Security
Defending Canadian Payrolls: Fighting Back Against Payroll Pirates

The Rise of Storm-2755: Canadian Employees Targeted in Payroll Pirate Attacks
Storm-2755, a financially motivated threat actor, has been causing havoc by stealing Canadian employees’ salary payments through payroll redirection attacks. These attacks, also known as payroll pirate attacks, involve hijacking accounts to redirect funds for malicious purposes.
The modus operandi of the attackers involves using fake Microsoft 365 sign-in pages to steal authentication tokens and session cookies from victims. By redirecting them to malicious domains hosting fake Microsoft 365 sign-in forms, such as bluegraintours[.]com, the attackers can bypass multifactor authentication (MFA) through adversary-in-the-middle (AiTM) attacks.
Microsoft has highlighted the sophistication of AiTM attacks, which proxy the entire authentication flow in real-time to capture session cookies and OAuth access tokens. These tokens allow threat actors to gain access to Microsoft services without being prompted for credentials, bypassing traditional MFA protections.
The attackers, once inside an employee’s account, create inbox rules to hide messages from HR staff containing keywords like “direct deposit” or “bank.” This prevents victims from seeing crucial correspondence, paving the way for further manipulation.
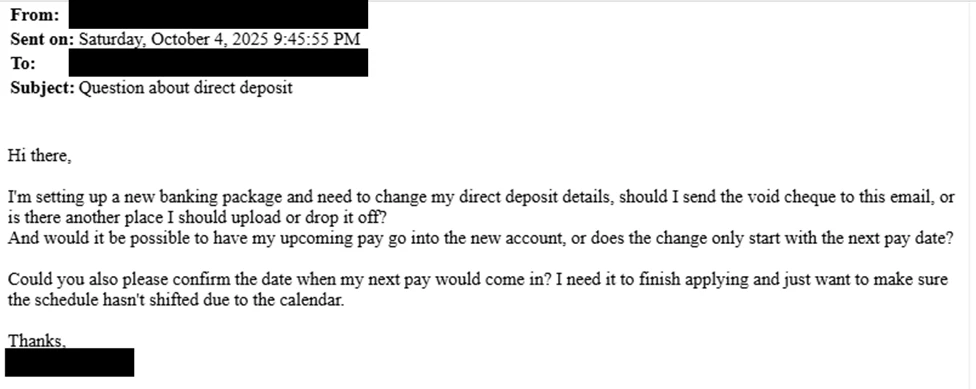
In a clever ploy, the attackers then send emails to HR staff under the guise of “Question about direct deposit” to trick them into updating banking information. If social engineering tactics fail, the attackers resort to logging into HR software platforms like Workday using stolen sessions to manually update information.
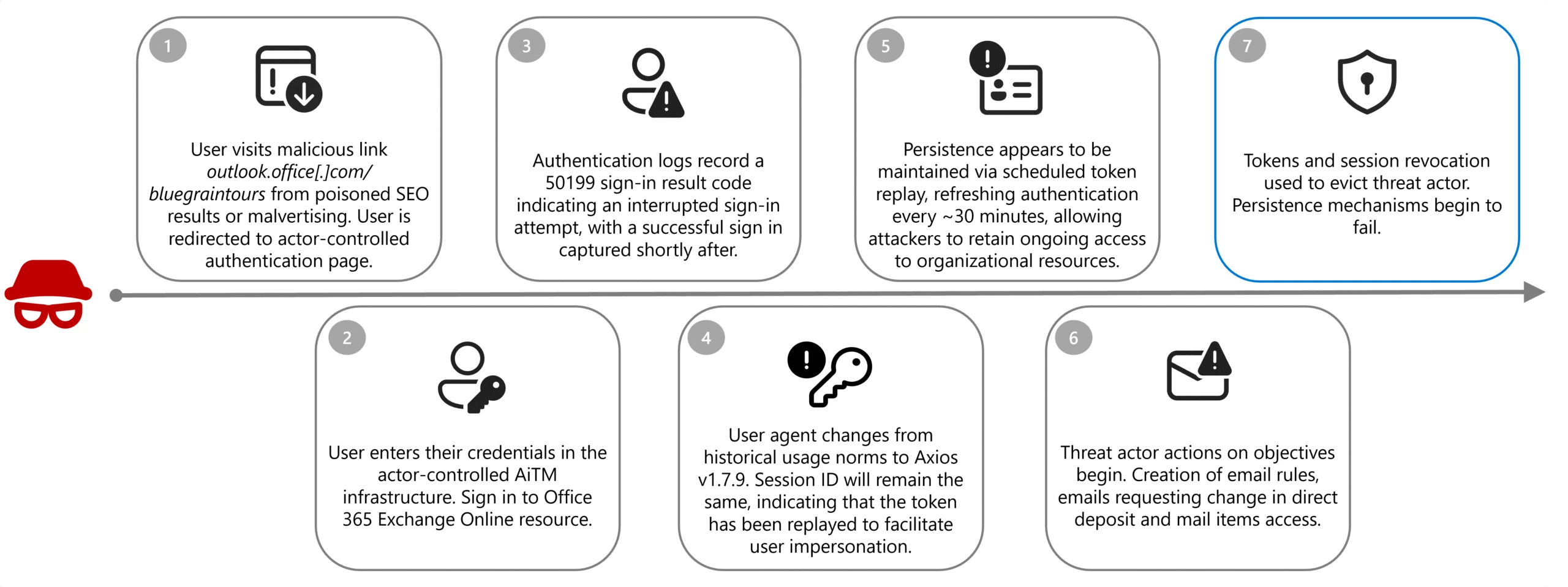
To counter AiTM and payroll pirate attacks, Microsoft recommends blocking legacy authentication protocols and implementing phishing-resistant MFA. Additionally, immediate action should be taken upon detecting signs of compromise, including revoking compromised tokens, removing malicious inbox rules, and resetting MFA credentials for affected accounts.
Continued Threat: Storm-2657 and Payroll Pirate Campaigns
In a similar vein, Storm-2657 targeted university employees in the United States in pirate payroll campaigns. By breaching accounts through phishing emails and using AiTM tactics to steal MFA codes, the threat actors compromised victims’ Exchange Online accounts.
Payroll pirate attacks are a subset of business email compromise (BEC) scams that specifically target entities involved in wire transfers. The FBI’s Internet Crime Complaint Center (IC3) has recorded a significant rise in BEC fraud complaints, with losses exceeding $3 billion, making it a lucrative crime type.
Enhancing Defenses and Mitigating Risks
Organizations must prioritize cybersecurity measures to protect against AiTM and payroll pirate attacks. Implementing robust security protocols, such as blocking legacy authentication and deploying phishing-resistant MFA, is crucial in safeguarding sensitive information.
Immediate response to any compromise is essential, including revoking compromised tokens, removing malicious rules, and resetting credentials. By staying vigilant and proactive, organizations can mitigate the risks posed by sophisticated cyber threats.
Conclusion
As cyber threats evolve and become more sophisticated, organizations must adapt their security strategies to combat emerging risks. By understanding the tactics employed by threat actors like Storm-2755 and Storm-2657, businesses can fortify their defenses and protect against financial losses and data breaches.

Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
-

 Facebook8 months ago
Facebook8 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple8 months ago
Apple8 months agoMeta discontinues Messenger apps for Windows and macOS





























