Security
The Importance of Strong Password Controls in Cybersecurity

During January of 2024, Microsoft experienced a security breach orchestrated by Russian hackers. This breach highlighted the vulnerability of passwords in even the most fortified security systems. It served as a stark reminder that passwords remain a critical aspect of network security, despite advancements in security tools.
The prevalence of password-related vulnerabilities continues to undermine the overall security of IT systems. Despite the introduction of advanced authentication technologies, passwords remain a primary target for attackers seeking to infiltrate corporate networks. As organizations navigate complex IT environments with on-premises servers, cloud platforms, and remote work setups, the importance of robust password controls becomes increasingly apparent.
Securing digital systems is akin to safeguarding a house with multiple entrances, each requiring a unique lock and set of keys for protection.
Identifying Weaknesses in Password Controls
Forgotten Accounts and Legacy Systems
Legacy accounts and forgotten entry points within digital infrastructure are akin to hidden spare keys left under old doormats. These overlooked access points, such as Windows Active Directory domains and specialized application accounts, pose significant security risks by providing easy entry for hackers into seemingly secure networks.
User Fatigue and Predictable Patterns
Users often struggle to manage a multitude of passwords, resorting to predictable patterns such as adding numbers or symbols to passwords for convenience. However, these common practices make passwords vulnerable to exploitation, as hackers can leverage leaked passwords to gain unauthorized access to corporate networks.
Verizon’s Data Breach Investigation Report revealed that stolen credentials are involved in nearly half of all data breaches. To address this issue, organizations should implement stringent password policies to mitigate security risks.
Implementing Effective Password Security Measures
Enhancing password security goes beyond mere checkbox compliance. Organizations must adopt intelligent and adaptable strategies to ensure robust protection. This entails moving beyond traditional complexity requirements and embracing dynamic password management approaches.
Enhanced Password Lists and Detection
Creating banned password lists that incorporate advanced pattern recognition and company-specific variations is crucial for bolstering security. These measures go beyond basic dictionary checks to identify subtle security risks and prevent the use of compromised passwords.
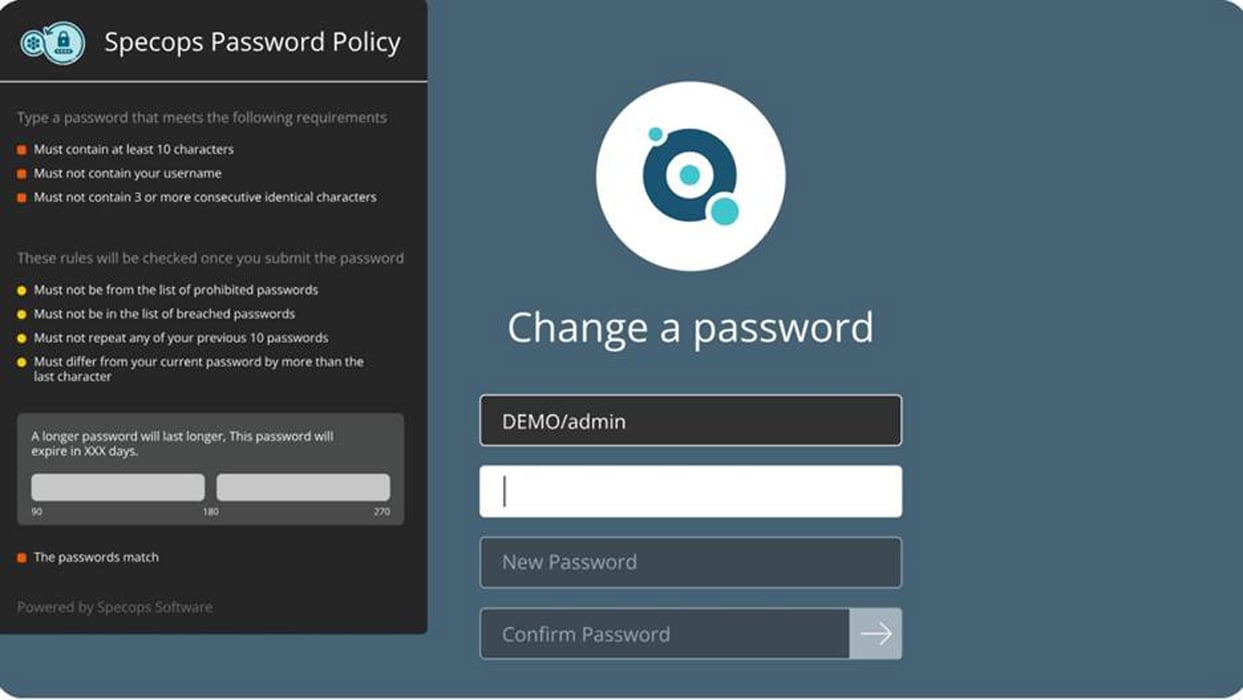
Intelligent Password History and Rotation
Traditional password rotation policies often lead to predictable password changes, diminishing security effectiveness. Organizations should implement nuanced rotation strategies that prevent password recycling without causing user frustration. The goal is to thwart attackers while ensuring user-friendly password practices.
Emphasizing Length and Memorability
Long, memorable passphrases offer superior security compared to cryptic, short passwords. By prioritizing length and memorability, organizations can enhance password strength and usability. This approach aligns with human behavior, making passwords easier to remember without compromising security.
