Security
Supply-Chain Intrusion: How ‘PlushDaemon’ Hackers Hijacked Software Updates

China-Linked Threat Actor ‘PlushDaemon’ Hijacking Software Update Traffic
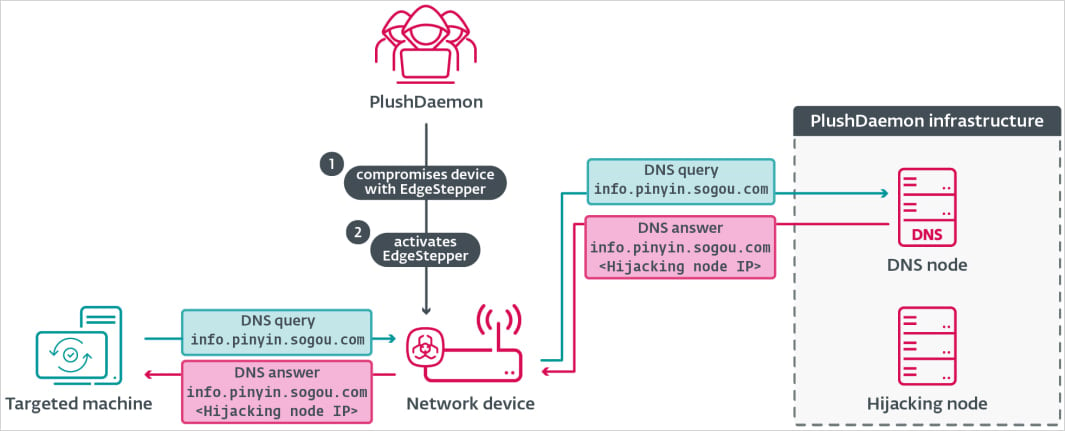
A cyberespionage operation conducted by a threat actor known as ‘PlushDaemon’ with ties to China has been uncovered. This group is utilizing a new implant called EdgeStepper to hijack software update traffic and gain unauthorized access to target networks.
Since 2018, PlushDaemon has been targeting individuals and organizations in various countries, including the United States, China, Taiwan, Hong Kong, South Korea, and New Zealand. They have deployed custom malware, such as the SlowStepper backdoor, to compromise their victims.
Notable targets of PlushDaemon include electronics manufacturers, universities, and a Japanese automotive manufacturing plant in Cambodia. ESET, a cybersecurity firm, has observed that the threat actor has been relying on malicious updates to infiltrate networks since 2019.
.jpg)
Source: ESET
Understanding the Attack Chain
The attack chain employed by PlushDaemon involves gaining access to routers through known vulnerabilities or weak admin passwords. They then install the EdgeStepper implant to redirect software-update traffic to their malicious infrastructure.
EdgeStepper, developed in Golang and compiled as an ELF binary, functions by intercepting DNS queries and redirecting them to a malicious DNS node. This allows the threat actors to control the flow of software updates and deliver their malware.
When a victim attempts to update their software, they unknowingly download the first-stage malware downloader, LittleDaemon, disguised as a DLL file named ‘popup_4.2.0.2246.dll.’
Source: ESET
LittleDaemon establishes communication with the attacker’s node and retrieves a second malware dropper, DaemonicLogistics, which is decrypted and executed in memory.
In the subsequent stage, DaemonicLogistics is utilized to fetch the signature backdoor, SlowStepper, providing the hackers with persistent access to the compromised system.
The SlowStepper backdoor, previously used in attacks targeting users of the South Korean VPN product IPany, enables the threat actors to conduct various malicious activities, including collecting system information, executing file operations, and deploying spyware tools to steal sensitive data.
Researchers emphasize that PlushDaemon’s capabilities allow them to compromise targets globally, highlighting the sophisticated nature of their cyberespionage tactics.
ESET’s report provides detailed insights into the newly uncovered malware and indicators of compromise associated with PlushDaemon’s attacks utilizing the EdgeStepper implant.

As Model Context Protocol (MCP) gains traction as a standard for connecting Local Logic Modules (LLMs) to tools and data, security teams are prioritizing the protection of these services. Download this free cheat sheet outlining 7 best practices to enhance security.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS