Security
Suspicions Arise as ShinyHunters Claim Resecurity Hack was Actually a Honeypot

The Alleged Breach of Resecurity by ShinyHunters: A Detailed Analysis
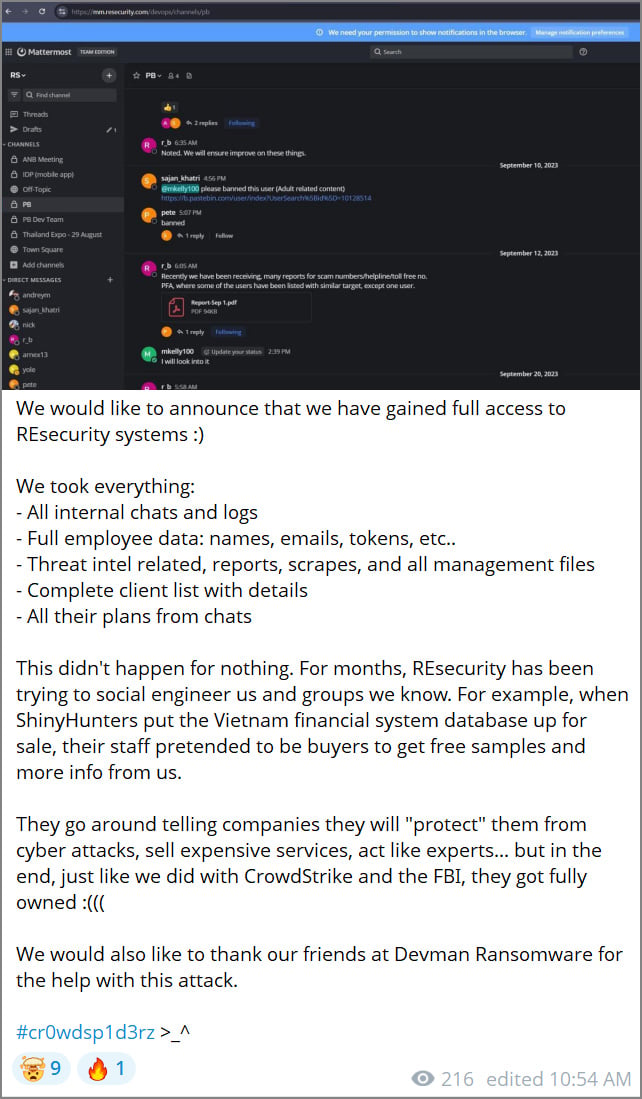
The cybersecurity landscape has been rocked by the recent claims made by the ShinyHunters hacking group regarding their breach of Resecurity. While Resecurity maintains that the attackers only accessed a honeypot containing fake data, the threat actors have published screenshots on Telegram to support their claims.
The alleged breach includes stolen employee data, internal communications, threat intelligence reports, and client information. The group, referring to themselves as “Scattered Lapsus$ Hunters,” asserts that the attack was in retaliation for what they perceive as ongoing attempts by Resecurity to gather information about their operations.

Source: BleepingComputer
The threat actors have also accused Resecurity of engaging in social engineering tactics to gain insight into their activities. They claim that Resecurity employees posed as buyers during the sale of a Vietnam financial system database, seeking free samples and additional information.
If you have any information regarding this incident or other undisclosed attacks, you can contact us confidentially via Signal at 646-961-3731 or at tips@bleepingcomputer.com.
Resecurity’s Perspective: The Honeypot Defense
Resecurity has vehemently denied the claims made by ShinyHunters, asserting that the breached systems were part of a honeypot designed to attract and monitor threat actors. The company detected reconnaissance indicators early and deployed a honeypot to gather intelligence on the attackers.
The honeypot was populated with synthetic datasets resembling real-world business data to lure the threat actors. Resecurity monitored the attacker’s activities, collecting telemetry on their tactics and infrastructure. The company identified servers used for the attack and shared intelligence with law enforcement.
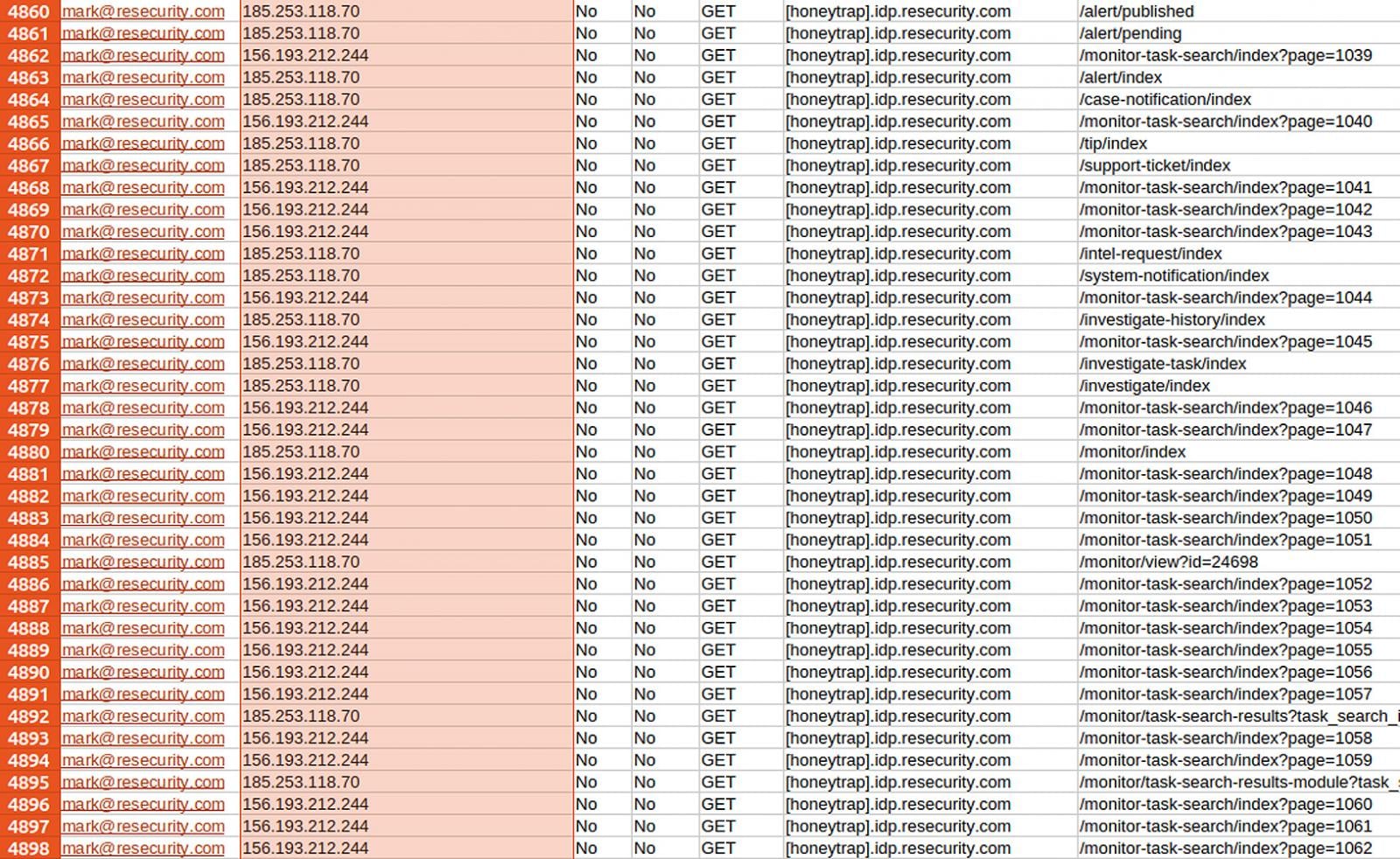
Source: Resecurity
Resecurity’s proactive approach to cybersecurity involved adding fake datasets to study the attacker’s behavior, leading to further intelligence gathering. The company’s efforts resulted in the identification of the threat actor’s infrastructure and subsequent law enforcement involvement.
At the time of writing, ShinyHunters have not provided additional evidence to support their claims. However, they have hinted at the possibility of releasing more information in the future.
“Nice damage control Resecurity. More information coming soon!,” posted the threat actors.

It’s budget season! Over 300 CISOs and security leaders have shared insights on planning, spending, and prioritizing for the year ahead. Learn how top leaders are turning investment into measurable impact.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS
