Enforcing Password Policies Strategically
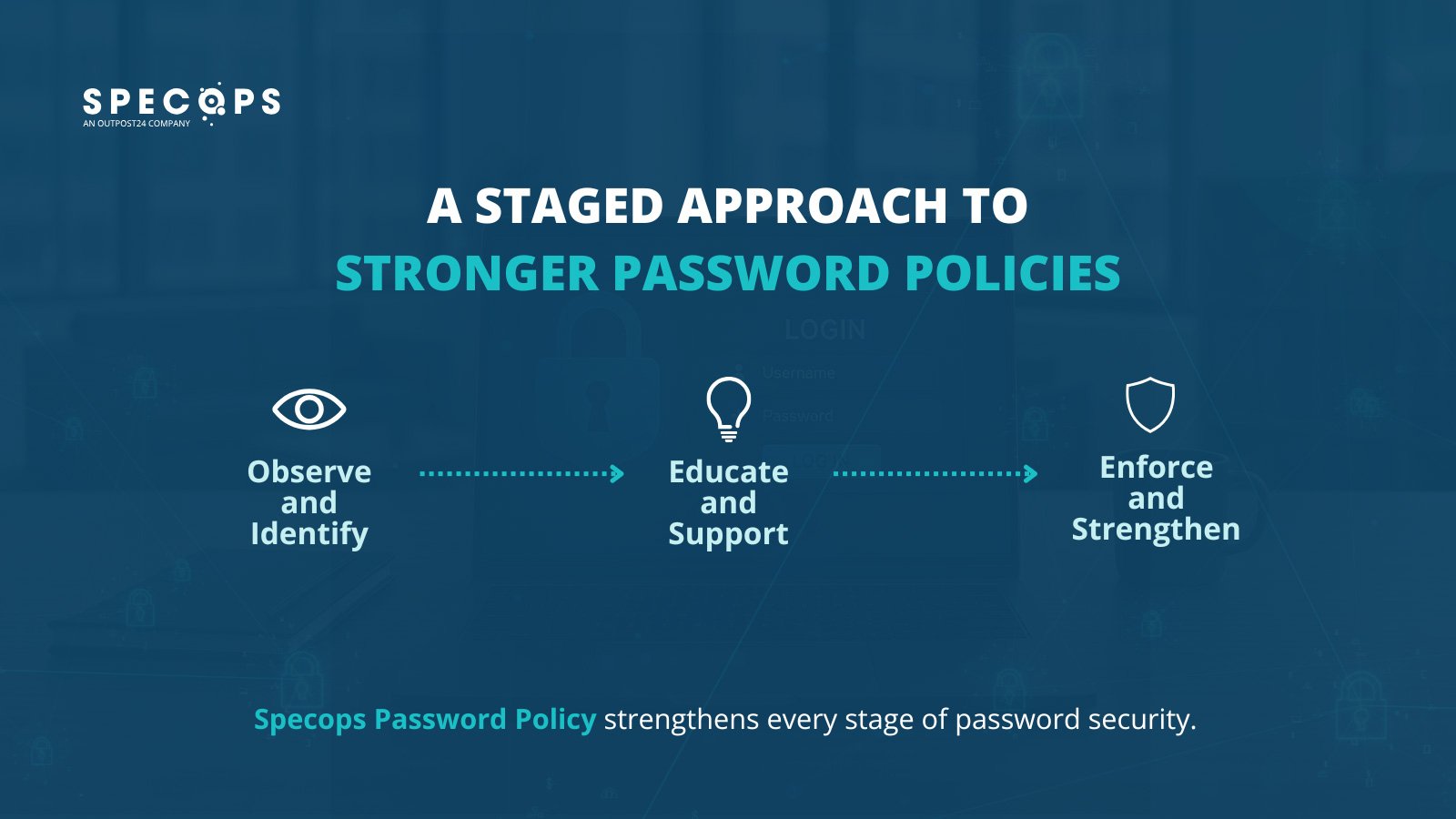
Enforcing password policies requires a blend of security strategy and psychology. Organizations should observe password usage patterns, provide guidance on potential weaknesses, and gradually implement mandatory changes with user support. It is essential to ensure that users perceive policy enforcement as a constructive measure rather than a punitive action.
Measuring the Effectiveness of Password Security Strategies
Evaluating the success of password security measures involves tracking key performance indicators (KPIs) such as the percentage of banned passwords detected, reduction in help desk password reset tickets, and the time required to address vulnerabilities. By analyzing these metrics, organizations can refine their password security approach and enhance overall protection.
Developing a 90-Day Password Security Plan
First 30 Days: Deep Dive and Discovery
Conduct a comprehensive assessment of password landscape, identify vulnerabilities, and analyze password complexity to establish a baseline. This phase involves running vulnerability scans and mapping out existing password practices.
Next 60 Days: Strategic Implementation
Implement new password strategies in incremental stages, starting with pilot groups in less sensitive departments. Provide training on password security best practices, educate users on the implications of weak passwords, and communicate policy changes effectively.
By following this structured approach, organizations can transform their password security strategy, creating adaptive defenses that evolve with the ever-changing threat landscape.
Embracing Password Security as a Continuous Priority
Despite evolving security technologies, passwords remain a fundamental aspect of authentication. By implementing intelligent and dynamic password controls, organizations can transform passwords from a security challenge into a resilient defense mechanism. This shift requires a shift in mindset, viewing password security as an ongoing strategy rather than a one-time fix.
To simplify password policy management and enhance security, consider utilizing tools like Specops Password Policy. This solution offers instant password feedback, blocks compromised passwords, and streamlines Active Directory security.
Contact us for a live demonstration today.
Contributed by Specops Software
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS