


North Korean APT37 Hackers Deploy New Malware to Breach Air-Gapped Networks In a recent development, North Korean hackers belonging to the state-backed group APT37, also known...



CISA Warns of Dormant RESURGE Malware on Ivanti Devices The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has recently disclosed new information regarding RESURGE, a malicious...



Cybersecurity Researchers Uncover ClickFix Campaign Delivering MIMICRAT Trojan Details have been revealed by cybersecurity researchers regarding a new ClickFix campaign that exploits compromised legitimate websites to...

AI assistants like Grok and Microsoft Copilot, equipped with web browsing and URL-fetching capabilities, have the potential to be misused for command-and-control (C2) activities. Recent research...
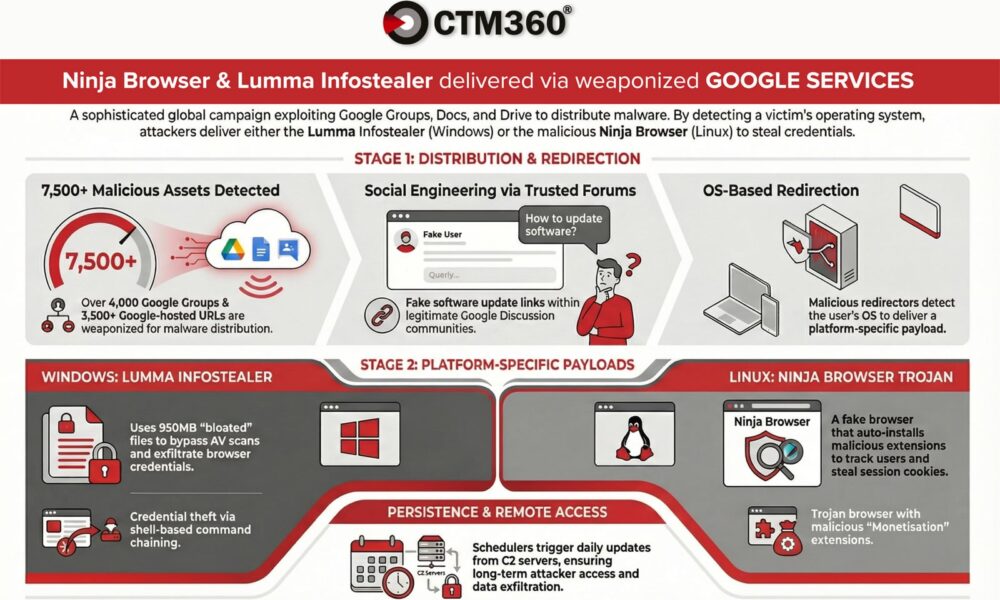

According to CTM360, a recent malware campaign is utilizing over 4,000 malicious Google Groups and 3,500 Google-hosted URLs to target organizations worldwide. Criminals are exploiting Google’s...

into plain text. Cryptocurrency Exchanges Targeted A recent surge in attacks targeting cryptocurrency exchanges has been observed, with threat actors using a combination of phishing and...



This past week brought about multiple subtle indications rather than one major headline, shaping the future of cyber attacks quietly. Researchers observed intrusions originating from mundane...



Hugging Face Platform Abused to Spread Android Malware Recently, a new Android malware campaign has emerged, utilizing the Hugging Face platform as a repository for numerous...



Malware Service “Stanley” Offers Malicious Chrome Extensions A new malware service known as ‘Stanley’ has emerged, offering malicious Chrome extensions that can bypass Google’s review process...



Konni Hackers Target Blockchain Engineers with AI-Generated Malware The North Korean hacker group known as Konni, also identified as Opal Sleet and TA406, has been utilizing...
Subscribe to our weekly newsletter below and never miss the latest News or an exclusive offer.