Security
Bitrefill Points Finger at North Korean Lazarus Group in Cyberattack Investigation

Cyberattack on Bitrefill Linked to North Korean Lazarus Group
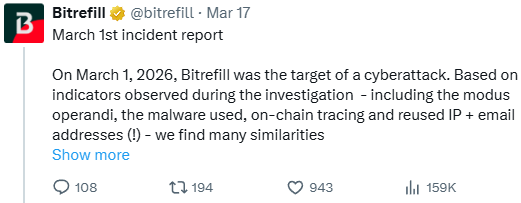
Bitrefill, a popular crypto-powered gift card store, recently disclosed that the cyberattack it experienced was likely orchestrated by North Korean hackers affiliated with the Bluenoroff group.
Through their investigation, Bitrefill identified several indicators that closely resembled previous attacks attributed to the North Korean threat actor, such as tactics, malware, IP addresses, and email addresses.
The company stated, “Based on indicators observed during the investigation – including the modus operandi, the malware used, on-chain tracing, and reused IP + email addresses (!) – we find many similarities between this attack and past cyberattacks by the DPRK Lazarus / Bluenoroff group against other companies in the crypto industries.”
Bitrefill serves as a mid-sized e-commerce platform that allows users to purchase gift cards using cryptocurrency for various stores in over 150 countries. These gift cards can be redeemed for a wide range of products and services, including clothing, food, groceries, health and beauty items, bills, transportation, electronics, and more.
The platform supports over 600 mobile operators and numerous global brands, catering to a wide customer base.
On March 1st, Bitrefill initially reported technical difficulties affecting its website and app. Subsequently, the company identified a security issue and temporarily suspended all services.
While user balances remained unaffected, the process of restoring all services is still ongoing.
The breach was detected after Bitrefill noticed irregularities in supplier purchases, manipulation of gift card inventory, and unauthorized transactions from certain wallets.
An investigation revealed that the attack originated from an employee’s compromised laptop, where legacy credentials were stolen and utilized to access sensitive information within the company’s infrastructure.
Approximately 18,500 purchase records, including customer email addresses, IP addresses, and cryptocurrency payment details, were exposed during the breach. For 1,000 transactions, customer names were also compromised.
Although the exposed information was encrypted, Bitrefill acknowledged the possibility that the attackers may have obtained decryption keys.
Despite labeling it as the most severe cyberattack in its ten-year history, Bitrefill managed to mitigate the impact with minimal losses, covered by its capital.
It was determined that the attackers were primarily interested in cryptocurrency and gift card inventory rather than customer data.
BlueNoroff, also known as APT38, is a subgroup of the Lazarus group specializing in targeting financial institutions, particularly within the cryptocurrency sector, with the goal of stealing digital assets.
Bitrefill emphasized the importance of enhancing security measures, including regular security reviews, penetration testing, access controls, logging, monitoring, and automated shutdown protocols to prevent future incidents.
Most of Bitrefill’s services have returned to normal operations, and customers are advised to remain vigilant when receiving communications.

Malware is evolving. The Red Report 2026 delves into how new threats leverage mathematics to evade detection and camouflage themselves.
Access our analysis of 1.1 million malicious samples to uncover the top 10 techniques and evaluate the efficacy of your security measures.
-

 Facebook5 months ago
Facebook5 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook5 months ago
Facebook5 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook3 months ago
Facebook3 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook3 months ago
Facebook3 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook5 months ago
Facebook5 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook3 months ago
Facebook3 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple5 months ago
Apple5 months agoMeta discontinues Messenger apps for Windows and macOS