


In today’s cybersecurity landscape, attackers have evolved from breaking into systems to logging in with compromised accounts. To combat this growing threat, organizations must have comprehensive...
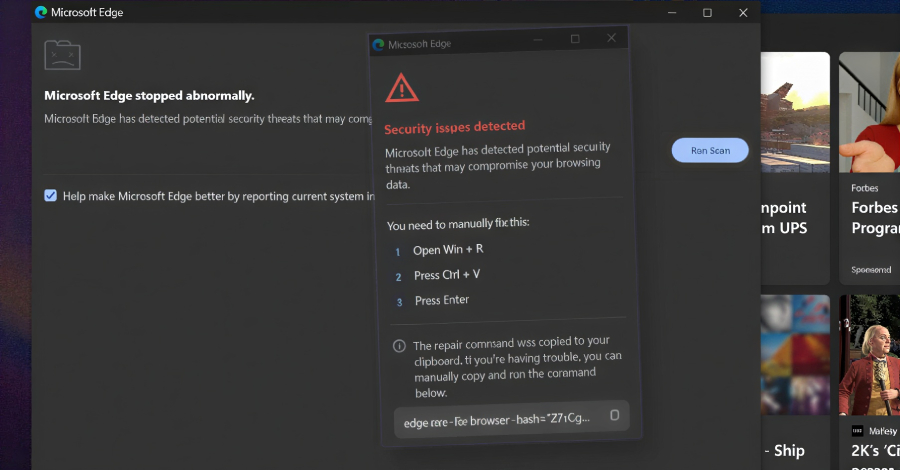


Enhancing Cybersecurity: Understanding KongTuke’s Advanced Tactics After facing a single communication failure, KongTuke employs a reconnection interval of 150 seconds to resume normal operations, showcasing its...



Malicious Chrome Extensions Targeting Enterprise Platforms Discovered Recently, cybersecurity firm Socket uncovered a campaign involving five Chrome extensions on the Chrome Web Store that posed as...



Embrace the Necessity of Maintaining HTML Structure It is crucial to uphold the original HTML structure in order to ensure consistency and accuracy in web content....



Serious Security Flaw Discovered in Bluetooth Devices A recent discovery by researchers from KU Leuven University in Belgium has unveiled a critical security vulnerability present in...



The online world is constantly buzzing with activity. Each week brings new reports of hacks, scams, and security threats cropping up in different corners of the...



Apple recently rolled out the second developer betas of iOS 26.3 and other updates after a holiday break, signaling an imminent public release later this month...



AI Security Concerns in the Enterprise World Artificial Intelligence (AI) agents are designed to streamline tasks, but they are also introducing a new set of security...



Reports from current and former Target employees have validated claims made by hackers regarding the leaked internal systems data. The leaked source code and documentation shared...

Nvidia recently unveiled the Vera Rubin NVL72 at CES 2026, a revolutionary rack-scale platform that encrypts every bus across 72 GPUs, 36 CPUs, and the entire...
Subscribe to our weekly newsletter below and never miss the latest News or an exclusive offer.