Security
Uncovering the Claude Code Leak: How Infostealer Malware is Being Spread on GitHub
Exploiting the Claude Code Leak: Fake GitHub Repositories Spreading Vidar Malware
Recent developments in the cybersecurity landscape have revealed a concerning trend where threat actors are leveraging the Claude Code source code leak to propagate the Vidar information-stealing malware. Claude Code, an AI agent developed by Anthropic, was inadvertently exposed on March 31 due to a JavaScript source map error, unveiling critical details about the tool’s functionalities and internal workings.
The inadvertent disclosure included a massive 513,000 lines of unobfuscated TypeScript code spread across 1,906 files, shedding light on the agent’s orchestration logic, permissions, hidden features, and security-related internals. This breach led to a surge in downloads and GitHub publications, with users unknowingly spreading the leaked code further.
Cloud security experts at Zscaler have identified malicious activities stemming from the Claude Code leak, particularly the distribution of the Vidar infostealer through fake GitHub repositories. One such repository, attributed to user “idbzoomh,” masqueraded as a legitimate leak offering enterprise features without usage restrictions, ultimately luring unsuspecting users into downloading malware.
Source: Zscaler
To maximize traffic to the deceptive repository, the threat actor optimized it for search engines, ensuring it ranked high in search results for queries related to the leaked Claude Code. This SEO strategy aimed to attract users seeking the exposed code, unwittingly leading them to download a malicious payload.
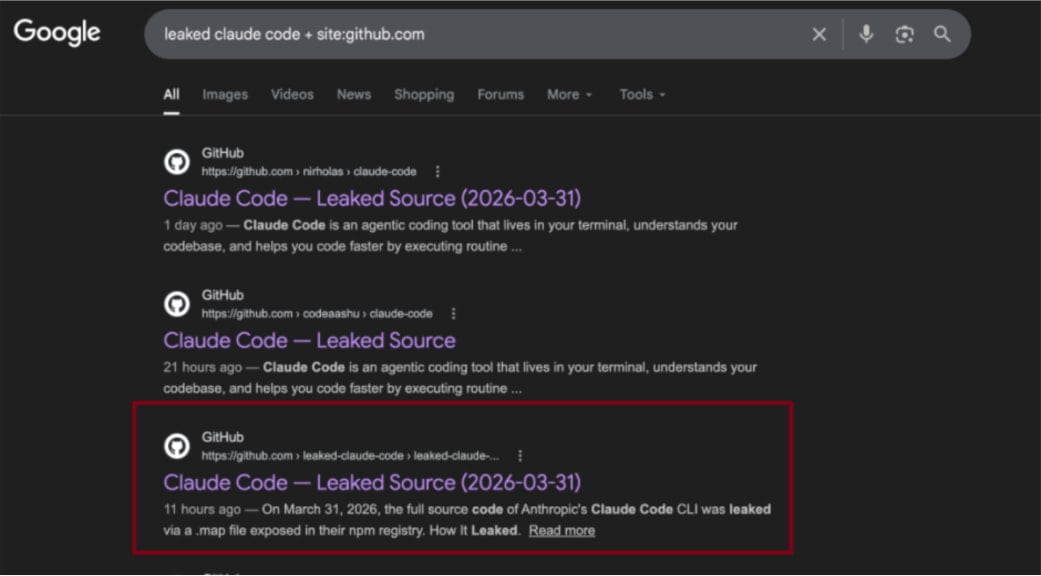
Source: Zscaler
Upon downloading a disguised 7-Zip archive containing a Rust-based executable named ClaudeCode_x64.exe, users inadvertently trigger the deployment of Vidar and the GhostSocks network traffic proxying tool. Zscaler’s investigation further revealed that the malicious archive undergoes frequent updates, potentially introducing new payloads in subsequent versions.
Additionally, a second GitHub repository mirroring the initial code leak was discovered, featuring a non-functional ‘Download ZIP’ button. This repository, believed to be managed by the same threat actor, suggests experimentation with alternative delivery mechanisms.
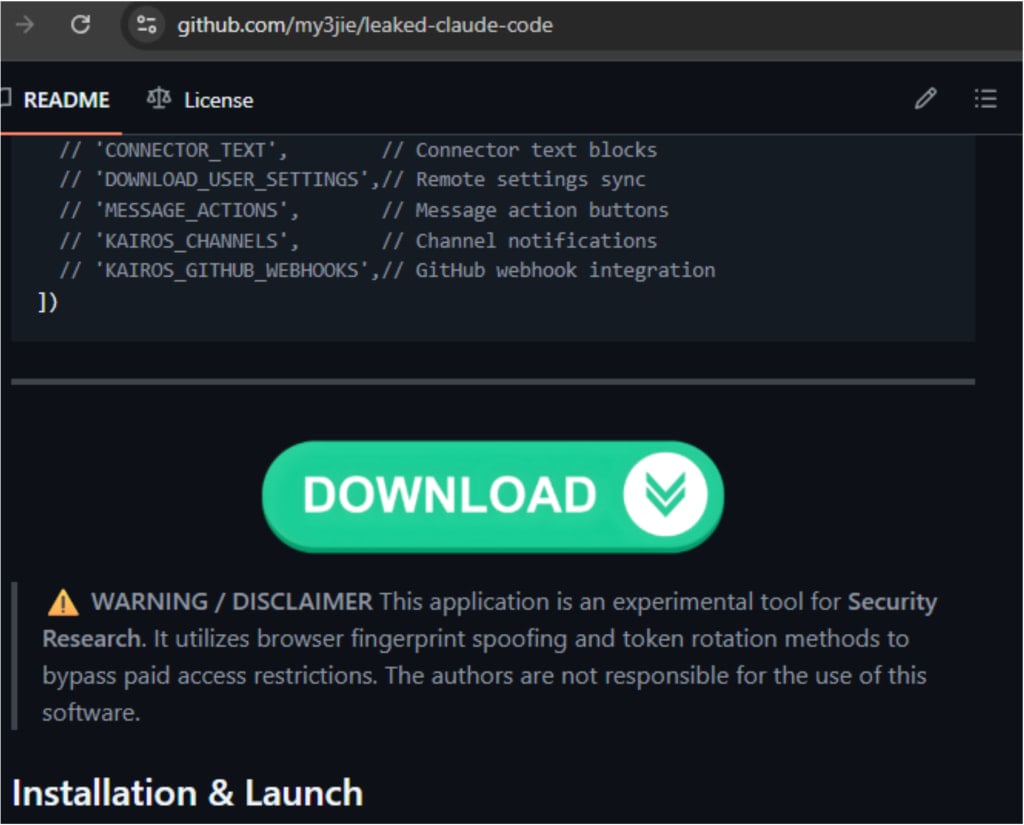
Source: Zscaler
Despite GitHub’s security measures, malicious actors have persistently exploited the platform to disseminate harmful payloads under the guise of legitimate content. Past instances have seen threat actors targeting unsuspecting individuals with repositories falsely claiming to offer proof-of-concept exploits for recent vulnerabilities.
This incident underscores the opportunistic nature of cyber threats, with bad actors quick to capitalize on high-profile events to achieve malicious objectives. As the cybersecurity landscape evolves, vigilance and caution are paramount in navigating the digital realm.

Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS


























