted into the ‘shell32.dll’ copy file without touching the disk.
Sophos researchers discovered that Shanya conducts checks for endpoint detection and response (EDR) solutions by invoking the ‘RtlDeleteFunctionTable’ function in an invalid context, triggering an unhandled exception or crash to disrupt automated analysis before the payload’s full execution.
Disabling Endpoint Detection and Response Solutions
Ransomware groups typically aim to disable EDR tools on the target system before proceeding with data theft and encryption phases of the attack.
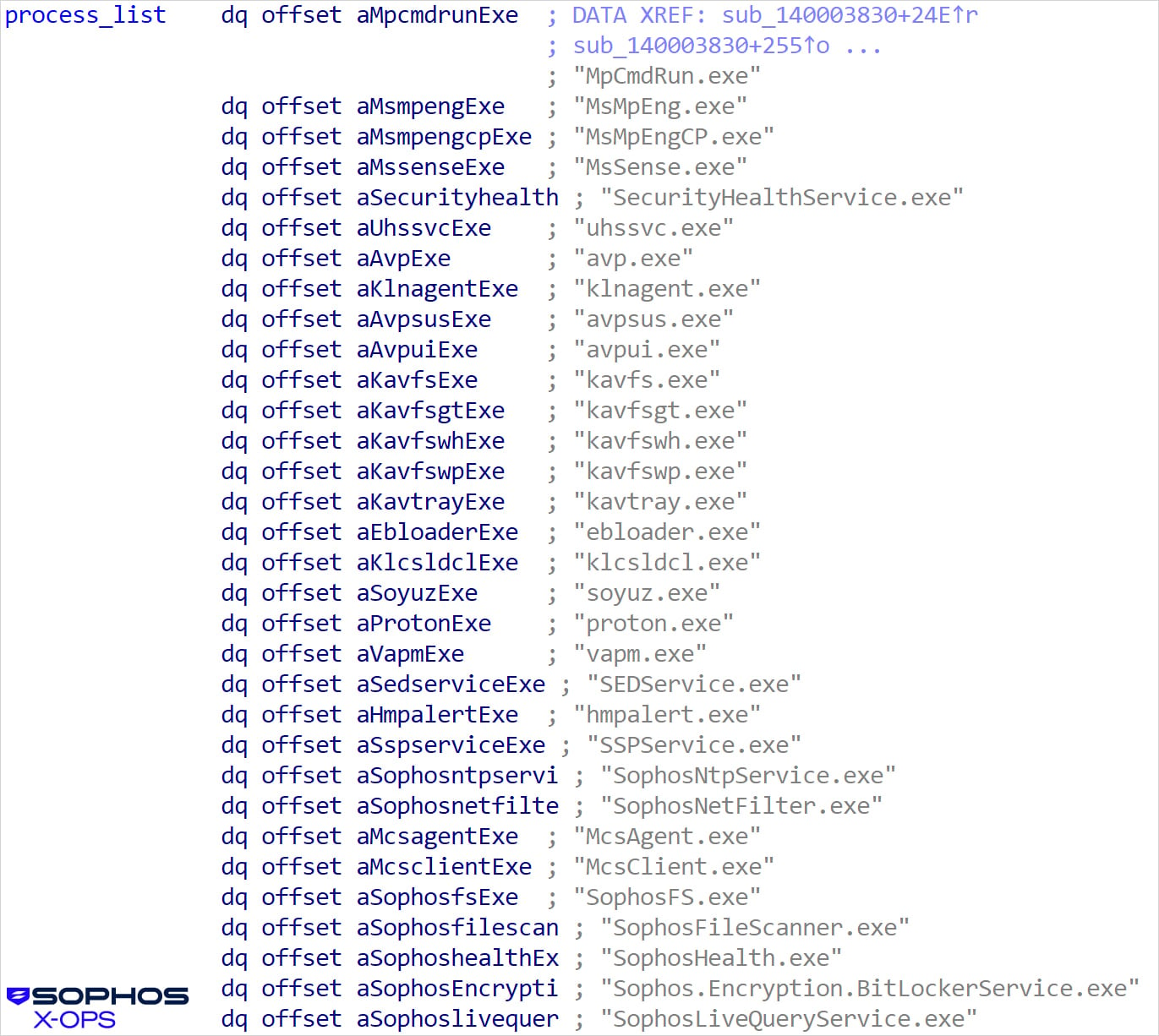
The execution commonly involves DLL side-loading, combining a legitimate Windows executable like ‘consent.exe’ with a Shanya-packed malicious DLL such as msimg32.dll, version.dll, rtworkq.dll, or wmsgapi.dll.
According to Sophos’ analysis, the EDR killer drops two drivers: the legitimately signed ThrottleStop.sys (rwdrv.sys) from TechPowerUp, which contains a vulnerability allowing arbitrary kernel memory writing, and the unsigned hlpdrv.sys.
The signed driver facilitates privilege escalation, while hlpdrv.sys disables security products based on commands received from user mode.
Source: Sophos
In addition to ransomware operators focusing on EDR disabling, Sophos has observed recent ClickFix campaigns utilizing the Shanya service to package the CastleRAT malware.
Sophos highlights that ransomware groups often rely on packer services to prepare EDR killers for deployment without detection.
The researchers offer a detailed technical analysis of some of the payloads packed with Shanya, along with indicators of compromise (IoCs) linked to Shanya-powered campaigns.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook3 months ago
Facebook3 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook3 months ago
Facebook3 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS