Security
Unmasking the Latest Tactic of Facebook Login Thieves: The Browser-in-Browser Trick
Facebook Login Thieves Increasingly Use Browser-in-Browser Trick
Hackers have been resorting to the browser-in-the-browser (BitB) technique to deceive users into divulging their Facebook account details. This method, developed by security researcher mr.d0x in 2022, has been adopted by cybercriminals targeting various online platforms, including Facebook and Steam.
Research conducted by Trellix indicates that threat actors steal Facebook accounts to perpetrate scams, gather personal information, or engage in identity fraud. With over three billion active users, Facebook remains a prime target for fraudulent activities.
The BitB Phishing Technique
In a BitB attack, users visiting attacker-controlled websites encounter a fake browser pop-up containing a login form. This pop-up is created using an iframe that mimics the authentication interface of legitimate platforms, making the deception harder to detect.
Trellix reports that recent phishing campaigns targeting Facebook users impersonate law firms alleging copyright infringement, threatening immediate account suspension, or sending Meta security notifications regarding unauthorized logins.
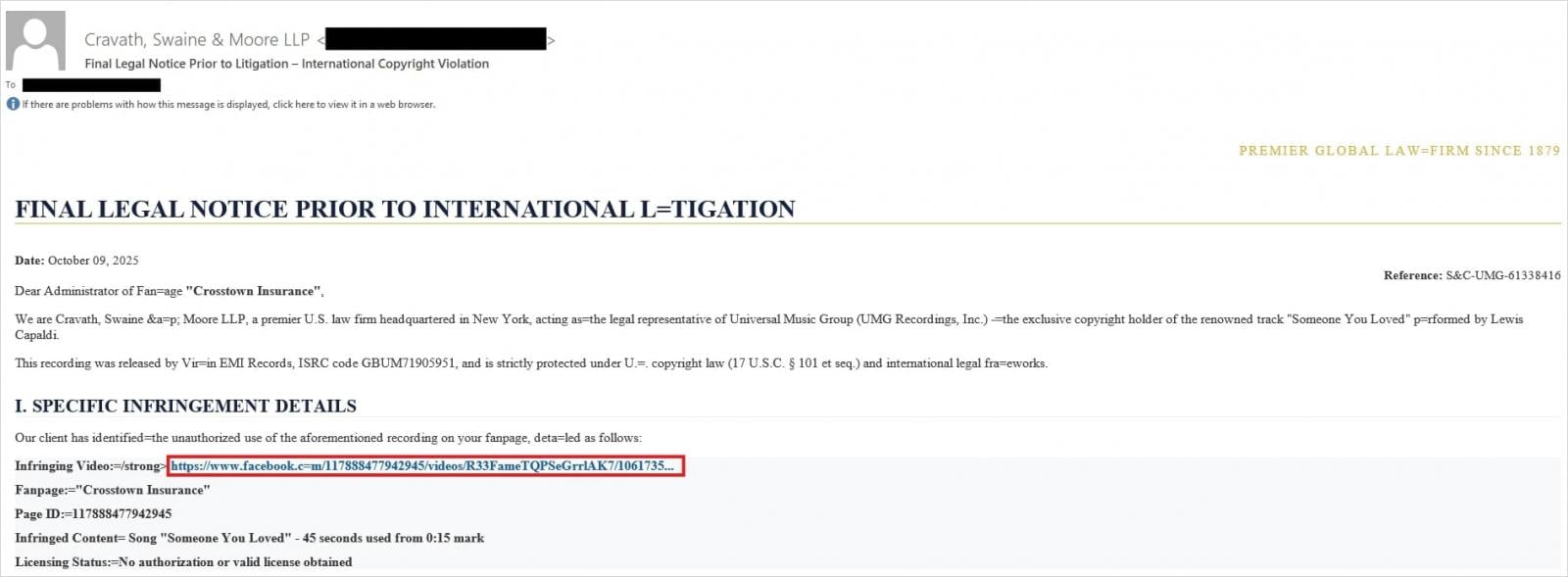
Source: Trellix
To evade detection and enhance credibility, cybercriminals have incorporated shortened URLs and fake Meta CAPTCHA pages. Ultimately, victims are coerced into entering their Facebook credentials in a bogus pop-up window.
