Security
Target Employees Verify Leaked Code Amid Heightened Git Security Measures

Reports from current and former Target employees have validated claims made by hackers regarding the leaked internal systems data. The leaked source code and documentation shared by a threat actor online have been confirmed to match real internal systems at Target.
Following BleepingComputer’s initial contact with Target about the alleged leak, the company swiftly implemented an “accelerated” security change that restricted access to Target’s Enterprise Git server. This change was communicated through internal channels a day after BleepingComputer’s inquiry.
Employee Validation of Leaked Materials
Recent reports have corroborated the authenticity of the leaked data related to Target’s internal CI/CD pipelines and infrastructure. Multiple sources with direct knowledge of Target’s internal systems have confirmed that the leaked data aligns with the company’s actual internal platforms and technology stack.

Former employees have identified internal system names, such as “BigRED” and “TAP [Provisioning],” mentioned in the leaked data, confirming their usage for cloud and on-premise application deployment at Target. Additionally, elements of the technology stack referenced in the leaked data, including Hadoop datasets, align with the systems used internally at Target.
Furthermore, the presence of proprietary project codenames and taxonomy identifiers in the leaked dataset, known internally as “blossom IDs,” indicates that the material reflects a genuine internal development environment rather than fabricated code.
If you are a Target employee or have any information regarding this event, please confidentially send us a tip online or via Signal at @axsharma.01.
Target’s Security Response
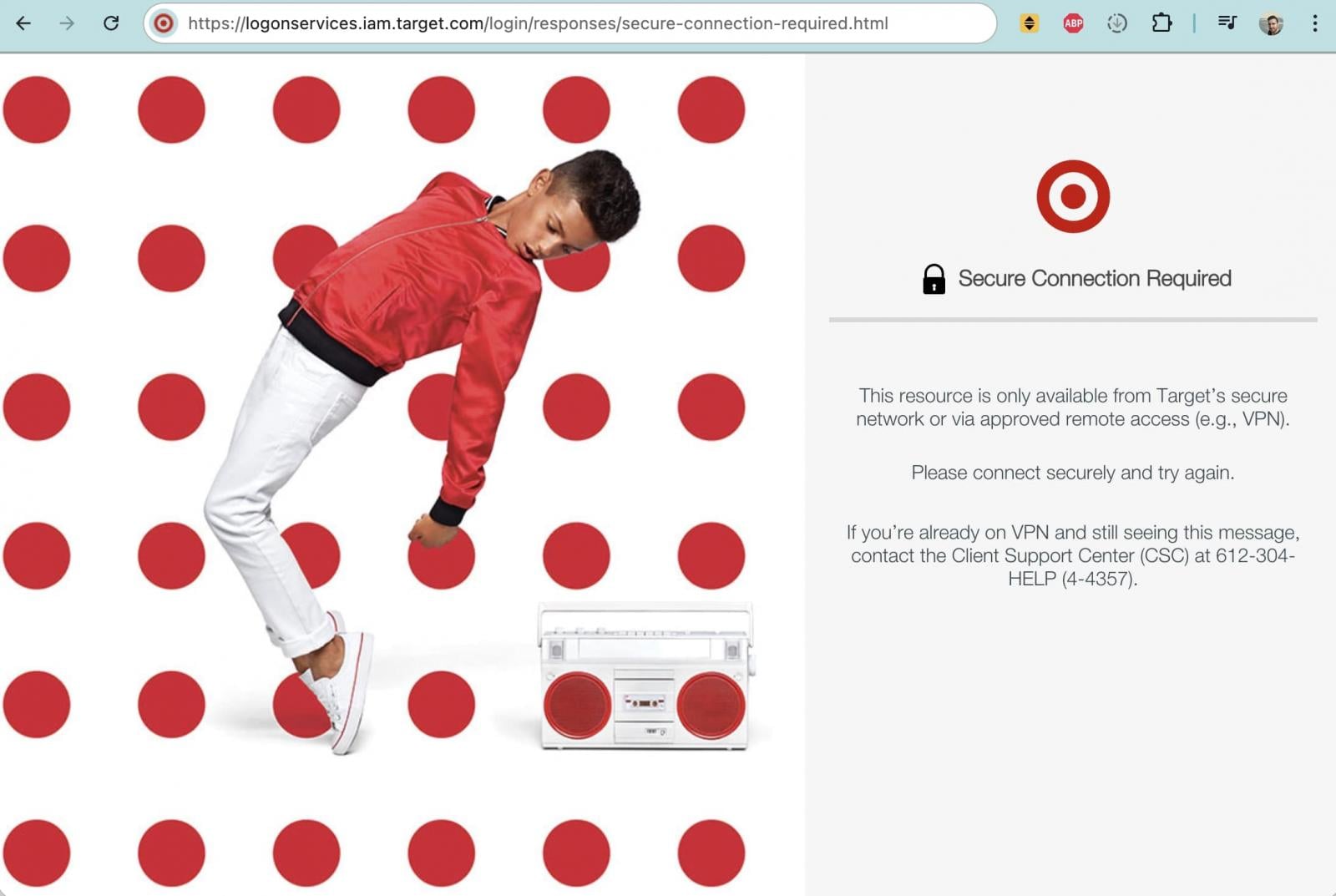
Following BleepingComputer’s contact, Target implemented an ‘accelerated’ security change, requiring access to git.target.com to be connected to a Target-managed network. This change aligns with the company’s approach to handling access to GitHub.com and signifies a lockdown of access to Target’s proprietary source code environment.
While git.target.com was previously accessible over the web, it is now only reachable from Target’s internal network or corporate VPN, indicating enhanced security measures to protect the company’s internal development resources.
Potential Data Breach Investigation
The origin of the leaked data remains unknown, with security researcher Alon Gal identifying a compromised Target employee workstation in late September 2025. The compromised workstation had extensive access to internal services, raising concerns about a potential insider involvement in the data leak.
While there is no direct confirmation linking the compromised workstation to the leaked source code for sale, threat actors often exfiltrate data for future monetization or leaks. The threat actor claims the dataset is approximately 860GB in size, with even a small sample confirming the presence of authentic internal code and system references.
BleepingComputer has provided Target with relevant repository links and offered to share threat-intelligence findings from Hudson Rock to aid in the investigation. Target has yet to respond to inquiries regarding a potential breach or insider involvement.

As the new year approaches, CISOs and security leaders are strategizing for the year ahead. Gain insights from over 300 top leaders on their planning, spending, and priorities for 2026. Download the report now to benchmark strategies and identify emerging trends in cybersecurity.
Discover how top leaders are translating investments into measurable impact.
Transform the following sentence into the passive voice:
“The company will announce the new product next week.”
The new product will be announced by the company next week.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS































