


In the digital age, customer experience (CX) platforms play a crucial role in processing vast amounts of unstructured data. This includes survey responses, online reviews, social...



Suspected Chinese State-Backed Hackers Exploit Critical Dell Security Flaw A critical Dell security flaw has been quietly exploited by a suspected Chinese state-backed hacking group in...



Ransomware Threats Outpacing Defenses: The Growing Preparedness Gap The gap between ransomware threats and the defenses meant to stop them is widening, according to Ivanti’s 2026...
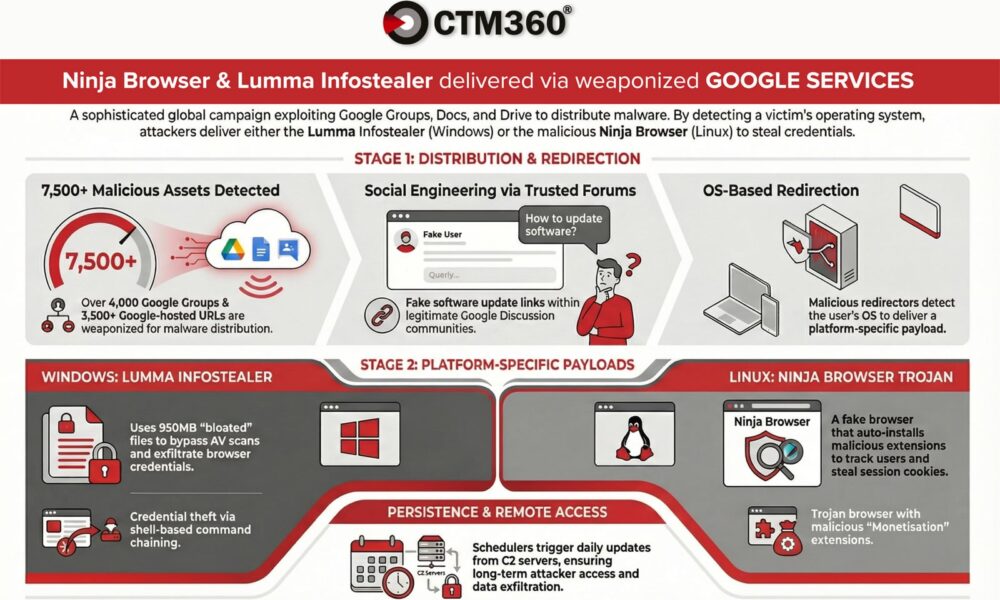

According to CTM360, a recent malware campaign is utilizing over 4,000 malicious Google Groups and 3,500 Google-hosted URLs to target organizations worldwide. Criminals are exploiting Google’s...



One Threat Actor Responsible for 83% of Recent Ivanti RCE Attacks Recent threat intelligence indicates that a single threat actor is behind the majority of active...



The Rising Threat of Identity and Access Management (IAM) Pivot Attacks A software developer receives a LinkedIn message from a recruiter offering a legitimate job opportunity....


Over 230 Malicious Skills Target OpenClaw Users with Data-Stealing Malware Recently, more than 230 malicious packages have surfaced for OpenClaw, an AI assistant previously known as...



Konni Hackers Target Blockchain Engineers with AI-Generated Malware The North Korean hacker group known as Konni, also identified as Opal Sleet and TA406, has been utilizing...



Protecting Against Ransomware Attacks: A Comprehensive Guide One of the key challenges with ransomware encryption is the failure to write the encrypted temporary key to the...



The Saudi-Led Acquisition of Electronic Arts Sparks Congressional Concerns A recent acquisition deal led by Saudi investors to acquire Electronic Arts has stirred up a wave...
Subscribe to our weekly newsletter below and never miss the latest News or an exclusive offer.