


Unveiling the Impostors: Lessons from Elmyr de Hory for Cybersecurity Defenders The art world has long grappled with the issue of impostors, drawing parallels to the...



How to Validate Your Mobile App Idea Before Development Starting a mobile app development project without validating your app idea can lead to failure. Research from...



It doesn’t matter who you are or how smart you think you are — nobody is immune to falling for a scam. That’s especially true on...



For individuals who enjoy capturing videos with their iPhone, the significance of sound quality cannot be overstated. Whether you are striving for the perfect shot for...



Architectural Elasticity: The Key to Scaling Intelligent Automation When it comes to scaling intelligent automation without disruption, the focus should be on architectural elasticity rather than...



The Impact of Artificial Intelligence on UI/UX Design In a recent survey conducted by ResearchGate, it was found that 74% of respondents believed that AI would...
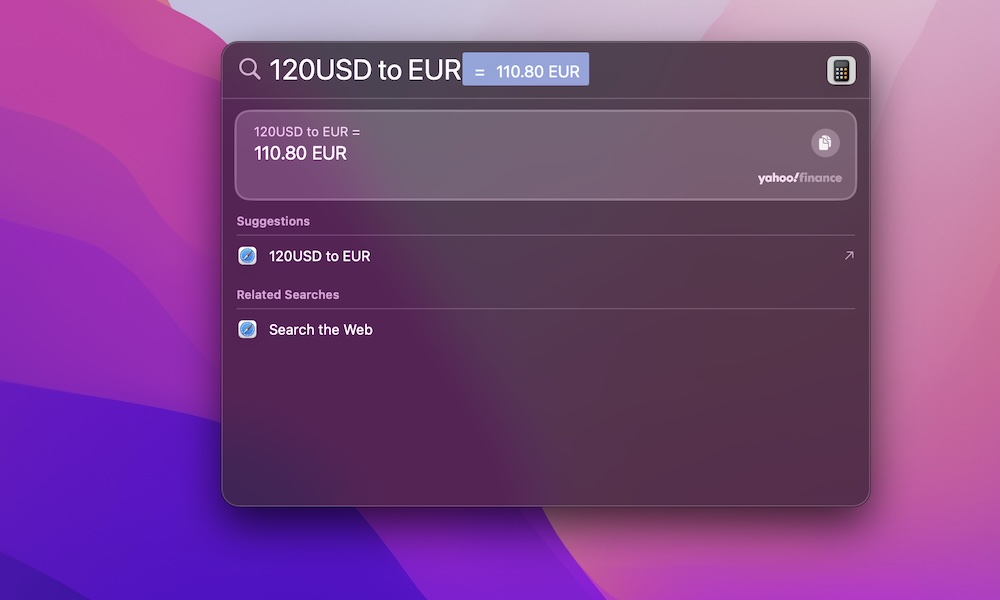

If you’ve spent years on Windows, your hands probably know what to do before your brain finishes the thought. CTRL-C and CTRL-V for copy and paste....



The Ninja Luxe Café Premier is a coffee machine that requires a lot of effort to set up and brew a cup of coffee. It offers...



Scaling Enterprise AI: Overcoming Architectural Oversights Scaling enterprise AI involves addressing architectural oversights that often hinder pilot projects from progressing to production. This challenge extends beyond...



When it comes to cybersecurity, one thing remains constant: adversaries are always evolving. The emergence of offensive AI is revolutionizing attack techniques, making them more difficult...
Subscribe to our weekly newsletter below and never miss the latest News or an exclusive offer.