Security
Exploiting Critical Marimo RCE Vulnerability: A Call to Action

Shortly after the public disclosure of a critical vulnerability in the Marimo open-source reactive Python notebook platform, hackers wasted no time and began exploiting it within just 10 hours.
The vulnerability in question allows for remote code execution without the need for authentication in Marimo versions 0.20.4 and earlier. This vulnerability, known as CVE-2026-39987, has been deemed critical by GitHub, scoring a 9.3 out of 10.
According to researchers at Sysdig, a cloud-security company, attackers swiftly developed an exploit based on the developer’s advisory and promptly launched attacks aimed at extracting sensitive information.

Marimo serves as an open-source Python notebook environment commonly utilized by data scientists, ML/AI practitioners, researchers, and developers involved in creating data apps or dashboards. With 20,000 GitHub stars and 1,000 forks, Marimo is a well-received project within the tech community.
The root cause of CVE-2026-39987 lies in the WebSocket endpoint ‘/terminal/ws,’ which exposes an interactive terminal lacking proper authentication checks, thereby allowing connections from any unauthenticated client.
This vulnerability essentially grants direct access to a full interactive shell, operating with the same privileges as the Marimo process.
Marimo officially disclosed the flaw on April 8 and subsequently released version 0.23.0 as a corrective measure. Users who deployed Marimo as an editable notebook or exposed it to a shared network using ‘–host 0.0.0.0’ while in edit mode are particularly at risk.
Exploitation in the Wild
Within the initial 12 hours post-disclosure, Sysdig noted 125 IP addresses engaging in reconnaissance activities associated with the vulnerability.
Less than 10 hours after the disclosure, the researchers observed the first exploitation attempt, specifically in a credential theft operation.
The attacker verified the vulnerability by connecting to the ‘/terminal/ws’ endpoint and executing a scripted sequence to confirm remote command execution before swiftly disconnecting.
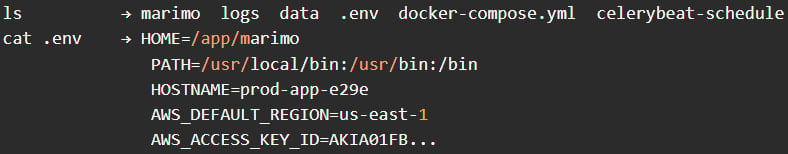
Following this validation, the attacker engaged in manual reconnaissance, issuing basic commands like pwd, whoami, and ls to gain insights into the environment, followed by attempts at directory navigation and checks for SSH-related locations.
The attacker then shifted focus to credential harvesting, targeting the .env file to extract environment variables, cloud credentials, and application secrets. Subsequently, further attempts were made to access additional files in the working directory and probe for SSH keys.
Source: Sysdig
According to a recent Sysdig report, the entire phase of credential access was completed in under three minutes.
Approximately an hour later, the attacker returned for a second exploitation session utilizing the same exploit sequence. The researchers identified the attacker as a methodical operator with a hands-on approach, focusing on high-value objectives like stealing .env credentials and SSH keys.
Interestingly, the attackers refrained from deploying persistence mechanisms, cryptominers, or backdoors, indicating a swift and stealthy operation.
Marimo users are strongly advised to upgrade to version 0.23.0 promptly, monitor WebSocket connections to ‘/terminal/ws,’ restrict external access using a firewall, and rotate all exposed secrets. If upgrading is not feasible, it is recommended to block or disable access to the ‘/terminal/ws’ endpoint altogether.

Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
-

 Facebook8 months ago
Facebook8 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple8 months ago
Apple8 months agoMeta discontinues Messenger apps for Windows and macOS