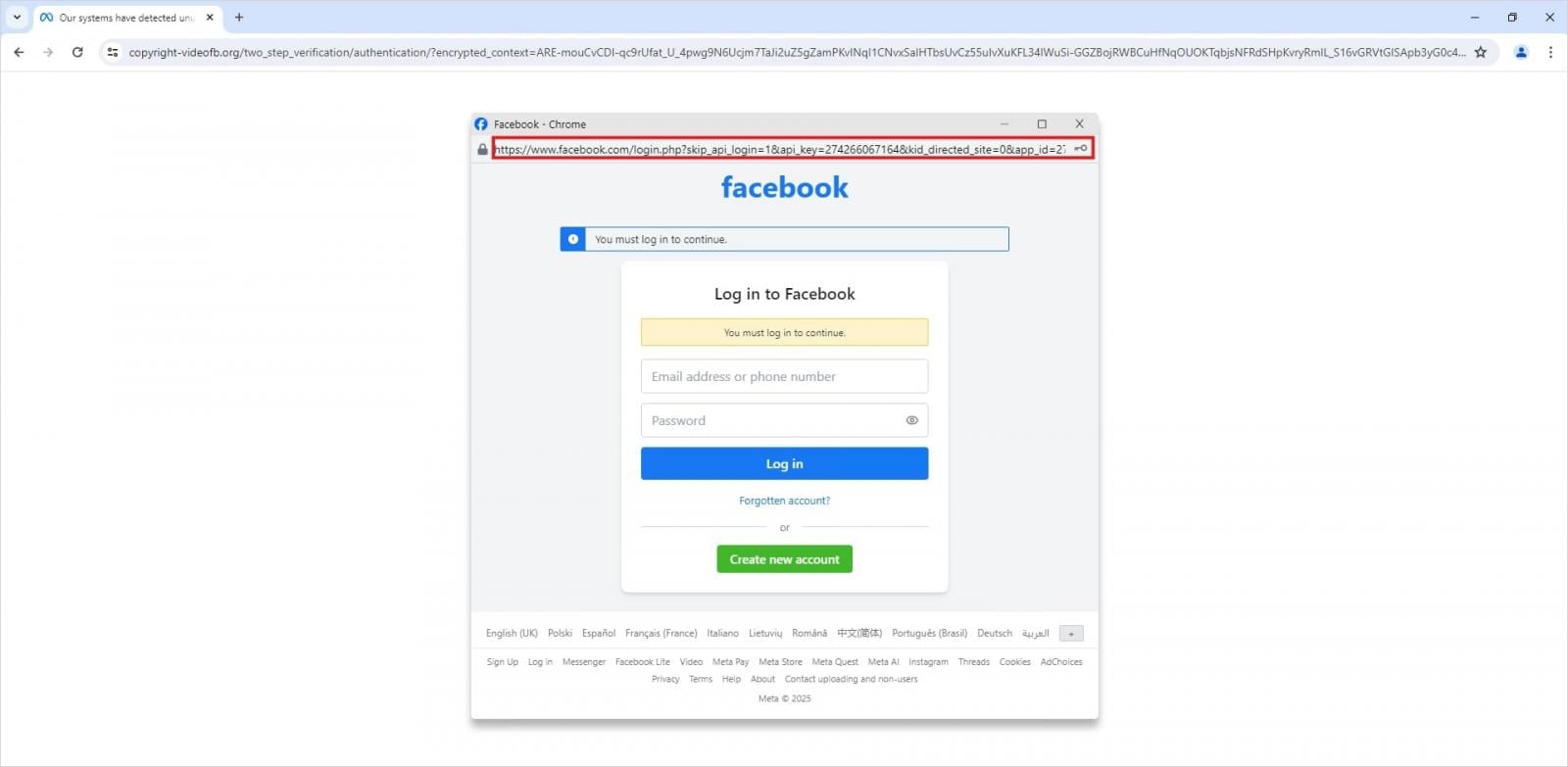
Source: Trellix
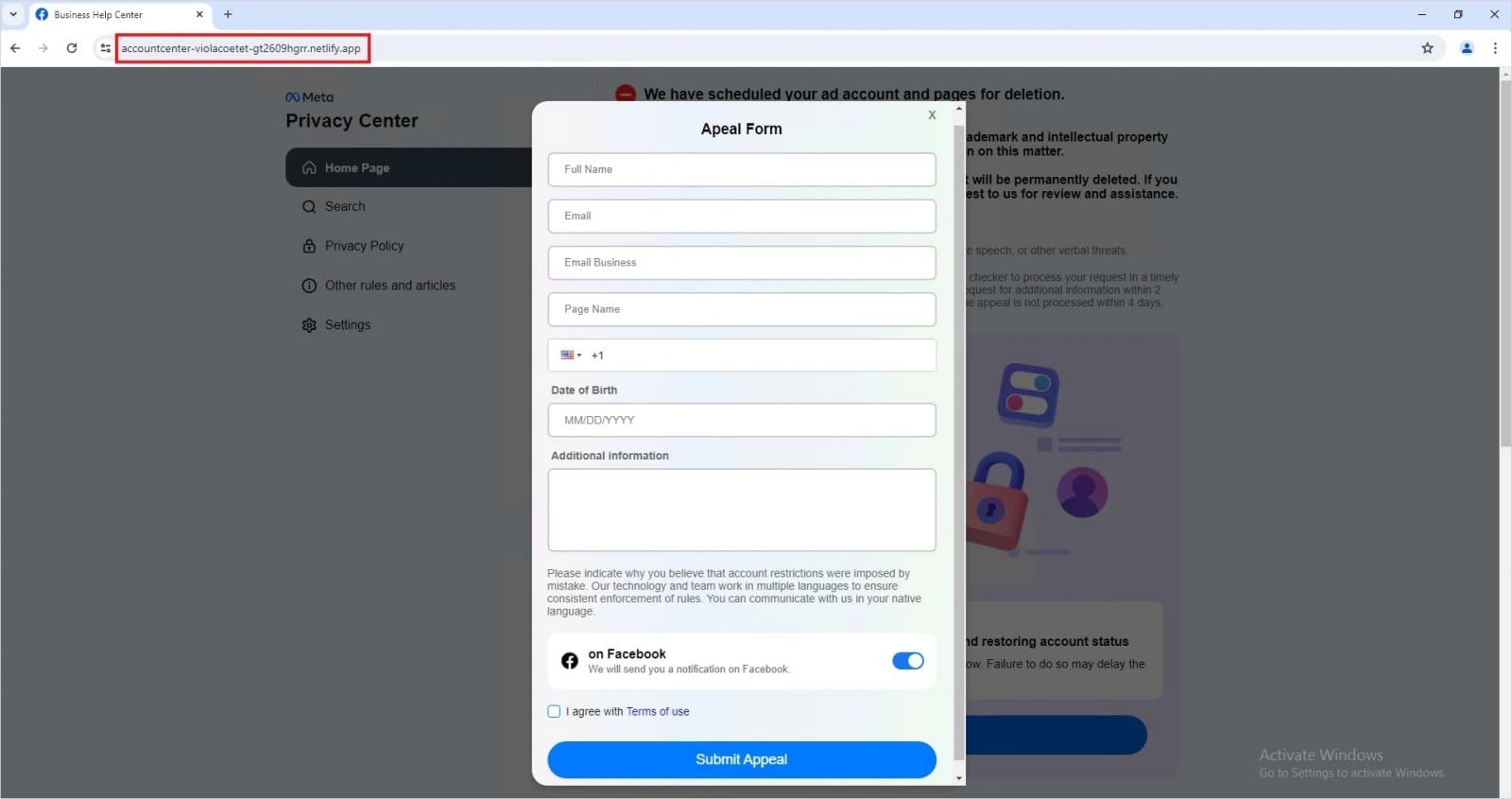
Additionally, Trellix has identified numerous phishing pages hosted on reputable cloud platforms like Netlify and Vercel. These pages imitate Meta’s Privacy Center portal, redirecting users to forms disguised as appeals that illicitly collect personal data.
Source: Trellix
These campaigns represent a significant advancement compared to conventional Facebook phishing schemes. The abuse of trusted infrastructure, such as legitimate cloud hosting services and URL shorteners, aids fraudsters in circumventing security measures and instilling a false sense of security in their phishing pages.
The emergence of the Browser-in-the-Browser technique marks a substantial escalation in phishing tactics. By creating a custom fake login pop-up window within the victim’s browser, this method leverages users’ familiarity with authentication processes, making credential theft visually undetectable.
Protecting Against BitB Attacks
When users receive security alerts or infringement notifications, it is advisable to navigate to the official URL in a separate tab instead of clicking embedded links in emails. When prompted to enter credentials in login pop-ups, it is essential to check if the window can be moved outside the browser window, as iframes used in the BitB trick are confined to the underlying window.
Enabling two-factor authentication is a general recommendation for bolstering the security of online accounts. While not foolproof, this feature adds an extra layer of protection against unauthorized access, even if credentials are compromised.

Whether you’re managing old keys or implementing safeguards for AI-generated code, this guide assists your team in building secure systems from the ground up.
Download the cheat sheet to simplify secrets management.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS