


It’s 3:37 am on a Sunday in Los Angeles, and one of the leading financial services firms on the West Coast is experiencing the second week...



University of Pennsylvania Cybersecurity Incident: What Happened? Recently, the University of Pennsylvania faced a cybersecurity breach that led to offensive emails being sent to students and...



Chinese Threat Actors Exploit Microsoft SharePoint Vulnerability to Target Global Organizations Following the public disclosure and patching of the ToolShell security vulnerability in Microsoft SharePoint in...



The Growing Threat of Ransomware and Cyber Attacks on U.S. Critical Infrastructure The Federal Bureau of Investigation (FBI) and the Cybersecurity and Infrastructure Security Agency (CISA)...



The Rise of AI-Powered Cyberattacks: Is India’s BFSI Sector Ready? For those of us who’ve tracked the ever-shifting landscape of cybersecurity, the narrative has always been...



Every week, the cyber world reminds us that silence doesn’t mean safety. Attacks often begin quietly — one unpatched flaw, one overlooked credential, one backup left...
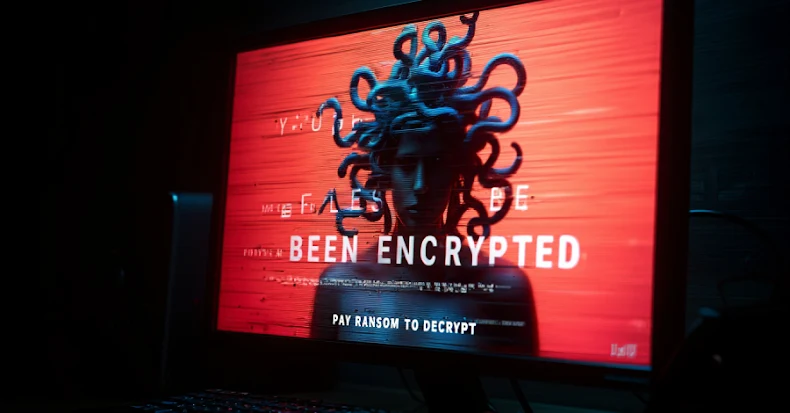

Microsoft Attributes Medusa Ransomware Deployment to Storm-1175 Group Exploiting Fortra GoAnywhere Vulnerability On Monday, Microsoft revealed that the Storm-1175 threat actor group exploited a critical security...



Cybersecurity Firm Attributes Oracle E-Business Suite Exploitation to Threat Actor CrowdStrike has identified the exploitation of a critical security flaw in Oracle E-Business Suite to a...



Steam Removes Game Infected with Cryptocurrency-Draining Malware Recently, Steam took swift action to remove a game from its platform that was found to contain malware capable...
Subscribe to our weekly newsletter below and never miss the latest News or an exclusive offer.