Security
The Evolving Need for Advanced Breach Monitoring Solutions
Authored by Ran Geva, Chief Executive Officer at Webz.io & Lunarcyber.com
2026 sees stolen credentials emerging as a top-tier concern in cybersecurity. Despite being acknowledged as a significant risk, many businesses still rely on generic tools and checkbox solutions to address this issue.
According to a recent survey conducted by Lunar, a dark-web monitoring platform powered by Webz.io, 85% of organizations consider stolen credentials to be a high or very high risk, with 62% ranking them among their top-three security priorities.
However, conversations with various organizations utilizing Lunar’s community platform reveal a common misconception. Statements like “we have MFA everywhere, so we’re covered” or “our EDR and zero-trust stack already protects our employees” reflect a lack of understanding that these measures do not offer complete protection when employees access critical SaaS services from unmanaged home devices.
The repercussions of failing to detect stolen credentials in a timely manner can be severe. According to IBM’s Cost of a Data Breach Report, a breach involving compromised credentials can cost between $4.81-4.88 million.
With Lunar observing 4.17 billion compromised credentials in 2025 alone, the potential global cost of these attacks is staggering. This underscores the fact that simple breach monitoring is no longer sufficient.
An organizational shift in mindset is crucial to establish a proactive defense strategy against the ever-evolving threat posed by infostealers.
The Pitfalls of Checkbox Monitoring and Generic Solutions
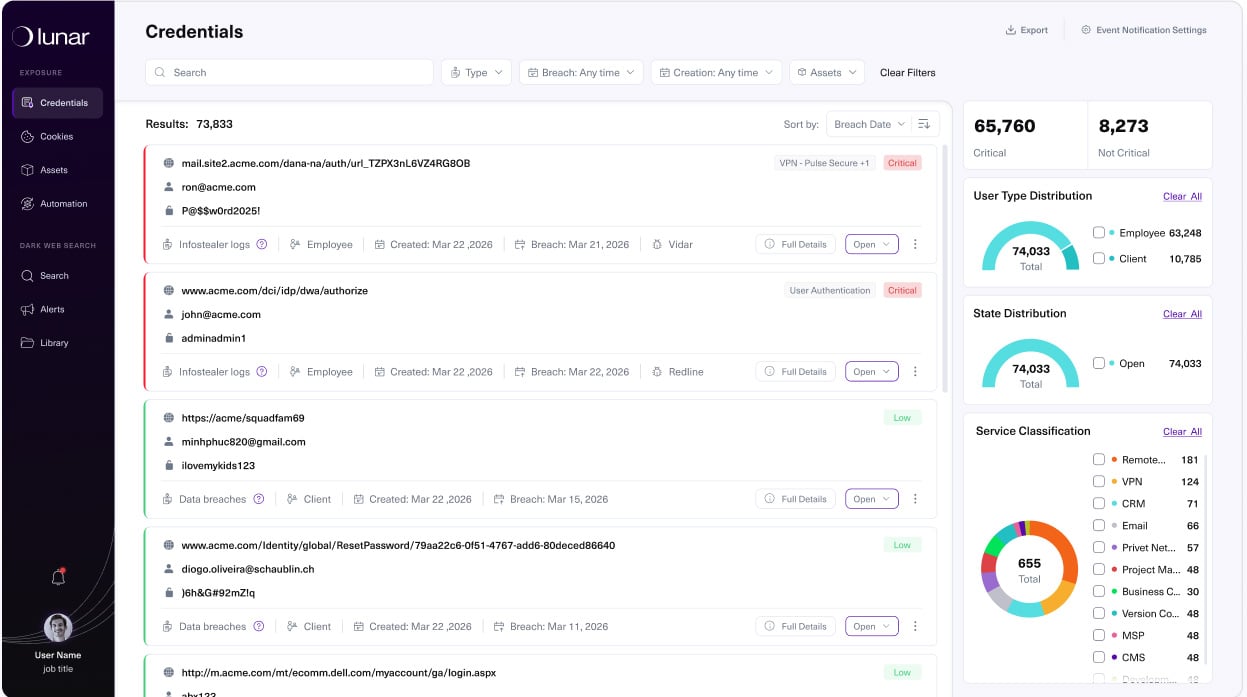
Prior to adopting Lunar, organizations often attempted to address the infostealer threat with inadequate solutions. These solutions typically focused on data breaches rather than infostealers, provided non-forensic infostealer data, had high latency and relied on stale data sources, and lacked automation, integrations, and investigation capabilities.
Research indicates that only 32% of surveyed enterprises utilize dedicated credential monitoring solutions, with 17% having no tools in place. Moreover, over 60% of organizations perform checks for exposed credentials on a monthly, infrequent, or nonexistent basis.
Upon transitioning to Lunar, many organizations are surprised to discover that their previous tools failed to provide the necessary forensic details to investigate breaches effectively. Key information such as compromised accounts, infected devices, impacted SaaS applications, and stolen session cookies was often missing.
While checkbox security is better than no security at all, it often lacks the depth required to effectively combat the infostealer threat. So, what impedes organizations from scaling their security operations?
Discover where your company’s credentials and session cookies are exposed.
Lunar offers continuous monitoring of breaches and infostealer logs for your domains, presenting actionable exposures in a free, enterprise-grade dashboard.
Sign Up for Free
Understanding the Extent of the Infostealer Threat
The infostealer paradox becomes evident in discussions surrounding the prevalence of exposed credentials. While the risks are known, organizations often struggle to allocate adequate budgets or identify effective solutions to mitigate the threat.
Furthermore, there is often a lack of awareness regarding the scale of credential theft, the targeted environments, and the accessed information. Analysis of 4.17 billion compromised-credential records from 2025 revealed that infostealers like LummaC2, Rhadamanthys, Vidar, Acreed, and others consistently evaded enterprise monitoring, even in supposedly mature environments.
Contrary to the belief that macOS is safer than Windows, the emergence of families like Atomic macOS Stealer (AMOS), Odyssey, MacSync, MioLab, and Atlas has startled many new Lunar users.
The data exfiltrated by infostealers extends beyond username/password pairs. With modern infostealers offered as comprehensive products with subscription tiers, dashboards, and documentation tailored to harvesting cookies, session tokens, and SaaS access at scale, organizations are now racing to enhance their defenses.
For threat actors, session cookies serve as more than just access credentials. They essentially provide unrestricted entry, allowing them to bypass login pages without encountering password prompts, MFA challenges, or leaving obvious traces in authentication logs.
This realization is now dawning on many organizations.
Anatomy of an Infostealer Attack
Deconstructing an infostealer attack and highlighting the inefficacy of checkbox security typically involves the following stages:
- Device Compromise: The victim’s device is infected by an infostealer delivered through various vectors such as zero-day exploits, ClickFix campaigns, rogue browser extensions, pirated software, game mods, or malicious open-source projects.
- Credential Extraction: The infostealer harvests browser logins and cookies, including those from third-party portals, and transmits them to the malware operator.
- Credential Monetization: The stolen credentials are aggregated into logs and traded on underground markets and private channels.
- Network Intrusion: The attacker who acquires the logs gains entry to the target network, including third-party portals, leveraging valid session tokens.
This entire sequence can unfold within hours. However, many organizations only conduct credential checks monthly or rely on outdated data sources.
By the time anomalies surface in legacy monitoring tools, attackers have already had ample time to explore and extract desired information.
Establishing a Robust Breach Monitoring Regimen
Organizations transitioning to a mature breach monitoring program equipped with tools to extract data from sources like stealer logs, Telegram groups, and marketplaces experience a paradigm shift. Instead of sporadic checks, they emphasize three critical capabilities:
- Continuous monitoring and standardization of key sources (breaches, stealer logs, combolists, marketplaces, and pertinent channels) to offer security teams a comprehensive and deduplicated view of breach exposures.
- Targeted automation to minimize false positives and noise, enabling analysts to focus on identities and sessions of genuine concern.
- Integration with existing security and identity frameworks (SIEM, SOAR, IDP) to execute end-to-end playbooks, promptly resetting credentials, revoking sessions, and blocking compromised accounts upon confirmed exposures.
Organizations leveraging Lunar witness a significant shift in approach once these elements are optimized. They treat the infostealer threat as a distinct domain with dedicated ownership, metrics, and playbooks, rather than managing breach monitoring through disparate tools.
At the core of Lunar’s mission is the provision of a free breach monitoring solution accessible to all organizations, irrespective of budget, delivering enterprise-grade coverage of compromised credentials, infostealers, and session cookies.
Redefining Breach Monitoring in 2026
Even seasoned security teams can fall into the breach monitoring paradox, where they acknowledge the threat but rely on periodic checks, MFA, and EDR as sufficient measures. However, in 2026, infostealers operate at a pace and scale that surpass the capabilities of checkbox monitoring solutions.
Elevating breach monitoring to a core program rather than a standalone product equips enterprises with the requisite visibility to detect compromised credentials wherever they surface, the context to interpret exposure implications, and the playbooks to automatically respond to detected attacks.
Explore how Lunar can aid in identifying your organization’s compromised credentials by availing free access.
Presented and authored by Lunar.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple6 months ago
Apple6 months agoMeta discontinues Messenger apps for Windows and macOS































